Structured Exception Handler Exploitation Pdf Software Computer

Structured Exception Handler Exploitation Pdf Software Computer Structured exception handler exploitation free download as pdf file (.pdf) or view presentation slides online. the seh exploitation technique was publicly documented by david litchfield september, 2003. Structured exception handling blocks of code are encapsulated, with each block having one or more associated handlers. each handler specifies some form of filter condition on the type of exception it handles.
Exception Handling Pdf This paper is written to discuss the design and theory of how a structured exception handler (seh) exploit can be written to target a windows host. we use the buffer overflow vulnerability in the esf easychat server software as a detailed example of this exploit type. If the reader already understands how struc tured exception handling works and can be exploited, feel free to skip ahead. the design of the technique that is the focus of this paper will be described in chapter 3 followed by a description of a proof of concept implementation in chapter 4. A tutorial on bayesian optimization of expensive cost functions, with application to active user modeling and hierarchical reinforcement learning 12th dec 2016 (bayopt).pdf. To reveal which combinations of the known protection mechanisms for seh overwrites are really effective. on the way to the goal, i will show you that we can bypass safeseh and software dep and hardware dep and sehop, all at the same time, under certain conditions.
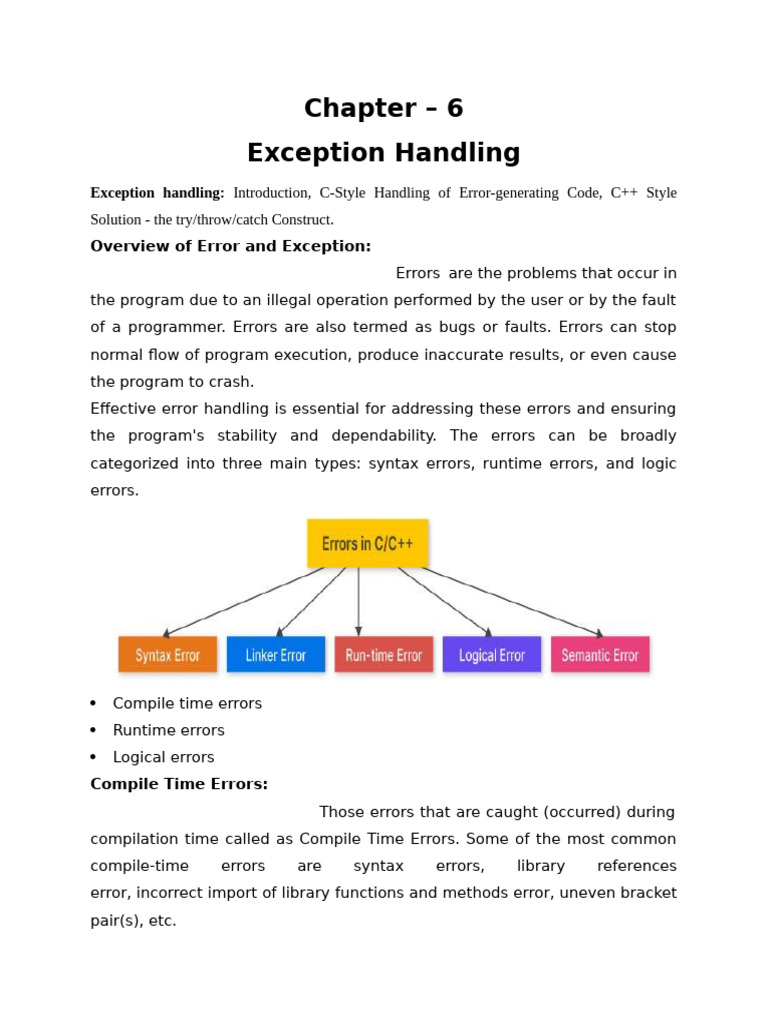
Exception Handling Pdf Computer Program Programming A tutorial on bayesian optimization of expensive cost functions, with application to active user modeling and hierarchical reinforcement learning 12th dec 2016 (bayopt).pdf. To reveal which combinations of the known protection mechanisms for seh overwrites are really effective. on the way to the goal, i will show you that we can bypass safeseh and software dep and hardware dep and sehop, all at the same time, under certain conditions. In exploitation of application which is using seh (structured exception handling), there are multiple ways to bypass it in this experiment techniques we are discussing about cases of seh. Structured exception handler exploitation · structured exception handling • blocks of code are encapsulated, with each block having one or more associated handlers. The purpose of the sehop mitigation is to prevent an attacker from being able to make use of the structured exception handler (seh) overwrite exploitation technique. While handling an exception, windows transfers control to exception handlers, following the seh chain. our first exception handler has been overwritten and the execution flow is redirected onto the « pop pop ret » sequence (instead of really handling the exception).

Exception Handling Pdf Software Systems Architecture In exploitation of application which is using seh (structured exception handling), there are multiple ways to bypass it in this experiment techniques we are discussing about cases of seh. Structured exception handler exploitation · structured exception handling • blocks of code are encapsulated, with each block having one or more associated handlers. The purpose of the sehop mitigation is to prevent an attacker from being able to make use of the structured exception handler (seh) overwrite exploitation technique. While handling an exception, windows transfers control to exception handlers, following the seh chain. our first exception handler has been overwritten and the execution flow is redirected onto the « pop pop ret » sequence (instead of really handling the exception).
Exception Handling 2 Pdf Java Programming Language Computer The purpose of the sehop mitigation is to prevent an attacker from being able to make use of the structured exception handler (seh) overwrite exploitation technique. While handling an exception, windows transfers control to exception handlers, following the seh chain. our first exception handler has been overwritten and the execution flow is redirected onto the « pop pop ret » sequence (instead of really handling the exception).
Comments are closed.