Threat Intelligence Use Case Replica Secure Environments
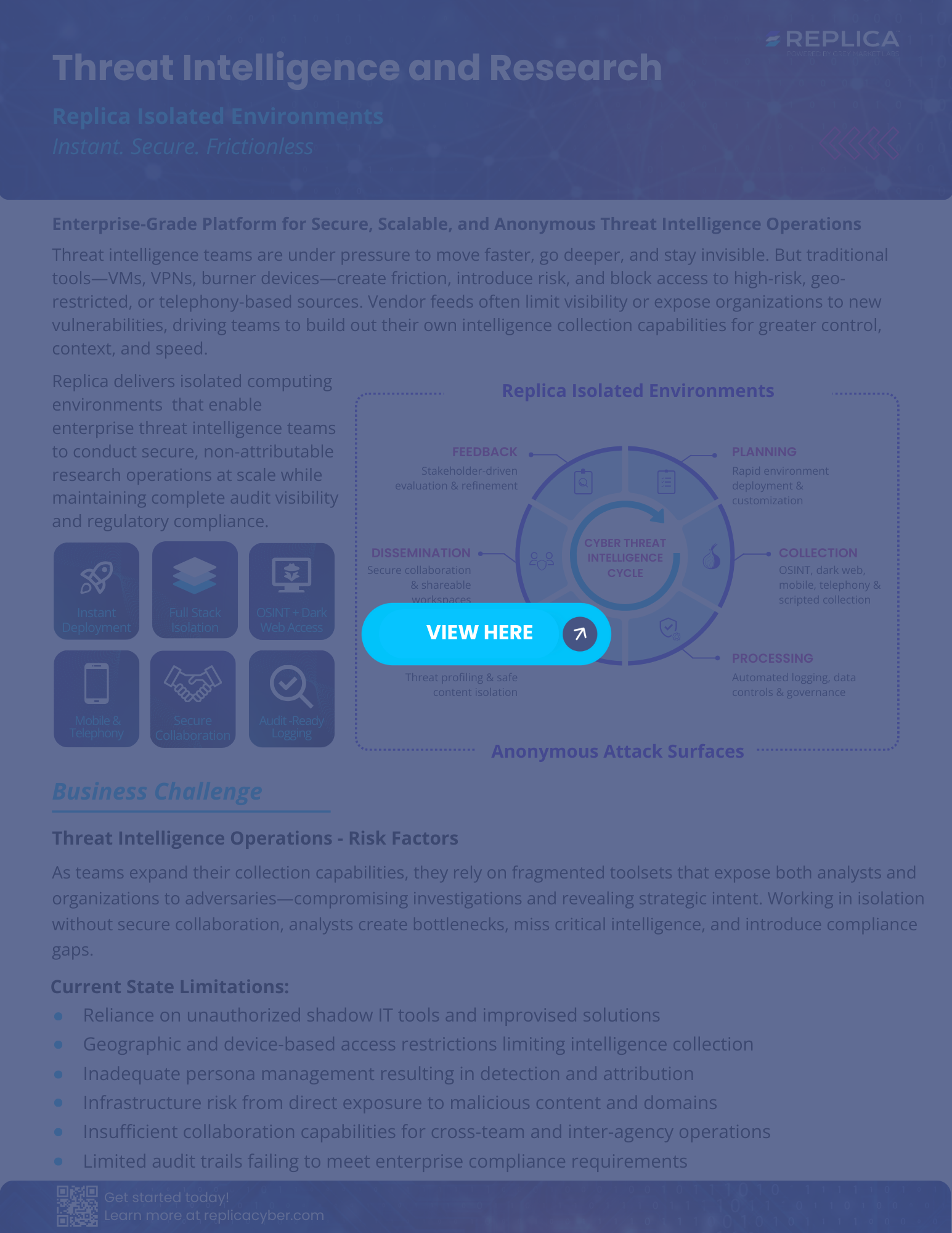
Threat Intelligence Use Case Replica Secure Environments Securely collect, analyze, and collaborate on threat intelligence from dark web, mobile, telephony, and restricted sources with replica. Replica delivers isolated computing environments that enable enterprise threat intelligence teams to conduct secure, non attributable research operations at scale while maintaining complete audit visibility and regulatory compliance.

Threat Intelligence Use Case Replica Secure Environments Download our latest white papers to stay ahead with cutting edge industry knowledge. enable safe, compliant ai experimentation—from tools and workflows to full scale projects—in secure isolated environments that accelerate innovation . Malware & forensic analysis use case replica enables security teams to safely detonate, reverse engineer, and investigate malware while keeping systems and data protected. Identify and deploy threat intelligence use cases for a wide number of scenarios to better secure an organization for improved security and business outcomes. Replica legends celebrates the extraordinary people driving threat intelligence, fraud disruption, malware analysis, and ai innovation. behind every secure operation.

Secure Threat Intelligence Collection In The Ai Era A New Playbook For Identify and deploy threat intelligence use cases for a wide number of scenarios to better secure an organization for improved security and business outcomes. Replica legends celebrates the extraordinary people driving threat intelligence, fraud disruption, malware analysis, and ai innovation. behind every secure operation. Replica delivers full computing environments that empower organizations to conduct high stakes work—securely and behind an anonymous attack surface. our patented zero trust isolated environments eliminate traditional trade offs between security and speed. Threat intelligence use case transform raw data into actionable intelligence, empowering teams to anticipate, detect, and respond to evolving cyber threats with precision . Attribution research: understanding campaign infrastructure often requires accessing threat intelligence sources, passive dns databases, and osint platforms that traditional air gapped environments can’t reach. The replica platform provides complete management of the secure environments with the ability to easily define specific personas, egress and file management options all with strict role based access control.

Threat Intelligence For Multi Cloud Environments Obrela Replica delivers full computing environments that empower organizations to conduct high stakes work—securely and behind an anonymous attack surface. our patented zero trust isolated environments eliminate traditional trade offs between security and speed. Threat intelligence use case transform raw data into actionable intelligence, empowering teams to anticipate, detect, and respond to evolving cyber threats with precision . Attribution research: understanding campaign infrastructure often requires accessing threat intelligence sources, passive dns databases, and osint platforms that traditional air gapped environments can’t reach. The replica platform provides complete management of the secure environments with the ability to easily define specific personas, egress and file management options all with strict role based access control.

Threat Intelligence Use Cases Attribution research: understanding campaign infrastructure often requires accessing threat intelligence sources, passive dns databases, and osint platforms that traditional air gapped environments can’t reach. The replica platform provides complete management of the secure environments with the ability to easily define specific personas, egress and file management options all with strict role based access control.
Comments are closed.