Sqlmap And Authentication Bypass Exploiting Login Forms
Bypass Admin Login With Sql Injections Sqlmap By 49 Off Learn how to ethically perform an authentication bypass using sqlmap—discover the flaws, test the limits, and secure login forms before attackers do. Sqlmap is a powerful automated tool that allows penetration testers and ethical hackers to test for and exploit sql injection vulnerabilities, especially in login forms. in this article, we will provide a detailed guide on how to exploit a vulnerable login form using sqlmap.

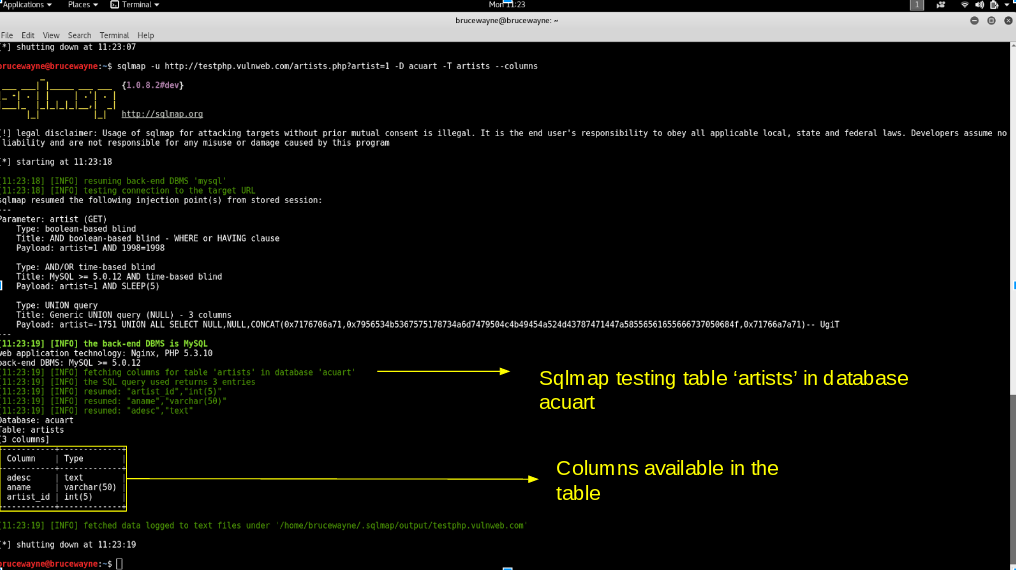
Bypass Admin Login With Sql Injections Sqlmap By 49 Off Sanjay ghosh posted on apr 24 sql injection explained: how hackers bypass login forms (and how to stop them) # security # cybersecurity # webdev # sql even today, a single poorly written sql query can allow an attacker to bypass authentication or expose sensitive data. and the scary part? it often comes down to just one line of code. This time, i focused on testing multiple endpoints of the same application — each one mimicking real world patterns seen in login forms, user registration, admin panels, and search interfaces. Sql injection is a technique used to exploit user data through web page inputs by injecting sql commands as statements. basically, these statements can be used to manipulate the application’s web server by malicious users. sql injection is a code injection technique that might destroy your database. Sqlmap is a widely used open source tool that automates the process of detecting and exploiting sql injection vulnerabilities in web applications. the guide explains the steps required to use sqlmap against a web application that requires user authentication.

Using Sql Injection To Bypass Authentication Jhonatan Silva Dio Sql injection is a technique used to exploit user data through web page inputs by injecting sql commands as statements. basically, these statements can be used to manipulate the application’s web server by malicious users. sql injection is a code injection technique that might destroy your database. Sqlmap is a widely used open source tool that automates the process of detecting and exploiting sql injection vulnerabilities in web applications. the guide explains the steps required to use sqlmap against a web application that requires user authentication. A recently disclosed critical bug in the truehr login portal demonstrates how a single malicious input in the username parameter can completely bypass password verification, granting unauthorized attackers access to sensitive hr data in production environments. In this tutorial, you will come to across how to perform a sql injection attack on a login form of any website. there are so many examples related to login form like facebook login, gmail login, and other online accounts. Using sqlmap with session cookies provides penetration testers with a powerful tool to detect and exploit sql injection vulnerabilities in login protected web applications. Solid intro comparing sqlmap and ghauri from a real world waf bypass perspective is exactly what practitioners need, especially with modern defenses getting trickier.
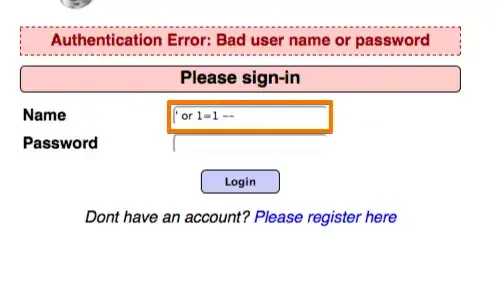
Using Sql Injection To Bypass Authentication Jhonatan Silva Dio A recently disclosed critical bug in the truehr login portal demonstrates how a single malicious input in the username parameter can completely bypass password verification, granting unauthorized attackers access to sensitive hr data in production environments. In this tutorial, you will come to across how to perform a sql injection attack on a login form of any website. there are so many examples related to login form like facebook login, gmail login, and other online accounts. Using sqlmap with session cookies provides penetration testers with a powerful tool to detect and exploit sql injection vulnerabilities in login protected web applications. Solid intro comparing sqlmap and ghauri from a real world waf bypass perspective is exactly what practitioners need, especially with modern defenses getting trickier.

Sql Authentication Bypass Pdf Data Management Computer Security Using sqlmap with session cookies provides penetration testers with a powerful tool to detect and exploit sql injection vulnerabilities in login protected web applications. Solid intro comparing sqlmap and ghauri from a real world waf bypass perspective is exactly what practitioners need, especially with modern defenses getting trickier.
Comments are closed.