Stegi Secure Data Sharing Initial Demo

Ensuring Secure Data Sharing In Cloud Data Stores Secupi A modern, educational and professional communication platform focused on security and usability. visit stegi.kodextech.prismdigitalc more. "empowering business growth through digital innovation"providing digital and technological solutions for businesses through research, training, software deve.
Secure Data Sharing Implementing Access Intelligence And Controls A user‑friendly communication channel to hide and reveal messages in an image. visit stegi.kodextech.prismdigitalco #datasecurity #dataprotection. Imagine embedding messages inside images—simple, smart, and secure. 🎥 just launched our latest video showcasing how stegi makes data protection effortless for everyone. Unified identity security platform end to end identity security products including iam, pam, and iga empowering you to protect access, control privilege access, and govern identities confidence. know more. This project is a secure peer to peer (p2p) messaging and file sharing system with end to end encryption, user authentication, access controls, and audit trails.

Securiti On Linkedin Secure Data Sharing Implementing Access Unified identity security platform end to end identity security products including iam, pam, and iga empowering you to protect access, control privilege access, and govern identities confidence. know more. This project is a secure peer to peer (p2p) messaging and file sharing system with end to end encryption, user authentication, access controls, and audit trails. When you send this link, the user on the other side can try out the model in their browser. because the processing happens on your device (as long as your device stays on), you don't have to worry about any packaging any dependencies. a share link usually looks something like this: 07ff8706ab.gradio.live. Learn how to use delta sharing for secure data and ai asset sharing with users outside your organization or on different metastores within your azure databricks account. In this blog, we’ll explore what it means to share information securely, the most common challenges to doing so, and best practices for incorporating data security into data sharing processes. The seq docker container stores configuration and log events in its data directory. for this directory to survive container restarts, it needs to be mapped to a persistent volume using v on the command line, as in the example above.

Block Diagram Of Proposed Secure Data Sharing In A Cloud Environment When you send this link, the user on the other side can try out the model in their browser. because the processing happens on your device (as long as your device stays on), you don't have to worry about any packaging any dependencies. a share link usually looks something like this: 07ff8706ab.gradio.live. Learn how to use delta sharing for secure data and ai asset sharing with users outside your organization or on different metastores within your azure databricks account. In this blog, we’ll explore what it means to share information securely, the most common challenges to doing so, and best practices for incorporating data security into data sharing processes. The seq docker container stores configuration and log events in its data directory. for this directory to survive container restarts, it needs to be mapped to a persistent volume using v on the command line, as in the example above.
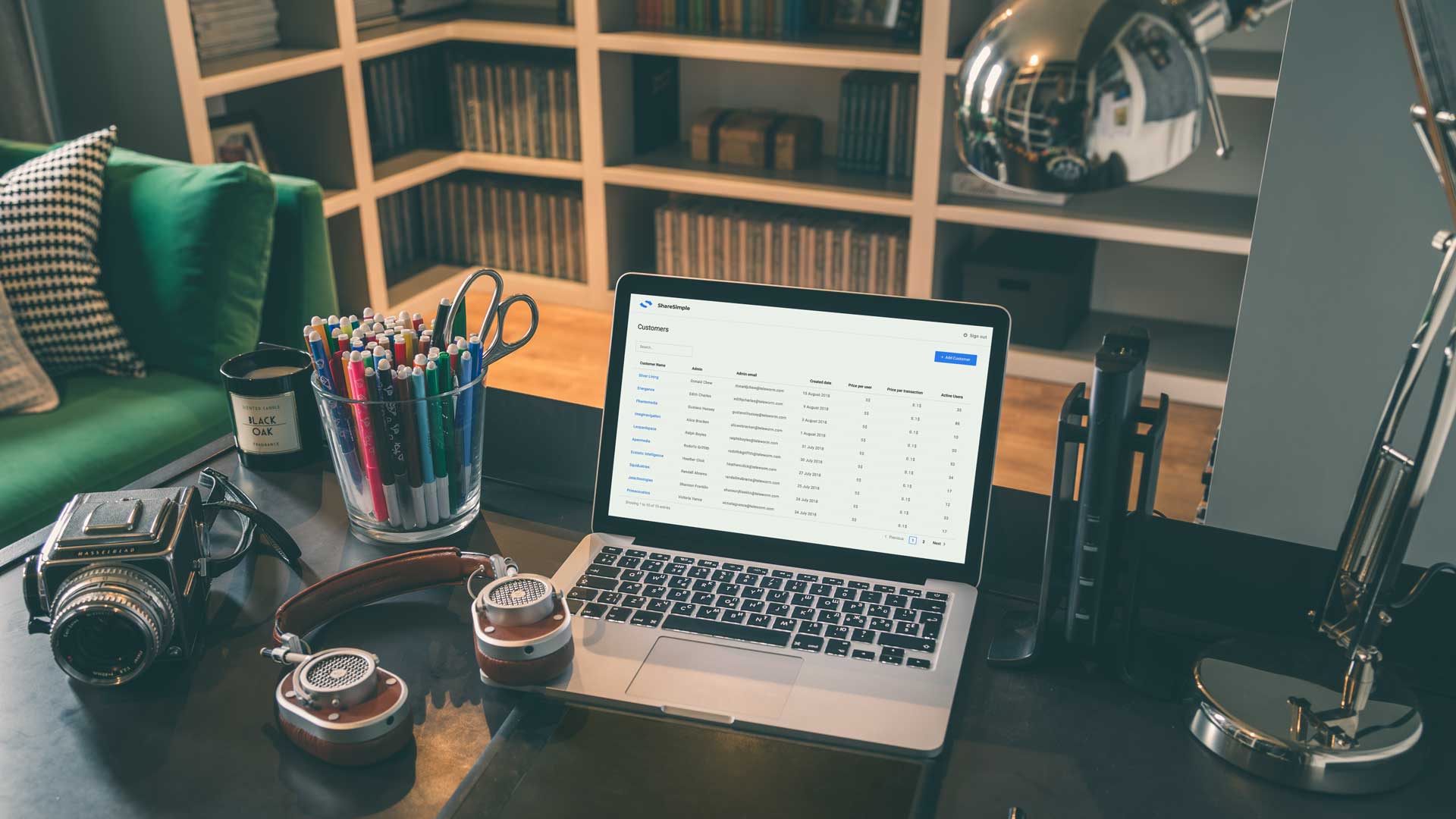
Software Solution For Secure Data Sharing In this blog, we’ll explore what it means to share information securely, the most common challenges to doing so, and best practices for incorporating data security into data sharing processes. The seq docker container stores configuration and log events in its data directory. for this directory to survive container restarts, it needs to be mapped to a persistent volume using v on the command line, as in the example above.

Pdf Secure Data Transfer Using Image Steganography
Comments are closed.