Common Use Case For Technical Threat Intelligence
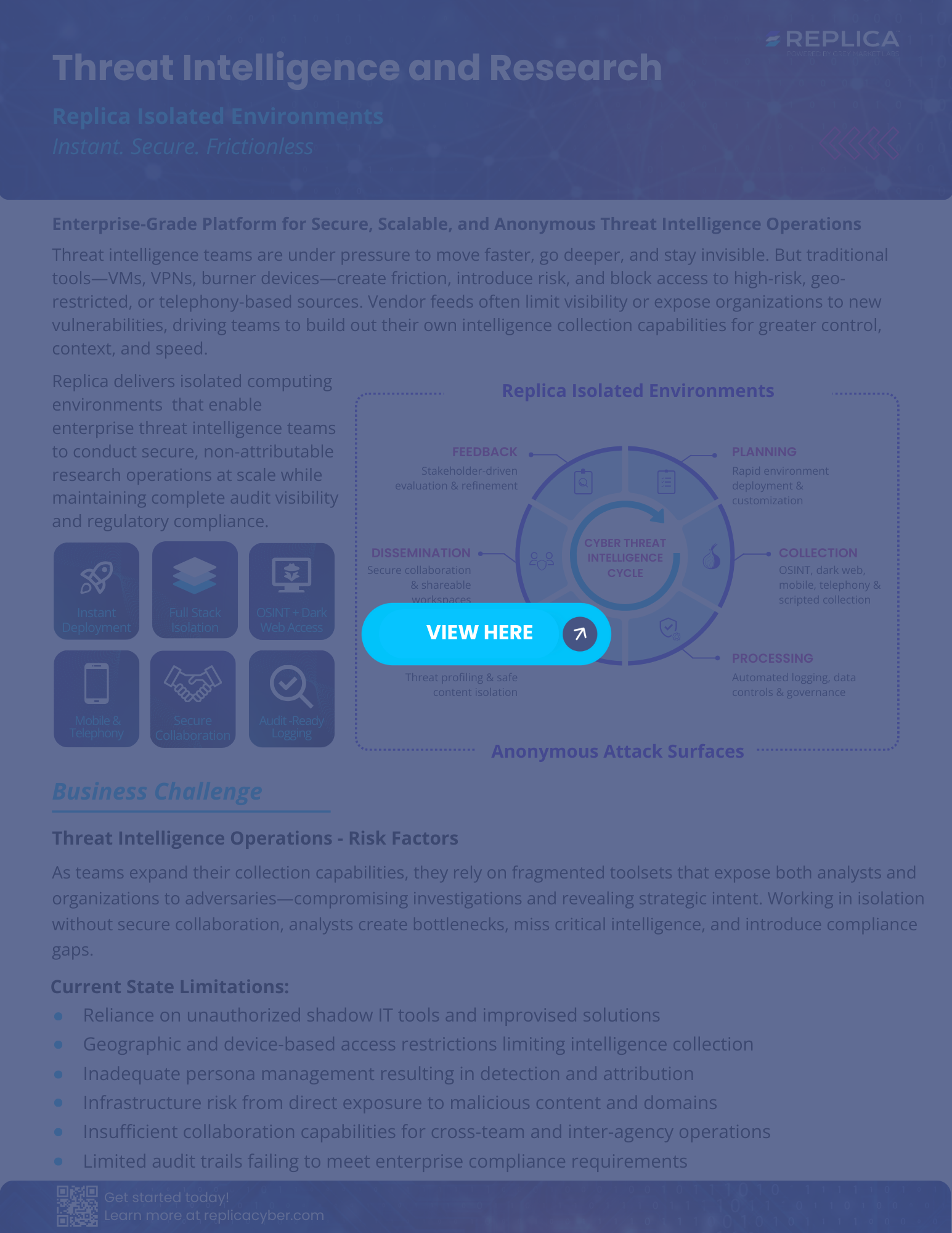
Threat Intelligence Use Case Replica Secure Environments Technical threat intelligence allows teams to conduct proactive threat hunting, analyze security incidents in depth, and locate forensic evidence to help defend against and mitigate the impact of cyberattacks. Learn how technical threat intelligence is used in organizations and see a real world case of how technical ti is collected.

