This Linux Patch Removes Spectre Meltdown Protections

Check For Meltdown And Spectre Vulnerabilities And Patch Them In Linux Now, people are rethinking the trade off. ubuntu has disabled some protections, resulting in 20% performance boost. after discussion between intel and canonical’s security teams, we are in agreement that spectre no longer needs to be mitigated for the gpu at the compute runtime level. Canonical’s decision to ship ubuntu 24.04 lts (noble numbat) and the upcoming 25.10 release with spectre defenses disabled in intel’s gpu compute runtime has sparked lively debate.
Check For Meltdown And Spectre Vulnerabilities And Patch Them In Linux Ubuntu’s decision to disable some spectre meltdown protections, leading to a potential 20% performance boost, signals a pivotal shift in how we balance security and speed in the age of advanced computing. Now, people are rethinking the trade off. ubuntu has disabled some protections, resulting in 20% performance boost. after discussion between intel and canonical’s security teams, we are in agreement that spectre no longer needs to be mitigated for the gpu at the compute runtime level. This article will delve into the details of the spectre and meltdown vulnerabilities, the patches designed to mitigate them, and most importantly, how to turn off these patches for those who require optimal system performance. Now, people are rethinking the trade off. ubuntu has disabled some protections, resulting in 20% performance boost. after discussion between intel and canonical’s security teams, we are in agreement that spectre no longer needs to be mitigated for the gpu at the compute runtime level.
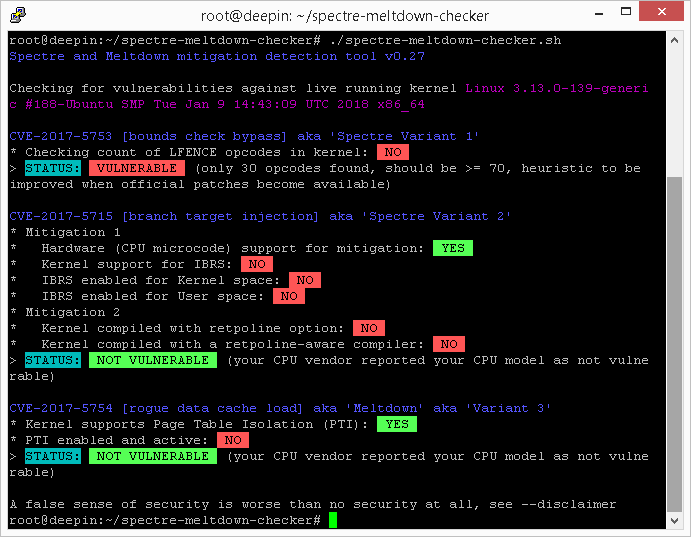
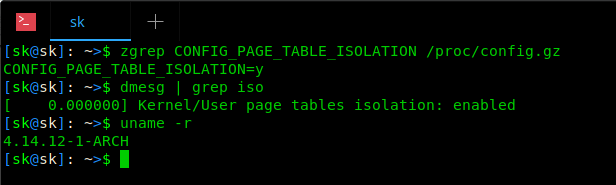
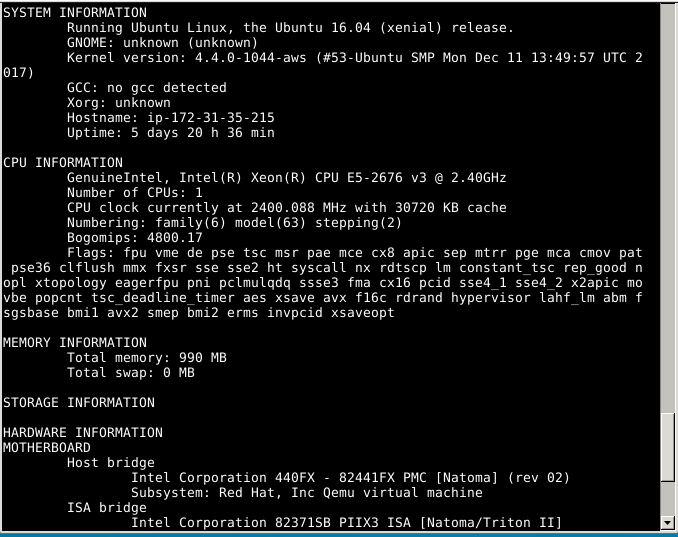
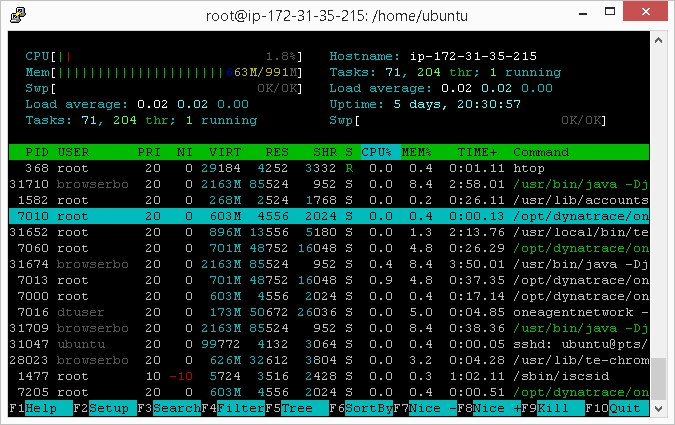
Check For Meltdown And Spectre Vulnerabilities And Patch Them In Linux This article will delve into the details of the spectre and meltdown vulnerabilities, the patches designed to mitigate them, and most importantly, how to turn off these patches for those who require optimal system performance. Now, people are rethinking the trade off. ubuntu has disabled some protections, resulting in 20% performance boost. after discussion between intel and canonical’s security teams, we are in agreement that spectre no longer needs to be mitigated for the gpu at the compute runtime level. For linux systems, the tool will detect mitigations, including backported non vanilla patches, regardless of the advertised kernel version number and the distribution (such as