Tool For Mac Spoofing Everintelligence

Tool For Mac Spoofing Everintelligence A cross platform mac address spoofing tool with both gui and command line interfaces. change your network adapter's mac address for privacy, testing, or network troubleshooting purposes. How do you bypass apple's rigid security protocols against spoofing? here are seven mac address changes that work on the macos environment.

Tool For Mac Spoofing Everintelligence Macchanger is a versatile and essential tool for managing mac addresses in cybersecurity. its ability to spoof, randomize, and restore mac addresses makes it indispensable for privacy, security testing, and network troubleshooting. Just looking for a recommendation for a free mac address spoofing tool. i was using "wifi spoof" which was free off the apple store, but now they want $25 for it no thanks. Every time you connect to a network (e.g. wifi or ethernet), your mac address is exposed. this allows people to use it to track you and uniquely identify you on the local network. Mac addresses have started to be abused by unscrupulous marketing firms, government agencies, and others to provide an easy way to track a computer across multiple networks.
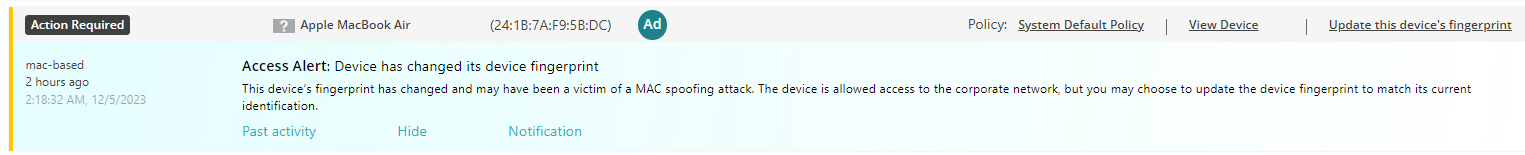
Turn On Mac Address Spoofing Protection By Iot Fingerprinting Every time you connect to a network (e.g. wifi or ethernet), your mac address is exposed. this allows people to use it to track you and uniquely identify you on the local network. Mac addresses have started to be abused by unscrupulous marketing firms, government agencies, and others to provide an easy way to track a computer across multiple networks. The mac spoofer is a cross platform python script designed to change or revert the media access control (mac) address of a network interface. it is a useful tool for enhancing privacy, bypassing network restrictions, or conducting authorized security testing. Discover the best mac spoofing tools in 2026 with real command examples. learn how to spoof mac addresses in linux and windows using macchanger, technitium, spoofmac, and more. perfect for ethical hackers, cybersecurity students, and network engineers. A mac address is intended to be permanent for a device, but you can spoof (change) it to a random address or to a specific device’s mac address to impersonate that device. While it can deter casual intruders, it is not a robust security measure because mac addresses can be easily changed, or "spoofed." in this lab, you will learn how to bypass mac address filtering.
Comments are closed.