Threat Intelligence Hunting Crowdstrike

What Is Cyber Threat Hunting Proactive Guide Crowdstrike Quickly access crowdstrike's industry leading threat intelligence directly in your chrome browser. the crowdstrike threat intelligence browser extension scans web pages to identify iocs, adversaries, malware, and vulnerabilities, providing rich context and analysis without switching between tools. A unified security solution that empowers every crowdstrike threat hunter with extensive security telemetry — spanning endpoint, identity, cloud, and next gen siem, along with integrated intelligence — to detect and disrupt threats quickly and effectively.
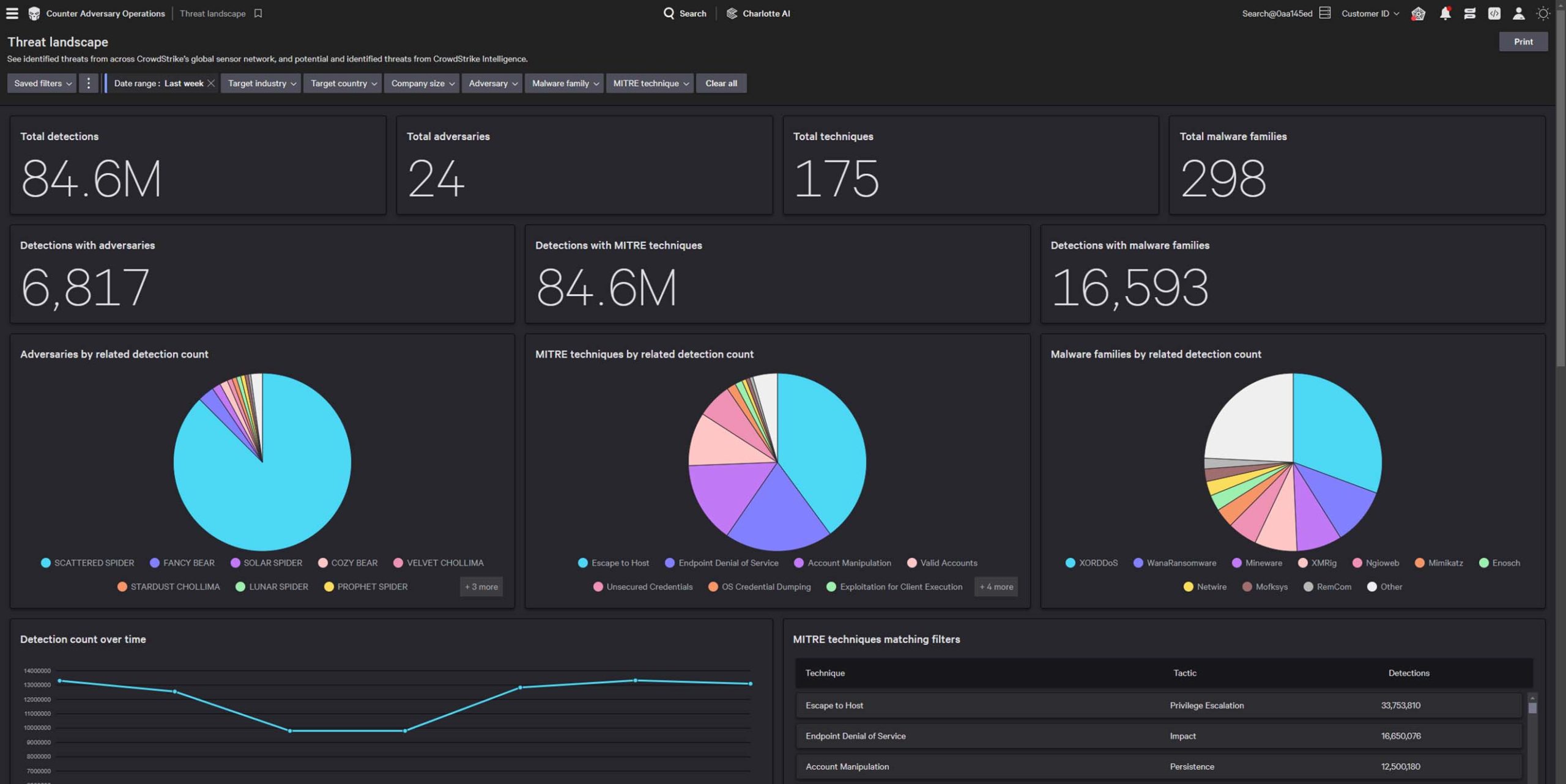
Threat Intelligence Hunting Crowdstrike The crowdstrike annual threat hunting report is one of the most critical intelligence documents for security experts, detailing adversary behavior, sector targeting, and intrusion tactics. The report reveals how threat actors are targeting tools used to build ai agents—gaining access, stealing credentials, and deploying malware—a clear sign that autonomous systems and machine identities have become a core part of the enterprise attack surface. In the crowdstrike 2024 threat hunting report, crowdstrike unveils the latest tactics of 245 modern adversaries and shows how these adversaries continue to evolve and emulate legitimate user behavior. get insights to help stop breaches here. Autonomous threat hunting using the peak framework — hypothesis driven, intelligence driven, and baseline hunts against crowdstrike ng siem with hunt….
