Temporary Access Infisical

Temporary Access Pdf Learn how to set up timed access to sensitive resources for user and machine identities. certain environments and secrets are so sensitive that it is recommended to not give any user permanent access to those. for such use cases, infisical supports the functionality of temporary access provisioning. to provision temporary access through web ui:. Certain environments and secrets are so sensitive that it is recommended to not give any user permanent access to those. for such use cases, infisical supports the functionality of temporary access provisioning.
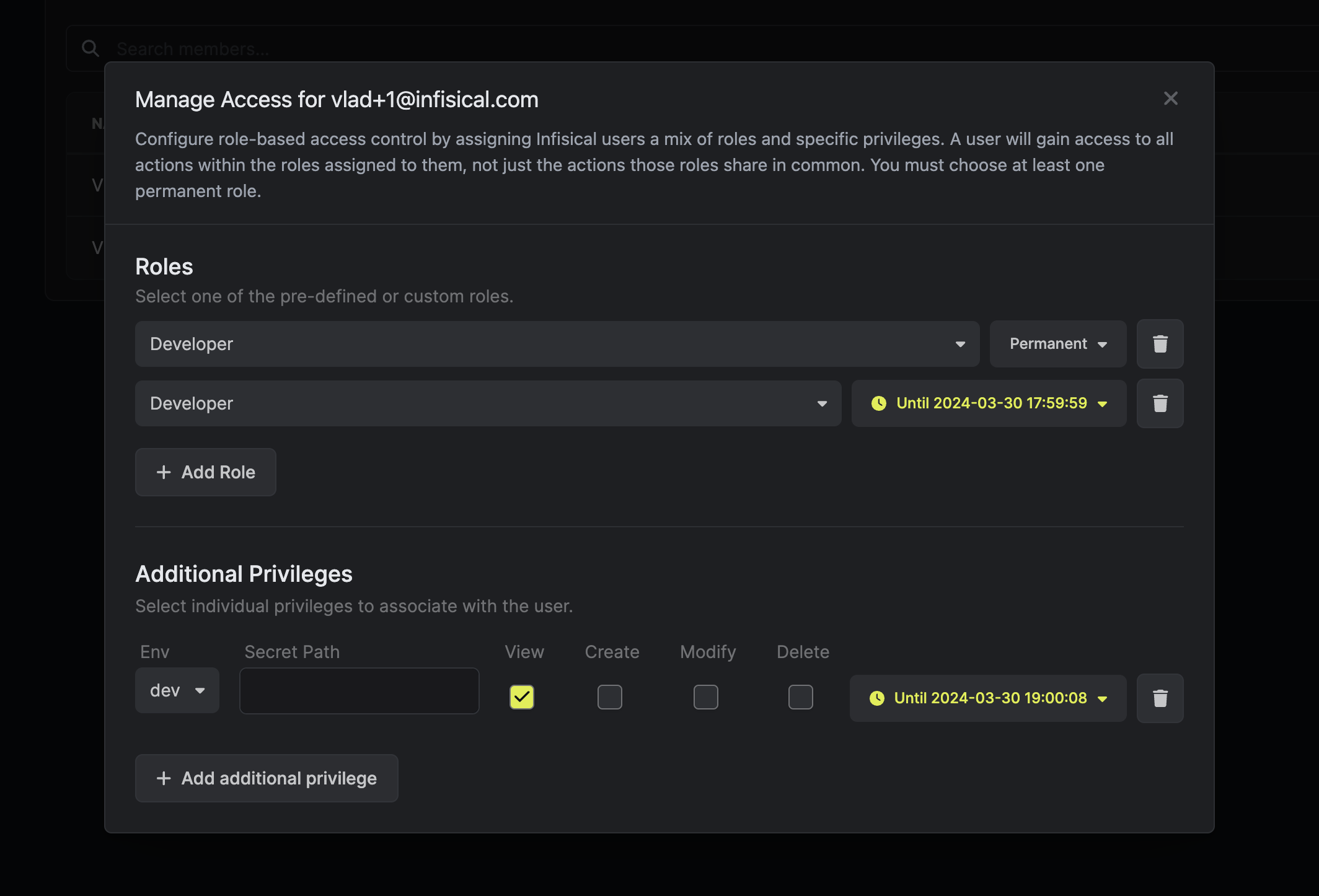
Temporary Access Infisical Access approval workflows enable users to request temporary or permanent access to specific environments and secret paths. the system enforces policy based approval requirements before granting additional privileges. Securing ssh access to linux servers without static keys issue time bound, centrally managed ssh certificates via infisical’s signed certificate feature to replace traditional key pairs and revoke access instantly. In the context of infisical, this means that only the intended recipients (whether they’re individuals, servers, or applications) can decrypt and access the secrets. This document covers the groups and group based access control system in infisical. groups are collections of users and machine identities that can be assigned permissions at the organization or project level, enabling centralized management of access control.
