Threat Intelligence Lifecycle

Threat Intelligence Lifecycle Analyst1 The lifecycle is typically divided into six stages: planning and direction, collection, processing, analysis, dissemination, and feedback. each step builds on the last, creating a repeatable process that strengthens defenses in cyber threat intelligence efforts. A complete guide to the cyber threat intelligence lifecycle. learn each phase from planning to dissemination, and how cti strengthens your security operations.

Threat Intelligence Lifecycle Analyst1 The threat intelligence lifecycle is a process used in cybersecurity to manage cyberthreats. it helps organizations protect their information assets by gathering, analyzing, and applying information about potential and current cyberthreats. The threat intelligence lifecycle consists of five repeatable phases that describe how intelligence moves from intent to action: requirements & tasking, collection & discovery, analysis & prioritization, dissemination & action, and feedback & retasking. The threat intelligence lifecycle is a structured, cyclical framework that guides security teams in converting raw data into finished intelligence. each of the six phases plays a distinct role in ensuring the final output is accurate, relevant, and actionable for defending your organization. Learn about the different phases of the threat intelligence lifecycle, as well as best practices for each phase.

Threat Intelligence Lifecycle Phases Best Practice Explained Snyk The threat intelligence lifecycle is a structured, cyclical framework that guides security teams in converting raw data into finished intelligence. each of the six phases plays a distinct role in ensuring the final output is accurate, relevant, and actionable for defending your organization. Learn about the different phases of the threat intelligence lifecycle, as well as best practices for each phase. The threat intelligence lifecycle focuses on six distinct phases, which are explained below: 1. direction: the lifecycle commences with planning out the goals, objectives, scope and methodology for the process of collecting threat intelligence based on the requirements of key stakeholders involved. What is the cyber threat intelligence lifecycle? cyber threat intelligence lifecycle is a 6 stage continuous process that converts raw threat data into actionable intelligence for security decisions. it defines a structured flow where organizations collect, process, and analyze threat data. The threat intelligence lifecycle is a six phase process: planning and direction, collection, processing, analysis, dissemination, and feedback. it provides a structured framework for transforming raw threat data into actionable intelligence and continuously improving the program’s effectiveness. Explore the cyber threat intelligence lifecycle explained step by step. learn phases, best practices, and ai integration for enterprise cybersecurity in 2026.
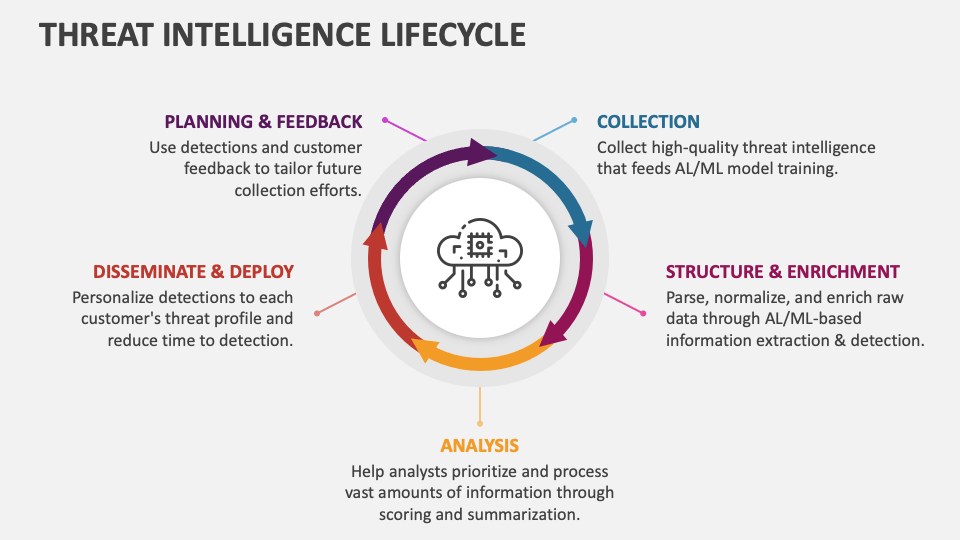
Threat Intelligence Lifecycle Template For Google Slides And Powerpoint The threat intelligence lifecycle focuses on six distinct phases, which are explained below: 1. direction: the lifecycle commences with planning out the goals, objectives, scope and methodology for the process of collecting threat intelligence based on the requirements of key stakeholders involved. What is the cyber threat intelligence lifecycle? cyber threat intelligence lifecycle is a 6 stage continuous process that converts raw threat data into actionable intelligence for security decisions. it defines a structured flow where organizations collect, process, and analyze threat data. The threat intelligence lifecycle is a six phase process: planning and direction, collection, processing, analysis, dissemination, and feedback. it provides a structured framework for transforming raw threat data into actionable intelligence and continuously improving the program’s effectiveness. Explore the cyber threat intelligence lifecycle explained step by step. learn phases, best practices, and ai integration for enterprise cybersecurity in 2026.
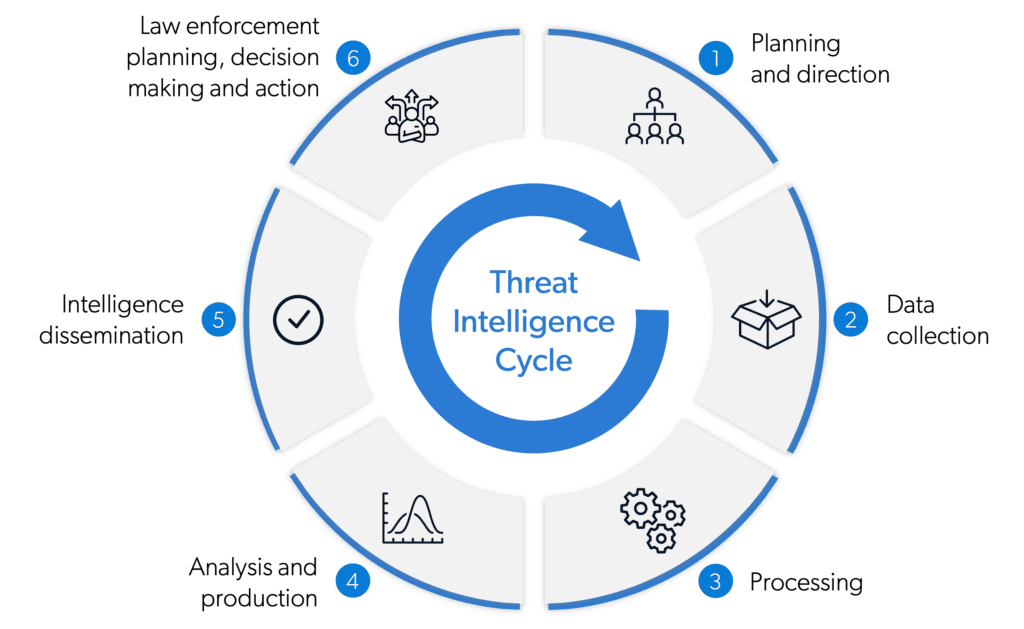
Threat Intelligence Lifecycle Definition Explanation Examples The threat intelligence lifecycle is a six phase process: planning and direction, collection, processing, analysis, dissemination, and feedback. it provides a structured framework for transforming raw threat data into actionable intelligence and continuously improving the program’s effectiveness. Explore the cyber threat intelligence lifecycle explained step by step. learn phases, best practices, and ai integration for enterprise cybersecurity in 2026.

Understanding The Cyber Threat Intelligence Lifecycle Filigran Blog
Comments are closed.