debian, ubuntu, centos, rhel, fedora, opensuse, arch, ), it also works if you've compiled your own kernel. It's been a few years since spectre and meltdown were major news stories and since the mitigations were added for those and other exploits you've been able to remove them with a kernel. Now, people are rethinking the trade off. ubuntu has disabled some protections, resulting in 20% performance boost. after discussion between intel and canonical’s security teams, we are in agreement that spectre no longer needs to be mitigated for the gpu at the compute runtime level. For safeguarding ourselves from this type of vulnerability there comes a shell script called spectre & meltdown checker to tell if our system is vulnerable against the several"meltdown" & "speculative execution" cves (common vulnerabilities and exposures).

Check For Meltdown And Spectre Vulnerabilities And Patch Them In Linux For linux systems, the tool will detect mitigations, including backported non vanilla patches, regardless of the advertised kernel version number and the distribution (such as debian, ubuntu, centos, rhel, fedora, opensuse, arch, ), it also works if you've compiled your own kernel. It's been a few years since spectre and meltdown were major news stories and since the mitigations were added for those and other exploits you've been able to remove them with a kernel. Now, people are rethinking the trade off. ubuntu has disabled some protections, resulting in 20% performance boost. after discussion between intel and canonical’s security teams, we are in agreement that spectre no longer needs to be mitigated for the gpu at the compute runtime level. For safeguarding ourselves from this type of vulnerability there comes a shell script called spectre & meltdown checker to tell if our system is vulnerable against the several"meltdown" & "speculative execution" cves (common vulnerabilities and exposures).
Check For Meltdown And Spectre Vulnerabilities And Patch Them In Linux Now, people are rethinking the trade off. ubuntu has disabled some protections, resulting in 20% performance boost. after discussion between intel and canonical’s security teams, we are in agreement that spectre no longer needs to be mitigated for the gpu at the compute runtime level. For safeguarding ourselves from this type of vulnerability there comes a shell script called spectre & meltdown checker to tell if our system is vulnerable against the several"meltdown" & "speculative execution" cves (common vulnerabilities and exposures).
Check For Meltdown And Spectre Vulnerabilities And Patch Them In Linux
Comments are closed.