The Essential Eight Overview

A Comprehensive Guide To The Essential Eight Pdf Security While no set of mitigation strategies are guaranteed to protect against all cyber threats, organisations are recommended to implement eight essential mitigation strategies from the strategies to mitigate cyber security incidents as a baseline. Learn how to assess and implement the acsc essential eight maturity levels.

Overview Of Essential Eight Emdeh S Substack Australian organisations must adhere to robust cyber security frameworks to protect sensitive data and ensure business continuity. the australian cyber security centre (acsc) developed the essential 8 as a set of baseline strategies to mitigate cyber threats and safeguard business operations. The “essential eight” is a cybersecurity framework developed by the australian cyber security centre (acsc). the eight strategies that constitute the framework cover the minimum essential controls that organizations should implement to stay protected from cyber threats. The essential eight strategies are designed to be self assessed and or externally assessed against a maturity model (e8mm). the model consists of four maturity levels, maturity level 0 to maturity level 3, that are clearly articulated for each of the essential eight strategies. Essential 8 is a practical, technical baseline created by the australian cyber security centre (acsc). it focuses on eight specific strategies (like patching, mfa, backups) that directly reduce the risk of common cyber attacks.
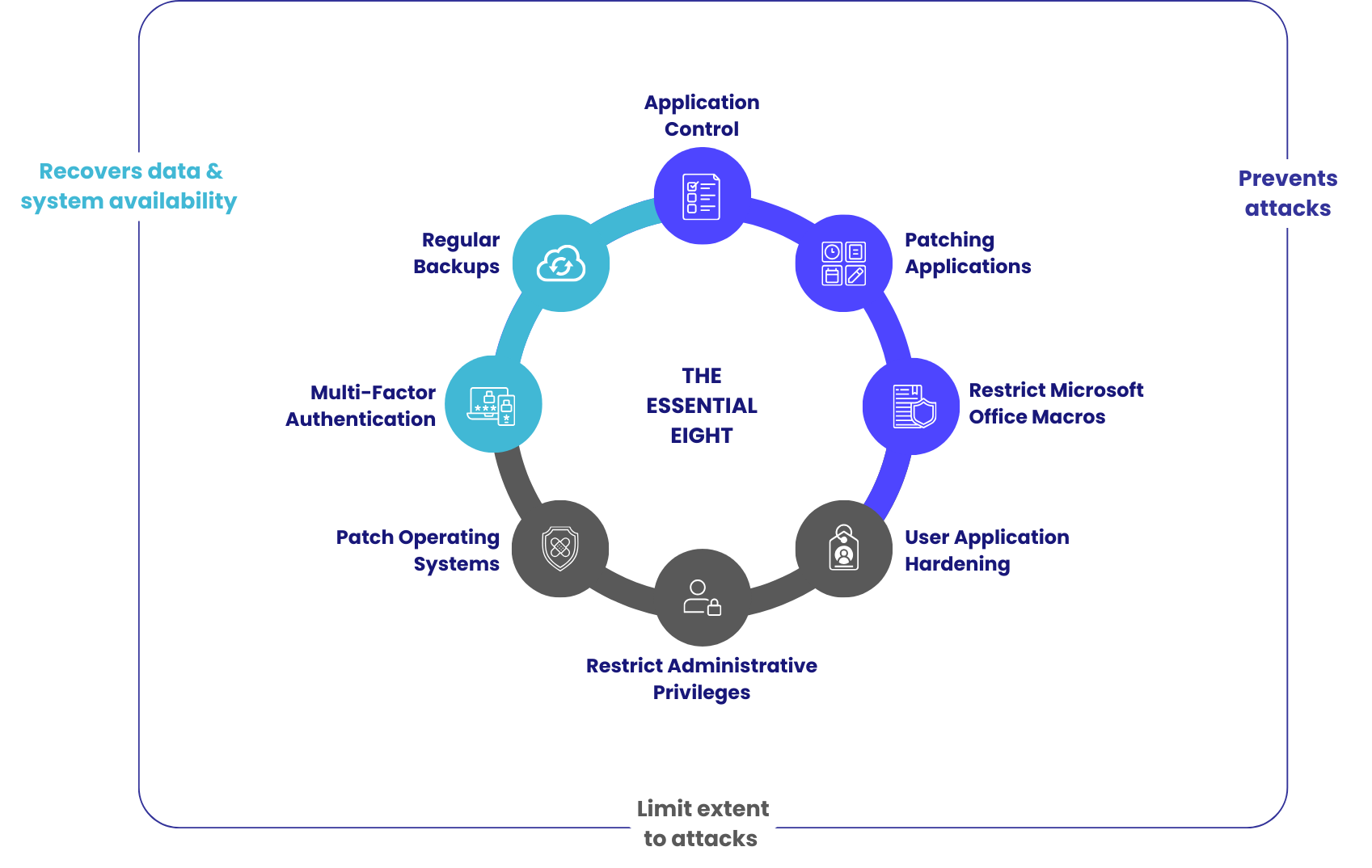
Acsc Essential Eight Cyberunlocked Sydney The essential eight strategies are designed to be self assessed and or externally assessed against a maturity model (e8mm). the model consists of four maturity levels, maturity level 0 to maturity level 3, that are clearly articulated for each of the essential eight strategies. Essential 8 is a practical, technical baseline created by the australian cyber security centre (acsc). it focuses on eight specific strategies (like patching, mfa, backups) that directly reduce the risk of common cyber attacks. Overview assessments against the essential eight are conducted using the essential eight maturity model. this maturity model describes three target maturity levels (maturity level one through to maturity level three) which are based on mitigating increasing levels of targeting and tradecraft. The essential eight is an australian cybersecurity strategy consisting of eight mitigation strategies aimed at bolstering an organization’s cyber defenses, applicable to both government and private sectors. The essential eight, a strategy recommended by the australian cyber security centre (acsc), provides a framework to mitigate cyber security incidents. this model acts as a benchmark for organizations to assess their security posture and implement improvements where necessary. The essential eight refer to a baseline of eight mitigation areas and strategies developed by the australian signals directorate to help organizations protect themselves against various cyber threats.
Essential Eight Guide Mobile Mentor Overview assessments against the essential eight are conducted using the essential eight maturity model. this maturity model describes three target maturity levels (maturity level one through to maturity level three) which are based on mitigating increasing levels of targeting and tradecraft. The essential eight is an australian cybersecurity strategy consisting of eight mitigation strategies aimed at bolstering an organization’s cyber defenses, applicable to both government and private sectors. The essential eight, a strategy recommended by the australian cyber security centre (acsc), provides a framework to mitigate cyber security incidents. this model acts as a benchmark for organizations to assess their security posture and implement improvements where necessary. The essential eight refer to a baseline of eight mitigation areas and strategies developed by the australian signals directorate to help organizations protect themselves against various cyber threats.
Comments are closed.