Table 1 From Phishing Classification Techniques A Systematic

Advance Phishing Techniques Simplified Pdf Phishing Computer Therefore, this study aims to conduct a systematic review, to show a more crucial issue in phishing attacks, namely classification techniques. these issues were categorized into techniques,. Therefore, this study aims to conduct a systematic review, to show a more crucial issue in phishing attacks, namely classification techniques. these issues were categorized into techniques, datasets, performance evaluation, and phishing types.
A Literature Review On Classification Of Phishing Attacks Pdf A systematic review of techniques, datasets, performance evaluation, and phishing types is conducted to show a more crucial issue in phishing attacks, namely classification techniques. This document presents a systematic literature review on phishing classification techniques, highlighting the growing concern of phishing attacks over the past decade. Table 1 shows only three slrs published in the last five years about phishing website detection techniques in the five influential journals selected in the current study. A tech3 (visual cryptography and code generation techniques, 5%) was identified as one of the anti phishing technique by tanvi [24] which reported that it is an effective prevention technique to keep the internet users far away from the phishers.

Pdf Phishing Classification Techniques A Systematic Literature Review Table 1 shows only three slrs published in the last five years about phishing website detection techniques in the five influential journals selected in the current study. A tech3 (visual cryptography and code generation techniques, 5%) was identified as one of the anti phishing technique by tanvi [24] which reported that it is an effective prevention technique to keep the internet users far away from the phishers. Abstract publication: ieee access pub date: 2022 doi: 10.1109 access.2022.3166474 bibcode: 2022ieeea 1041574a full text sources publisher |. This study offers a thorough examination of phishing detection research done over the last 10 years, from 2015 to 2024. the study examines phishing attack types, detection techniques, including heuristic, list based, machine learning, and deep learning. Phishing continues to stand out as one of the foremost obstacles confronting online users, with a substantial number falling victim to it. researchers are activ. The thirteen most recent classification techniques used in preliminary phishing studies were compared and evaluated against ten performance measures. the results showed that the proposed schemes successfully uncover the maximum and minimum performance obtained by a classification technique.

Pdf Phishing Classification Techniques A Systematic Literature Review Abstract publication: ieee access pub date: 2022 doi: 10.1109 access.2022.3166474 bibcode: 2022ieeea 1041574a full text sources publisher |. This study offers a thorough examination of phishing detection research done over the last 10 years, from 2015 to 2024. the study examines phishing attack types, detection techniques, including heuristic, list based, machine learning, and deep learning. Phishing continues to stand out as one of the foremost obstacles confronting online users, with a substantial number falling victim to it. researchers are activ. The thirteen most recent classification techniques used in preliminary phishing studies were compared and evaluated against ten performance measures. the results showed that the proposed schemes successfully uncover the maximum and minimum performance obtained by a classification technique.
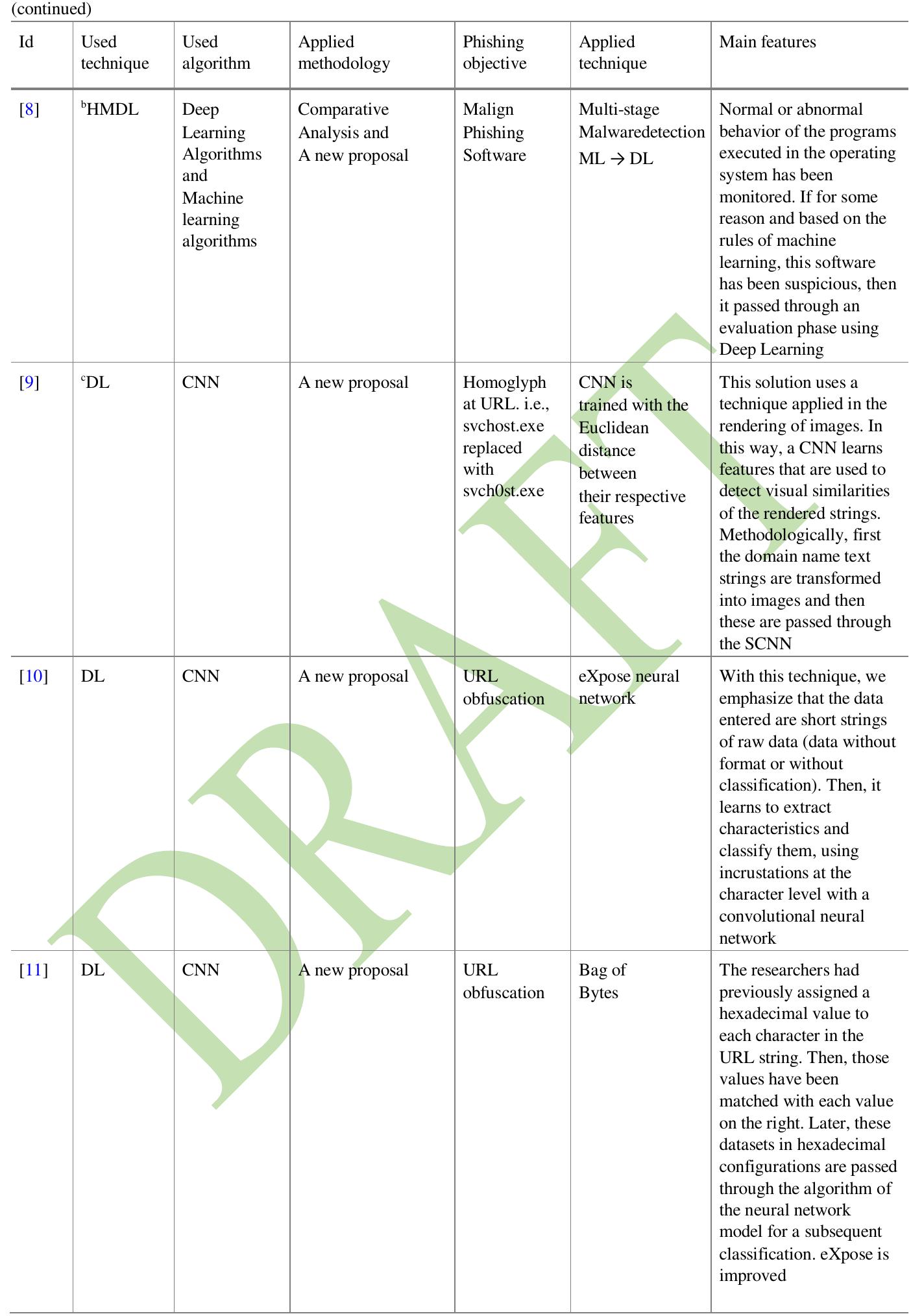
Table 1 Classification Of Phishing Attack Solutions By Phishing continues to stand out as one of the foremost obstacles confronting online users, with a substantial number falling victim to it. researchers are activ. The thirteen most recent classification techniques used in preliminary phishing studies were compared and evaluated against ten performance measures. the results showed that the proposed schemes successfully uncover the maximum and minimum performance obtained by a classification technique.
Comments are closed.