Studybyyourself Chapter 3 Asymmetric Cryptography
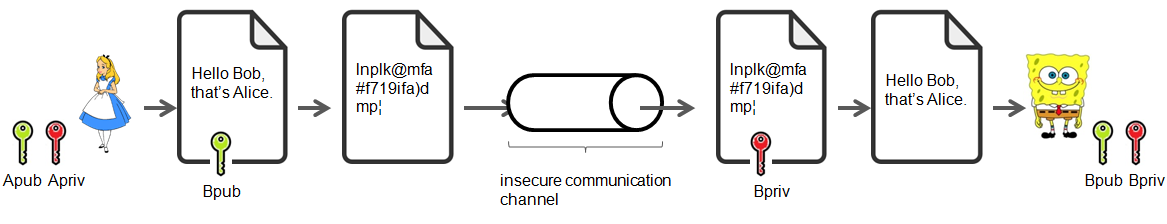
Studybyyourself Chapter 3 Asymmetric Cryptography Asymmetric cryptography (or public key cryptography) has been called that way since the key for encrypting differs from the key for decrypting the ciphertext. in asymmetric cryptography each entity owns two keys, the public key and the private key. In a diffie hellman key exchange, alice and bob have chosen prime value q = 17 and primitive root = 5.
Studybyyourself Chapter 3 Asymmetric Cryptography Chapter 3 discusses asymmetric encryption, a cryptographic method using a public and private key for secure communication. it covers the principles of public key cryptography, the rsa cryptosystem, and key management strategies for distributing public keys. Explore the fundamentals of asymmetric key cryptography, including rsa, diffie hellman, and elliptic curve techniques for secure communication. Starting with a little bit of history of this revolutionary method of encryption decryption, we will look at different types of asymmetric algorithms and how they help secure our credit cards, identity, and data. Asymmetric cryptography is a core part of many cryptographic applications. for example, it allows for encrypting messages, exchanging secret keys over an insecure channel, and establishing.

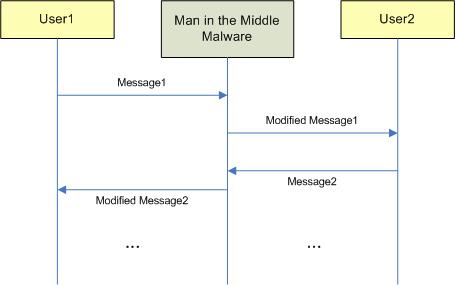
What Is Asymmetric Cryptography Starting with a little bit of history of this revolutionary method of encryption decryption, we will look at different types of asymmetric algorithms and how they help secure our credit cards, identity, and data. Asymmetric cryptography is a core part of many cryptographic applications. for example, it allows for encrypting messages, exchanging secret keys over an insecure channel, and establishing. This cryptographic system addresses two major challenges faced in traditional (symmetric) cryptography: key distribution and digital signatures. asymmetric algorithms use one key for encrypting data and another, related key for decrypting it. It explains the processes involved in various encryption algorithms, including symmetric and asymmetric key encryption, emphasizing the importance of digital signatures and the roles of hashing functions and asymmetric cryptography in secure electronic communications. Read and download cryptography chapter 3 – asymmetric ciphers notes for bsc csit fifth semester. free pdf study materials for tribhuvan university tu exams. The present tutorial explains how cryptography evolved over the time. it highlights why a cryptographic concept has been completed by another one for correcting its weakness.
Comments are closed.