The Intelligence Lifecycle Explained

Threat Intelligence Lifecycle Analyst1 This security intelligence lifecycle enables organizations to gather data on threats with confidence, analyze it for accuracy and reliability, and take action to protect themselves. The lifecycle is typically divided into six stages: planning and direction, collection, processing, analysis, dissemination, and feedback. each step builds on the last, creating a repeatable process that strengthens defenses in cyber threat intelligence efforts.

Threat Intelligence Lifecycle Analyst1 A complete guide to the cyber threat intelligence lifecycle. learn each phase from planning to dissemination, and how cti strengthens your security operations. We examine five phases of the threat intelligence lifecycle and how fraud, physical, and cybersecurity programs embed it in their operations. The threat intelligence lifecycle is a structured, cyclical framework that guides security teams in converting raw data into finished intelligence. each of the six phases plays a distinct role in ensuring the final output is accurate, relevant, and actionable for defending your organization. What is the cyber threat intelligence lifecycle? cyber threat intelligence lifecycle is a 6 stage continuous process that converts raw threat data into actionable intelligence for security decisions. it defines a structured flow where organizations collect, process, and analyze threat data.

The Intelligence Lifecycle Phase 1 Planning Direction The threat intelligence lifecycle is a structured, cyclical framework that guides security teams in converting raw data into finished intelligence. each of the six phases plays a distinct role in ensuring the final output is accurate, relevant, and actionable for defending your organization. What is the cyber threat intelligence lifecycle? cyber threat intelligence lifecycle is a 6 stage continuous process that converts raw threat data into actionable intelligence for security decisions. it defines a structured flow where organizations collect, process, and analyze threat data. The problem isn’t the framework. it’s execution. teams collect everything and prioritize nothing. this guide walks through the six phase threat intelligence lifecycle, where teams get it wrong, and how to build a program that drives real security decisions. This post provides a deep, book level explanation of the threat intelligence lifecycle, exactly as implemented in enterprise socs, national certs, and mature cyber defense programs. The threat intelligence lifecycle is a systematic process that ensures the effective creation and management of intelligence. this module explores each phase in detail and how they work together to create actionable intelligence. you may see the model with less or more stages in it. Explore the cyber threat intelligence lifecycle explained step by step. learn phases, best practices, and ai integration for enterprise cybersecurity in 2026.
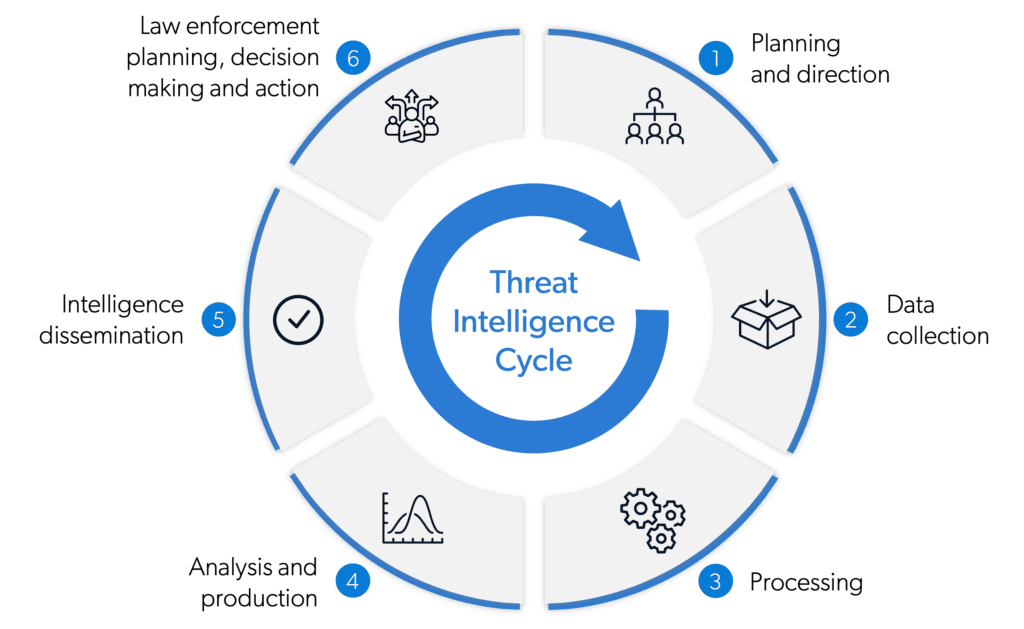
Threat Intelligence Lifecycle Definition Explanation Examples The problem isn’t the framework. it’s execution. teams collect everything and prioritize nothing. this guide walks through the six phase threat intelligence lifecycle, where teams get it wrong, and how to build a program that drives real security decisions. This post provides a deep, book level explanation of the threat intelligence lifecycle, exactly as implemented in enterprise socs, national certs, and mature cyber defense programs. The threat intelligence lifecycle is a systematic process that ensures the effective creation and management of intelligence. this module explores each phase in detail and how they work together to create actionable intelligence. you may see the model with less or more stages in it. Explore the cyber threat intelligence lifecycle explained step by step. learn phases, best practices, and ai integration for enterprise cybersecurity in 2026.
Comments are closed.