Top 10 Docker Container Security Best Practices With Tutorial
Top 10 Docker Container Security Best Practices With Tutorial Studique 10 best practices to containerize node.js web applications with docker if you’re a node.js developer you are going to love this step by step walkthrough, showing you how to build performant and secure docker base images for your node.js applications. By educating your team about docker security best practices, you can ensure that they understand the importance of security and are able to take steps to keep your docker environment secure.
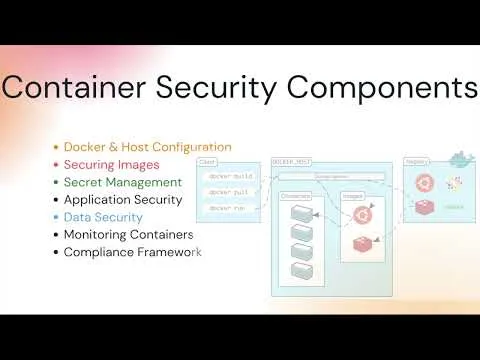
Docker Container Security Best Practices For Modern Applications Wiz Learn 14 docker best practices to ensure that your deployments are robust, resilient, and ready to meet the challenges of modern security threats. Discover the top 10 docker container security best practices with this comprehensive tutorial! learn how to ensure the security of your docker files and compose with speed and efficiency. Discover the top 10 docker container security best practices with this comprehensive tutorial! learn how to ensure the security of your docker files and compose with speed and efficiency. Container security involves implementing a robust set of practices and tools to protect the entire container lifecycle, from the underlying infrastructure to the applications running within them.

Docker Container Security Best Practices For Modern Applications Wiz Discover the top 10 docker container security best practices with this comprehensive tutorial! learn how to ensure the security of your docker files and compose with speed and efficiency. Container security involves implementing a robust set of practices and tools to protect the entire container lifecycle, from the underlying infrastructure to the applications running within them. Securing your docker containers requires a multi faceted approach. by following the 10 best practices outlined above, you can ensure that your containers are secure and protected against potential vulnerabilities that could compromise your data and systems. By following the top 10 docker security best practices outlined in this post, you can significantly reduce the risk of docker based attacks and ensure a secure environment for your applications. Tl;dr: master docker security best practices with this actionable cheat sheet. learn how to secure images, enforce least privilege, manage secrets, restrict resource usage, and harden network and registry configurations. avoid common pitfalls like exposed credentials and untrusted images. This guide cuts through the noise and provides a definitive list of the most impactful docker security best practices for hardening your containerized environments.

Docker Container Security Best Practices For Modern Applications Wiz Securing your docker containers requires a multi faceted approach. by following the 10 best practices outlined above, you can ensure that your containers are secure and protected against potential vulnerabilities that could compromise your data and systems. By following the top 10 docker security best practices outlined in this post, you can significantly reduce the risk of docker based attacks and ensure a secure environment for your applications. Tl;dr: master docker security best practices with this actionable cheat sheet. learn how to secure images, enforce least privilege, manage secrets, restrict resource usage, and harden network and registry configurations. avoid common pitfalls like exposed credentials and untrusted images. This guide cuts through the noise and provides a definitive list of the most impactful docker security best practices for hardening your containerized environments.

Container Security Best Practices With Docker Secopera Tl;dr: master docker security best practices with this actionable cheat sheet. learn how to secure images, enforce least privilege, manage secrets, restrict resource usage, and harden network and registry configurations. avoid common pitfalls like exposed credentials and untrusted images. This guide cuts through the noise and provides a definitive list of the most impactful docker security best practices for hardening your containerized environments.
Comments are closed.