Top 10 Bluetooth Threats Techyv

Top 10 Bluetooth Threats Techyv Learn about the top 10 bluetooth threats and how to protect your devices from potential attacks. keep your information safe with these tips and tricks. Hackers can exploit bluetooth to steal data, spy, or take control of your devices. learn about these threats and 18 essential tips to keep your connections secure.
Top 10 Bluetooth Threats Techyv Although bluetooth is extremely convenient for short range wireless data transfers, it also has several security risks if not configured and used securely. Bluetooth technology improves convenience but brings hidden security risks. learn about bluetooth vulnerabilities and effective steps to safeguard it. The existing bluetooth security has been extensively scrutinized and checked in recent years, and several researchers analyzed and tested bluetooth security and raised concerns about its reliability. this study seeks to the security vulnerabilities and threats in bluetooth embedded devices. Learn about vulnerability in bluetooth, how hackers exploit it, real world attacks, and best practices to secure devices and enterprise networks.

Top 10 Bluetooth Threats Techyv The existing bluetooth security has been extensively scrutinized and checked in recent years, and several researchers analyzed and tested bluetooth security and raised concerns about its reliability. this study seeks to the security vulnerabilities and threats in bluetooth embedded devices. Learn about vulnerability in bluetooth, how hackers exploit it, real world attacks, and best practices to secure devices and enterprise networks. In this article we are going to discuss about some of the risks posed by bluetooth devices and some of the types of bluetooth device threats in our daily life and how the attack will work. I had previously written about surveying the trend of bluetooth vulnerabilities back in 2021 [1]. as roughly a year or so has passed, it was a timely moment to review how things may have evolved with respect to the vulnerabilities discovered. In this comprehensive field guide, you‘ll not only learn how bluetooth attacks work on a technical level, but also simple best practices to lock down your connections without sacrificing convenience. Bluetooth technology, which facilitates wireless communication between billions of devices including smartphones, tablets, laptops, and internet of thing (iot).
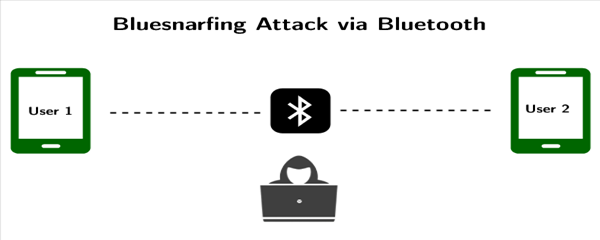
Top 10 Bluetooth Threats Techyv In this article we are going to discuss about some of the risks posed by bluetooth devices and some of the types of bluetooth device threats in our daily life and how the attack will work. I had previously written about surveying the trend of bluetooth vulnerabilities back in 2021 [1]. as roughly a year or so has passed, it was a timely moment to review how things may have evolved with respect to the vulnerabilities discovered. In this comprehensive field guide, you‘ll not only learn how bluetooth attacks work on a technical level, but also simple best practices to lock down your connections without sacrificing convenience. Bluetooth technology, which facilitates wireless communication between billions of devices including smartphones, tablets, laptops, and internet of thing (iot).
Comments are closed.