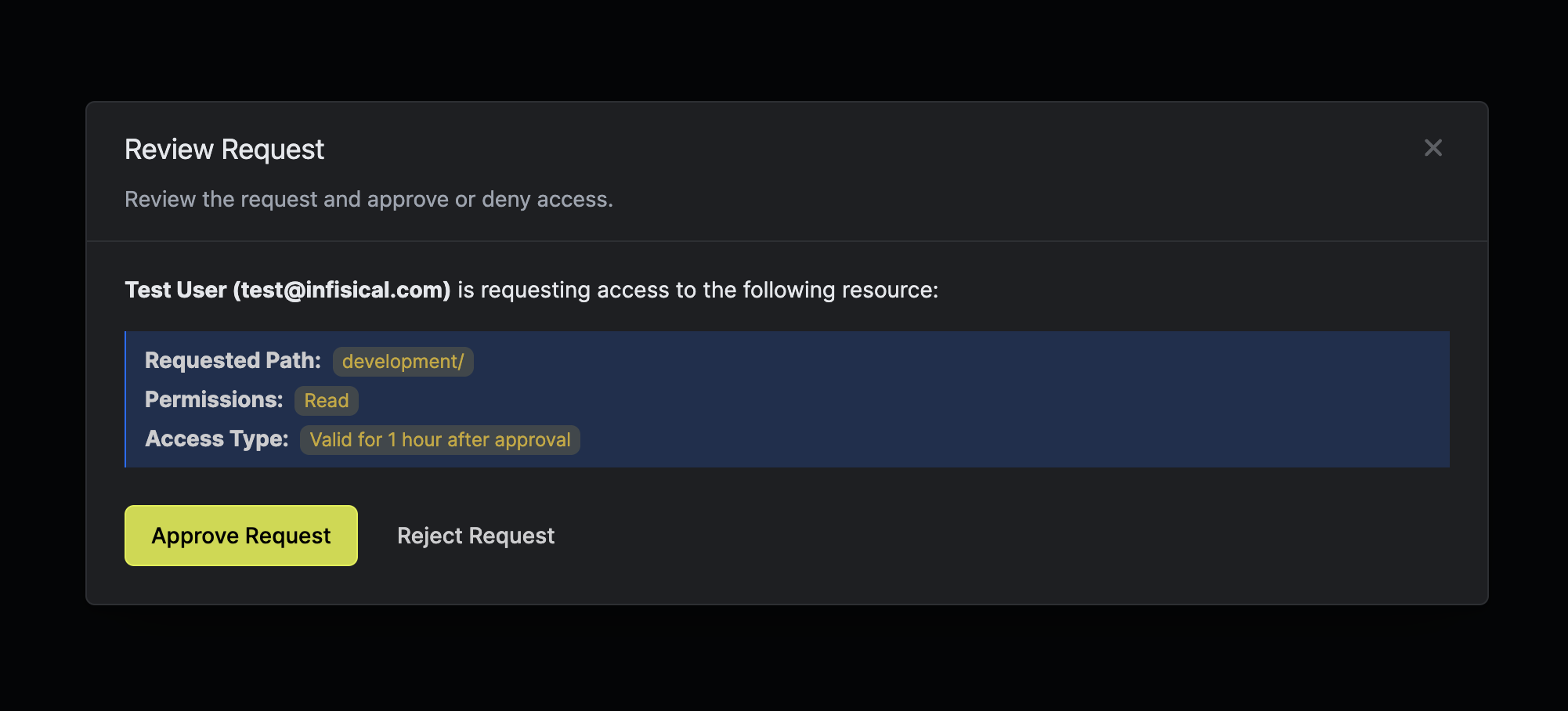
Access Requests Infisical In the context of infisical, this means that only the intended recipients (whether they’re individuals, servers, or applications) can decrypt and access the secrets. This document covers the groups and group based access control system in infisical. groups are collections of users and machine identities that can be assigned permissions at the organization or project level, enabling centralized management of access control. Access requests allow users to request temporary or permanent access to secrets in specific environments and folders. administrators can define policies that control who can approve requests, set time limits, and configure expiration rules. Access controls: define advanced authorization controls for users and machine identities with rbac, additional privileges, temporary access, access requests, approval workflows, and more. Instead of sharing static credentials, your team can request temporary access through infisical, which is then brokered through a secure gateway with full auditing and session recording. Infisical is the all in one identity security platform for developers, machines, and ai agents. manage identities, secrets, certs, and access.