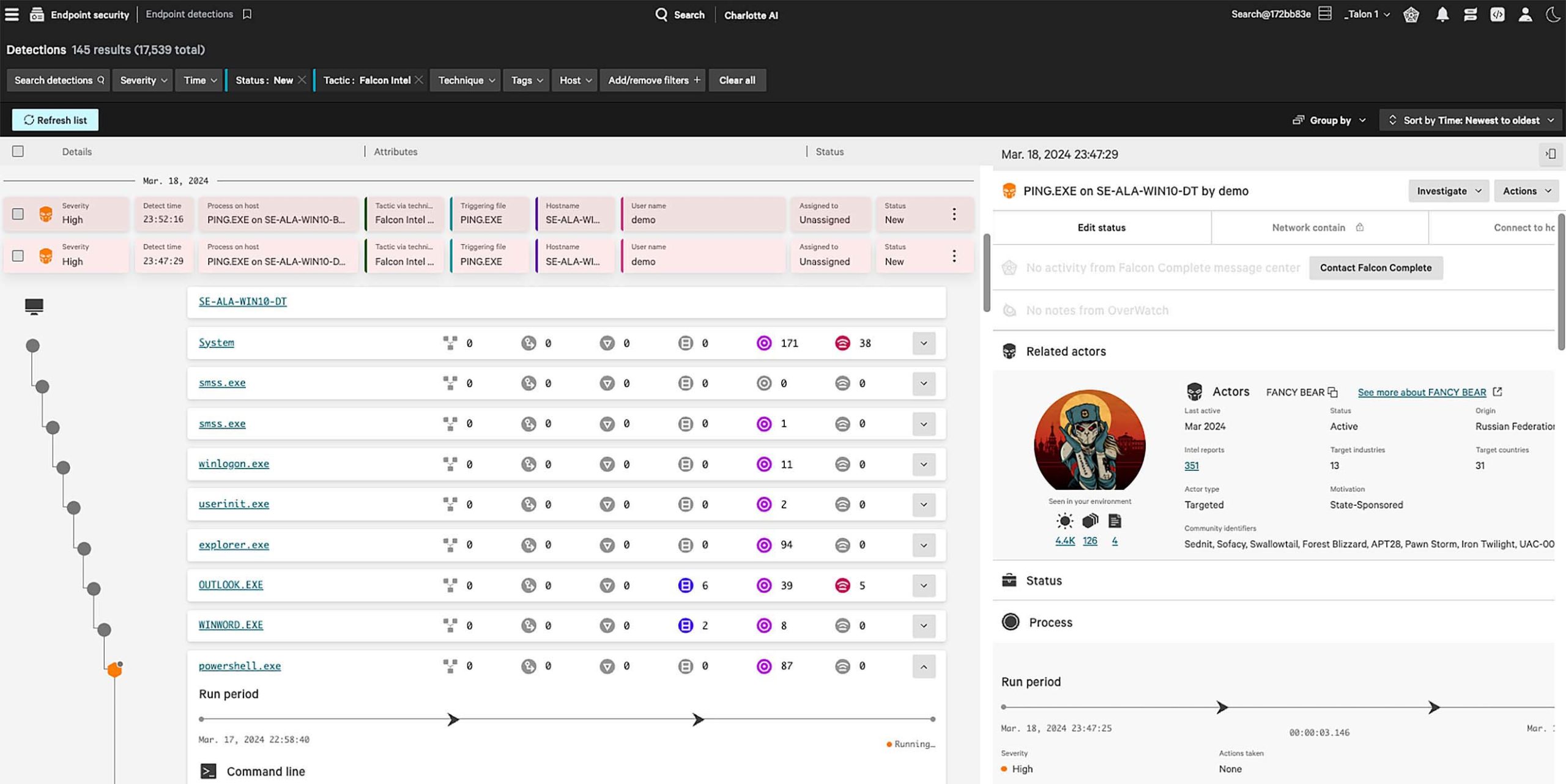
Threat Intelligence Hunting Crowdstrike In the crowdstrike 2024 threat hunting report, crowdstrike unveils the latest tactics of 245 modern adversaries and shows how these adversaries continue to evolve and emulate legitimate user behavior. get insights to help stop breaches here. Autonomous threat hunting using the peak framework — hypothesis driven, intelligence driven, and baseline hunts against crowdstrike ng siem with hunt…. Agentic ai is the new attack surface: crowdstrike observed multiple threat actors exploiting vulnerabilities in tools used to build ai agents, gaining unauthenticated access, establishing persistence, harvesting credentials, and deploying malware and ransomware. By combining data and detections from multiple domains and leveraging that against crowdstrike’s threat intelligence, crowdstrike overwatch is uniquely situated to respond to threats that cross these domain barriers. Crowdstrike has released the 2025 threat hunting report, highlighting a new phase in modern cyberattacks: adversaries are weaponizing genai to scale operations and accelerate attacks – and increasingly targeting the autonomous ai agents reshaping enterprise operations. Crowdstrike’s recommendations explicitly call for prioritizing proactive threat intelligence and hunting, and for augmenting analysts with specialized ai agents that can operate at the speed and scale required. this is the concept skyhawk calls left of boom. acting before the attack happens, rather than responding after it has already succeeded.

Crowdstrike Bundles Threat Hunting And Intelligence To Combat Identity Agentic ai is the new attack surface: crowdstrike observed multiple threat actors exploiting vulnerabilities in tools used to build ai agents, gaining unauthenticated access, establishing persistence, harvesting credentials, and deploying malware and ransomware. By combining data and detections from multiple domains and leveraging that against crowdstrike’s threat intelligence, crowdstrike overwatch is uniquely situated to respond to threats that cross these domain barriers. Crowdstrike has released the 2025 threat hunting report, highlighting a new phase in modern cyberattacks: adversaries are weaponizing genai to scale operations and accelerate attacks – and increasingly targeting the autonomous ai agents reshaping enterprise operations. Crowdstrike’s recommendations explicitly call for prioritizing proactive threat intelligence and hunting, and for augmenting analysts with specialized ai agents that can operate at the speed and scale required. this is the concept skyhawk calls left of boom. acting before the attack happens, rather than responding after it has already succeeded.
Comments are closed.