Table 2 From Classifying Tor Traffic Encrypted Payload Using Machine
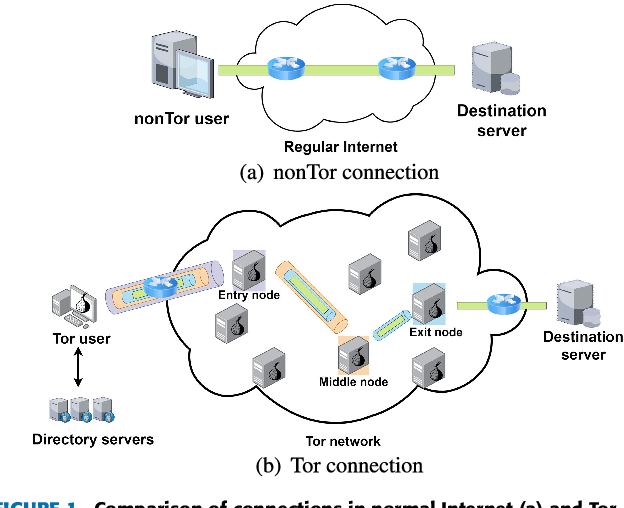
Figure 1 From Classifying Tor Traffic Encrypted Payload Using Machine We introduced a novel method using deep packet inspection and machine learning to differentiate between tor and nontor traffic based solely on encrypted payload. This study contributes to the efficient classification of tor and nontor traffic through features derived solely from a single encrypted payload packet, independent of its position in the traffic flow.
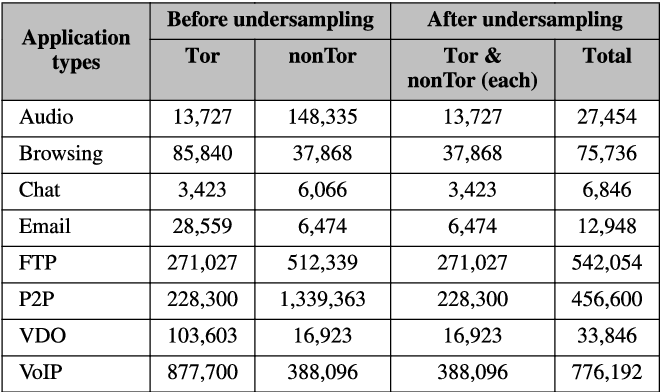
Table 2 From Classifying Tor Traffic Encrypted Payload Using Machine In the second strand of our research, we aimed to distinguish tor and nontor traffic using machine learning, based on encrypted payload features. Using deep packet inspection and machine learning, we presented a novel technique that distinguishes tor traffic from non tor traffic based only on the encrypted payload. This study contributes to the efficient classification of tor and nontor traffic through features derived solely from a single encrypted payload packet, independent of its position in the traffic flow. Thereby, this study contributes to the efficient classification of tor and nontor traffic through features derived solely from a single encrypted payload packet, independent of its position in the traffic flow.

Figure 1 From Classifying Tor Traffic Encrypted Payload Using Machine This study contributes to the efficient classification of tor and nontor traffic through features derived solely from a single encrypted payload packet, independent of its position in the traffic flow. Thereby, this study contributes to the efficient classification of tor and nontor traffic through features derived solely from a single encrypted payload packet, independent of its position in the traffic flow. Classifying tor traffic encrypted payload using machine learning tor provides internet anonymity with both beneficial and harmful uses, highlighting the need for effective traffic monitoring. Abstract publication: ieee access pub date: 2024 doi: 10.1109 access.2024.3356073 bibcode: 2024ieeea 1219418c full text sources publisher |.
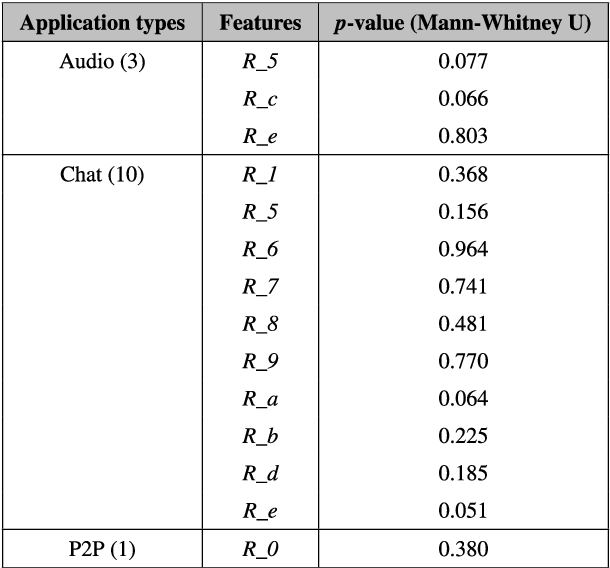
Table 1 From Classifying Tor Traffic Encrypted Payload Using Machine Classifying tor traffic encrypted payload using machine learning tor provides internet anonymity with both beneficial and harmful uses, highlighting the need for effective traffic monitoring. Abstract publication: ieee access pub date: 2024 doi: 10.1109 access.2024.3356073 bibcode: 2024ieeea 1219418c full text sources publisher |.
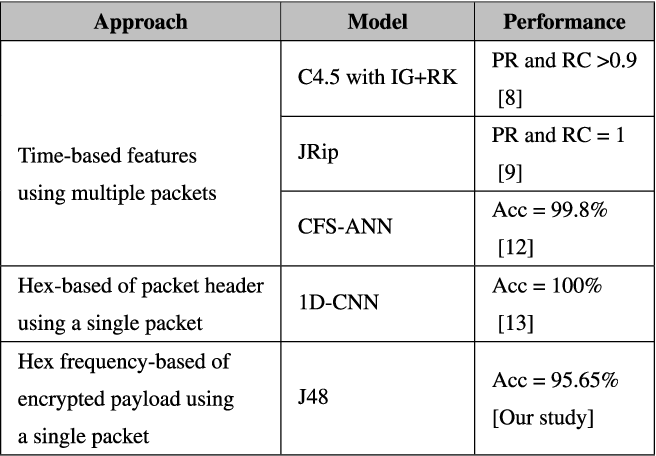
Table 1 From Classifying Tor Traffic Encrypted Payload Using Machine
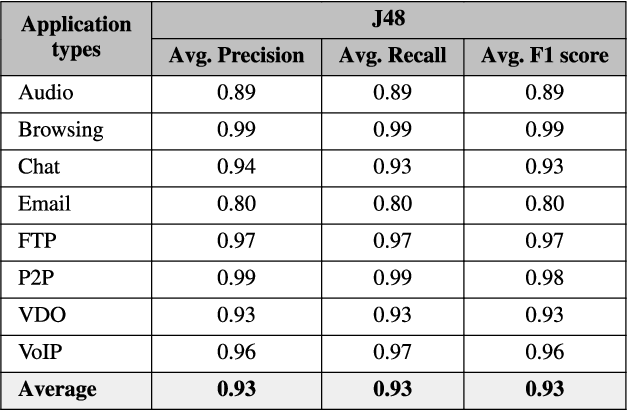
Table 1 From Classifying Tor Traffic Encrypted Payload Using Machine
Comments are closed.