Github Ankitrox Temporary Access Access Wordpress Site Temporarily Access requests allow users to request temporary or permanent access to secrets in specific environments and folders. administrators can define policies that control who can approve requests, set time limits, and configure expiration rules. Access controls: define advanced authorization controls for users and machine identities with rbac, additional privileges, temporary access, access requests, approval workflows, and more. Instead of sharing static credentials, your team can request temporary access through infisical, which is then brokered through a secure gateway with full auditing and session recording. Infisical is the all in one identity security platform for developers, machines, and ai agents. manage identities, secrets, certs, and access.
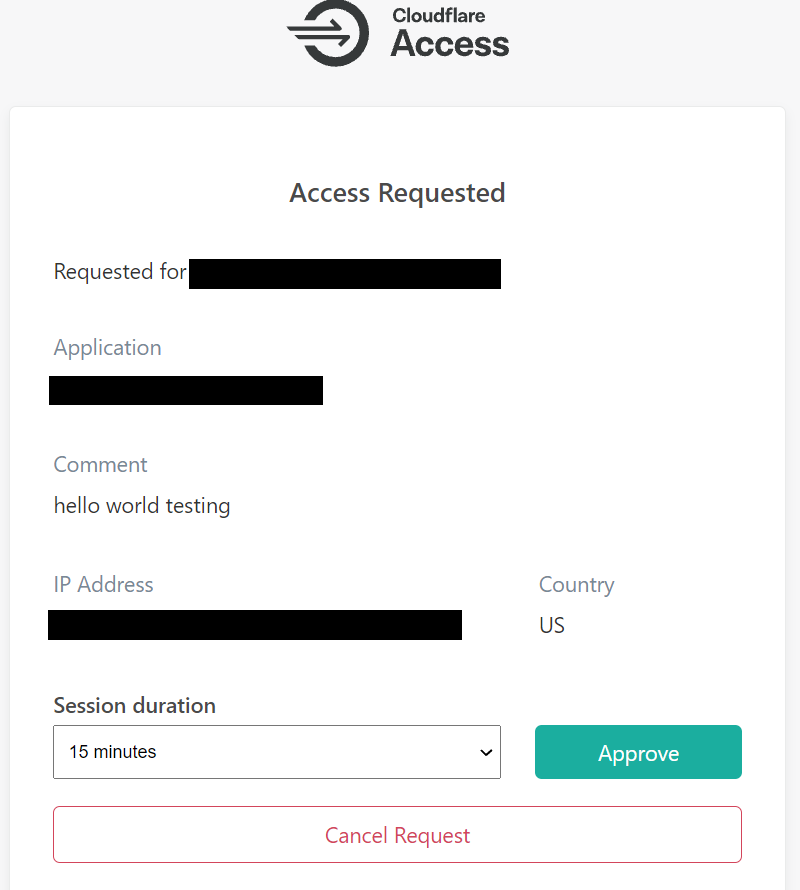
Announcing Access Temporary Authentication Instead of sharing static credentials, your team can request temporary access through infisical, which is then brokered through a secure gateway with full auditing and session recording. Infisical is the all in one identity security platform for developers, machines, and ai agents. manage identities, secrets, certs, and access.
Comments are closed.