Symmetric Key Cryptography Pdf

Unit 2 Classical Symmetric Key Cryptography Pdf From shannon’s results, it is known that no perfect symmetric key encryption scheme exists, unless the length of the key is at least the sum of the lengths of all transmitted messages. This paper introduces a lightweight technique for symmetric key encryption of text, which utilizes less complex operations such as xor and permutation matrices.

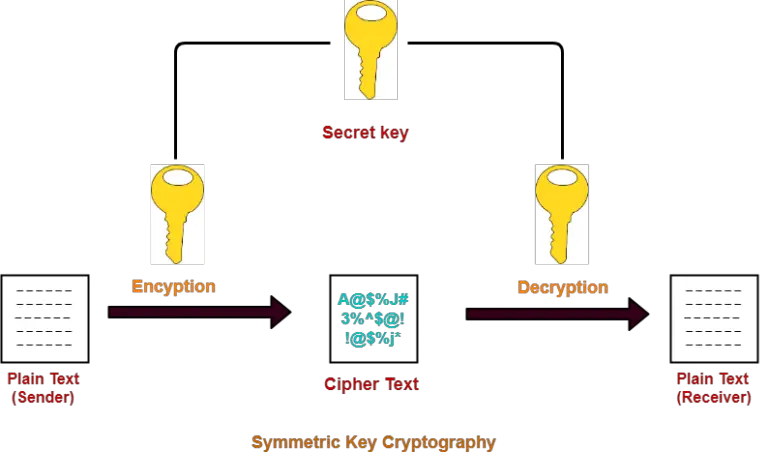
Lab01 Symmetric Cryptography Pdf Cryptography Encryption Designed by ibm in 1973 4, tweaked by the nsa, then became the us standard for encryption. international adoption followed. introduced in 1998, because 56 bit keys had become feasible to brute force. A recommended choice: aes counter mode cmac (or hmac), encrypt then mac. gives cca security, and provides authentication. This paper describes cryptography, various symmetric key algorithms in detail and then proposes a new symmetric key algorithm. algorithms for both encryption and decryption are provided here. Abstract symmetric key cryptography is a method used to keep information safe. it uses one secret key to both lock and unlock data. this paper explains how symmetric key cryptography works, talks about popular algorithms like des and aes, and shows where it is used in real life.

Unit 2 Symmetric Key Pdf Cryptography Key Cryptography This paper describes cryptography, various symmetric key algorithms in detail and then proposes a new symmetric key algorithm. algorithms for both encryption and decryption are provided here. Abstract symmetric key cryptography is a method used to keep information safe. it uses one secret key to both lock and unlock data. this paper explains how symmetric key cryptography works, talks about popular algorithms like des and aes, and shows where it is used in real life. Secret (symmetric) key functions: one key shared secret key is used for both encryption and decryption. The document discusses symmetric key cryptography and concepts related to symmetric key ciphers. it covers the mathematics behind symmetric key cryptography such as modular arithmetic, groups, rings, and finite fields. The key is shared via a “secured channel” symmetric ciphers are of two types: block : the plaintext is encrypted in blocks stream: the block length is 1 symmetric ciphers are used for bulk encryption, as they have better performance than their asymmetric counter part. This chapter gives an introduction to symmetric key cryptography and its sub groups – block ciphers and stream ciphers. we also provide short descriptions of the most commonly used algorithms in industry: des and aes. we will focus on their special properties from an implementation point of view.

Cyber Security Lab Symmetric Key Encryption Techniques Pdf Cipher Secret (symmetric) key functions: one key shared secret key is used for both encryption and decryption. The document discusses symmetric key cryptography and concepts related to symmetric key ciphers. it covers the mathematics behind symmetric key cryptography such as modular arithmetic, groups, rings, and finite fields. The key is shared via a “secured channel” symmetric ciphers are of two types: block : the plaintext is encrypted in blocks stream: the block length is 1 symmetric ciphers are used for bulk encryption, as they have better performance than their asymmetric counter part. This chapter gives an introduction to symmetric key cryptography and its sub groups – block ciphers and stream ciphers. we also provide short descriptions of the most commonly used algorithms in industry: des and aes. we will focus on their special properties from an implementation point of view.
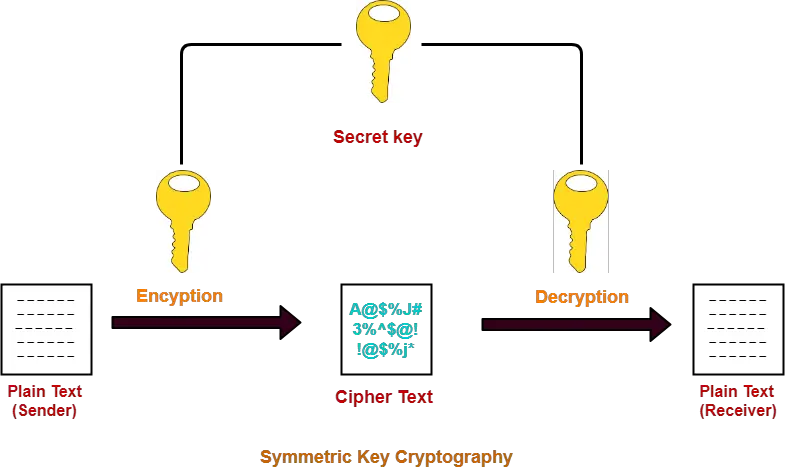
Symmetric Key Cryptography Cryptography Techniques Gate Vidyalay The key is shared via a “secured channel” symmetric ciphers are of two types: block : the plaintext is encrypted in blocks stream: the block length is 1 symmetric ciphers are used for bulk encryption, as they have better performance than their asymmetric counter part. This chapter gives an introduction to symmetric key cryptography and its sub groups – block ciphers and stream ciphers. we also provide short descriptions of the most commonly used algorithms in industry: des and aes. we will focus on their special properties from an implementation point of view.
Symmetric Key Cryptography Cryptography Techniques Gate Vidyalay
Comments are closed.