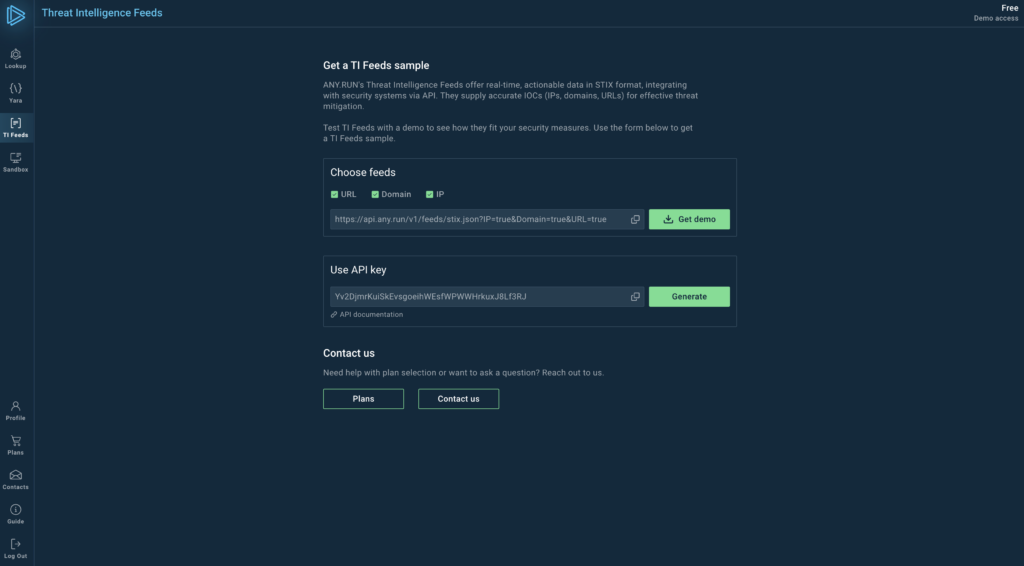
Threat Intelligence Use Case Replica Secure Environments Explore common threat intelligence examples and use cases to learn how cyber intelligence strengthens security and aids proactive threat response. 👨💻 what are common use cases for technical ti? technical ti revolves around collecting, analyzing, and disseminating threat data, which comes from ti feeds and malware analysis sessions. Discover the top 5 use cases and examples of threat intelligence solutions and learn how they can enhance your cybersecurity strategy and protect your organization. There are four main types of threat intelligence, each with its own use cases and focus. here’s a closer look:.

Common Use Case For Technical Threat Intelligence Discover the top 5 use cases and examples of threat intelligence solutions and learn how they can enhance your cybersecurity strategy and protect your organization. There are four main types of threat intelligence, each with its own use cases and focus. here’s a closer look:. By effectively utilizing threat intelligence, organizations can identify potential threats, respond swiftly to incidents, and implement proactive measures to prevent future attacks. Product categories like: brand protection, domain management, attack surface management, soar, social media platforms, bug bounty platforms can be used for cti use cases. Unlike operational or tactical intelligence, strategic threat intelligence is less concerned with technical indicators or daily incidents. instead, it equips decision makers with the context needed for setting security budgets, influencing corporate policy, and meeting regulatory obligations. For a long time, common wisdom held that a passive strategy — protecting the network perimeter and workstations — sufficed. but with enterprises increasingly falling victim to advanced and targeted attacks, it’s now clear that protection requires new methods, based on threat intelligence.
What Is A Common Use Case For Technical Threat Intelligence Malware By effectively utilizing threat intelligence, organizations can identify potential threats, respond swiftly to incidents, and implement proactive measures to prevent future attacks. Product categories like: brand protection, domain management, attack surface management, soar, social media platforms, bug bounty platforms can be used for cti use cases. Unlike operational or tactical intelligence, strategic threat intelligence is less concerned with technical indicators or daily incidents. instead, it equips decision makers with the context needed for setting security budgets, influencing corporate policy, and meeting regulatory obligations. For a long time, common wisdom held that a passive strategy — protecting the network perimeter and workstations — sufficed. but with enterprises increasingly falling victim to advanced and targeted attacks, it’s now clear that protection requires new methods, based on threat intelligence.

What Is Technical Threat Intelligence Unlike operational or tactical intelligence, strategic threat intelligence is less concerned with technical indicators or daily incidents. instead, it equips decision makers with the context needed for setting security budgets, influencing corporate policy, and meeting regulatory obligations. For a long time, common wisdom held that a passive strategy — protecting the network perimeter and workstations — sufficed. but with enterprises increasingly falling victim to advanced and targeted attacks, it’s now clear that protection requires new methods, based on threat intelligence.
Comments are closed.