Threat Modelling For Developers
Threat Modelling It S Not Just For Developers Aimative This article provides clear and simple steps to help teams that want to adopt threat modelling. threat modelling is a risk based approach to designing secure systems. it is based on identifying threats in order to develop mitigations to them. Developer centric functional threat modeling is a critical approach in the secure development lifecycle that shifts the traditional perspective of threat identification and mitigation towards a more functional viewpoint.

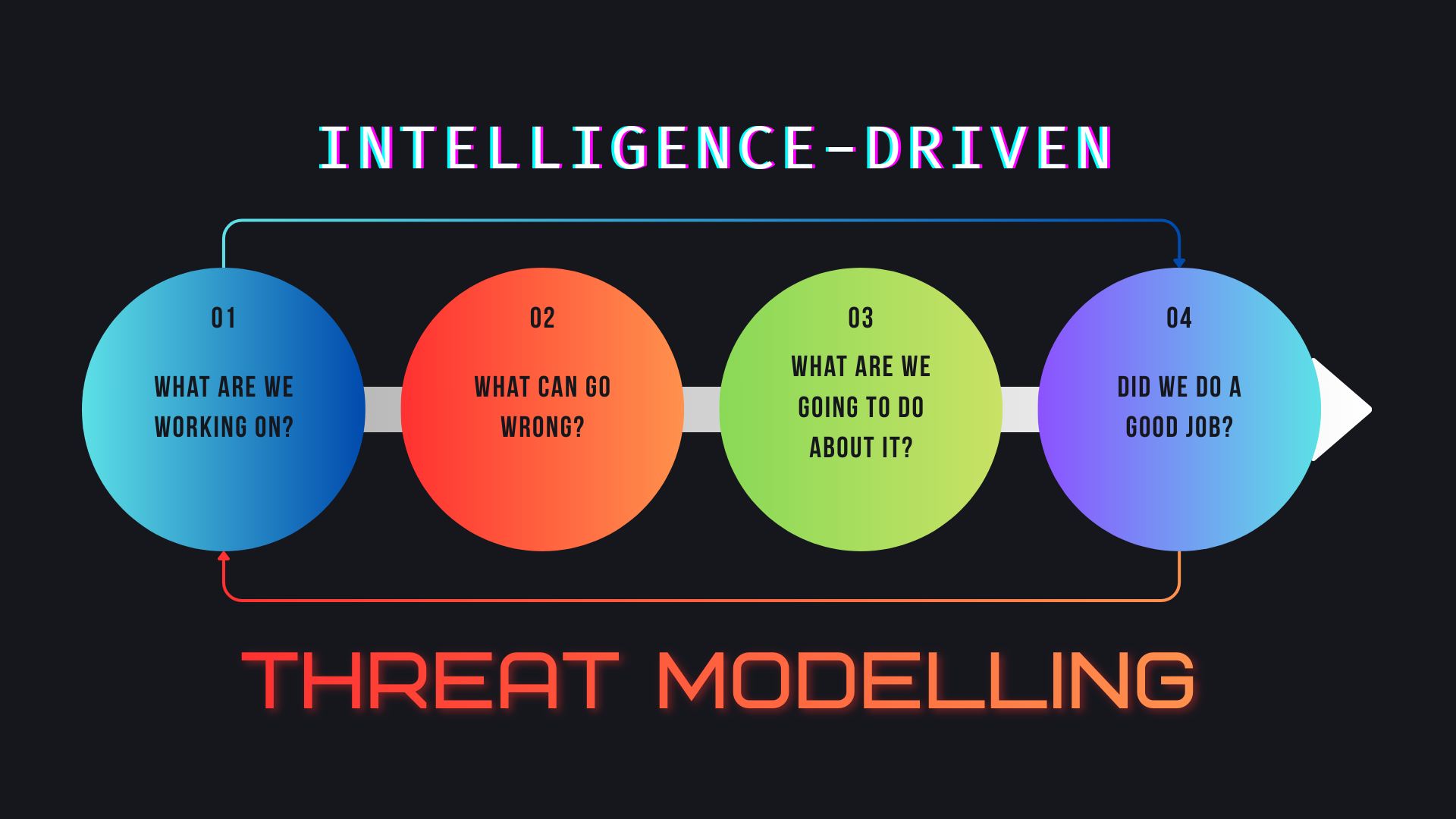
Threat Modelling Services Identify Mitigate Cyber Risks Grhombus Threat modeling is an important concept for modern application developers to understand. the goal of this cheatsheet is to provide a concise, but actionable, reference for both those new to threat modeling and those seeking a refresher. Threat modeling is a process that can help developers identify and understand potential security risks in applications and websites. Threat modeling is a proactive approach that helps identify potential security risks early in development, allowing teams to design more secure applications. this guide provides a step by step. Threat modeling is a collection of techniques to help you do this before you've written a line of new code. at its heart, threat modeling is very simple. we ask four key questions: what are we working on? what can go wrong? what are we going to do about each? did we do a good job?.

Threat Modeling For Developers Stories Hackernoon Threat modeling is a proactive approach that helps identify potential security risks early in development, allowing teams to design more secure applications. this guide provides a step by step. Threat modeling is a collection of techniques to help you do this before you've written a line of new code. at its heart, threat modeling is very simple. we ask four key questions: what are we working on? what can go wrong? what are we going to do about each? did we do a good job?. Threat modeling is a process for capturing, organizing, and analyzing all of this information. applied to software, it enables informed decision making about application security risks. The threat modeling process helps developers think about software security from the very beginning of the secure development lifecycle. by performing asset identification and analyzing trust boundaries, teams can visualize data flow diagrams to map entry points and attack vectors. We designed the tool with non security experts in mind, making threat modeling easier for all developers by providing clear guidance on creating and analyzing threat models. Essentially, threat modeling helps developers think like an attacker, as well as understand the system, identifying potential issues and fixing them before someone more malicious finds them.
Threat Modelling On One Page Jasonlayton Threat modeling is a process for capturing, organizing, and analyzing all of this information. applied to software, it enables informed decision making about application security risks. The threat modeling process helps developers think about software security from the very beginning of the secure development lifecycle. by performing asset identification and analyzing trust boundaries, teams can visualize data flow diagrams to map entry points and attack vectors. We designed the tool with non security experts in mind, making threat modeling easier for all developers by providing clear guidance on creating and analyzing threat models. Essentially, threat modeling helps developers think like an attacker, as well as understand the system, identifying potential issues and fixing them before someone more malicious finds them.
Comments are closed.