Ch10 Asymmetric Cryptography Pdf
Asymmetric Cryptography Notes Pdf Pdf Public Key Cryptography Ch10 asymmetric cryptography free download as pdf file (.pdf), text file (.txt) or view presentation slides online. Symmetrickey cryptography is appropriate for long messages, and the speed of encryption decryption is fast. asymmetrickey cryptography is appropriate for short messages, and the speed of encryption decryption is slow.

Ch10 Asymmetric Cryptography Pdf Lecture notes for chris peikert's graduate level theory of cryptography course theoryofcryptography lec10 asymmetric encryption.pdf at master · cpeikert theoryofcryptography. Asymmetric key cryptography is still needed for authentication, digital signatures, and secret key exchanges. asymmetric key cryptography is normally used to encrypt or decrypt small pieces of information, such as the cipher key for a symmetric key cryptography. Convention: alicekazam is sending encrypted messages to bobasaur, bobasaur is decrypting them, and eevee is an eavesdropper who overhears everything being sent, but hopefully still can’t understand it. an encryption method together with a decryption method is known as a cryptographic scheme. While encryption is probably the most prominent example of a crypto graphic problem, modern cryptography is much more than that. in this class, we will learn about pseudorandom number generators, digital signatures, zero knowledge proofs, multi party computation, to name just a few examples.

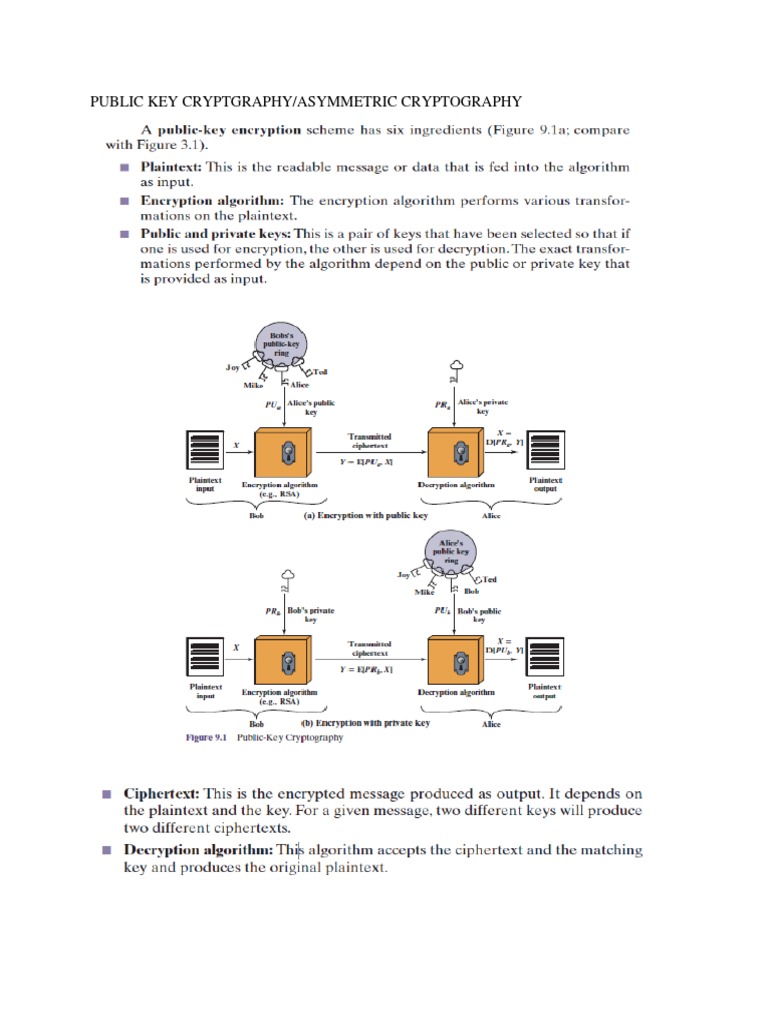
3 2 Asymmetric Key Cryptography Pdf Public Key Cryptography Convention: alicekazam is sending encrypted messages to bobasaur, bobasaur is decrypting them, and eevee is an eavesdropper who overhears everything being sent, but hopefully still can’t understand it. an encryption method together with a decryption method is known as a cryptographic scheme. While encryption is probably the most prominent example of a crypto graphic problem, modern cryptography is much more than that. in this class, we will learn about pseudorandom number generators, digital signatures, zero knowledge proofs, multi party computation, to name just a few examples. Pdf | cryptography enables us to store sensitive information or transmit it across insecure networks so that it cannot be read by anyone except the | find, read and cite all the research you. In today's lecture, we will explore how cryptography motivates solutions to the security concerns we discussed in monday's lecture. to do so, we will discuss: cryptography is the study of secure communication techniques in the presence of an adversary. others from understanding that same message. Symmetric: same key used for encryption and decryption asymmetric: for encryption a different key is used for encryption and decryption. Cryptographic checksums projection functions, and map a variable input length to a fixed output s ly strong and useful, hash f h must be easy to compute.

Asymmetric Crypto Pdf Public Key Cryptography Key Cryptography Pdf | cryptography enables us to store sensitive information or transmit it across insecure networks so that it cannot be read by anyone except the | find, read and cite all the research you. In today's lecture, we will explore how cryptography motivates solutions to the security concerns we discussed in monday's lecture. to do so, we will discuss: cryptography is the study of secure communication techniques in the presence of an adversary. others from understanding that same message. Symmetric: same key used for encryption and decryption asymmetric: for encryption a different key is used for encryption and decryption. Cryptographic checksums projection functions, and map a variable input length to a fixed output s ly strong and useful, hash f h must be easy to compute.

Asymmetric Encryption Pdf Public Key Cryptography Cryptography Symmetric: same key used for encryption and decryption asymmetric: for encryption a different key is used for encryption and decryption. Cryptographic checksums projection functions, and map a variable input length to a fixed output s ly strong and useful, hash f h must be easy to compute.
Comments are closed.