Solved Question 4 Write Two Methods Encrypt Message Key Chegg
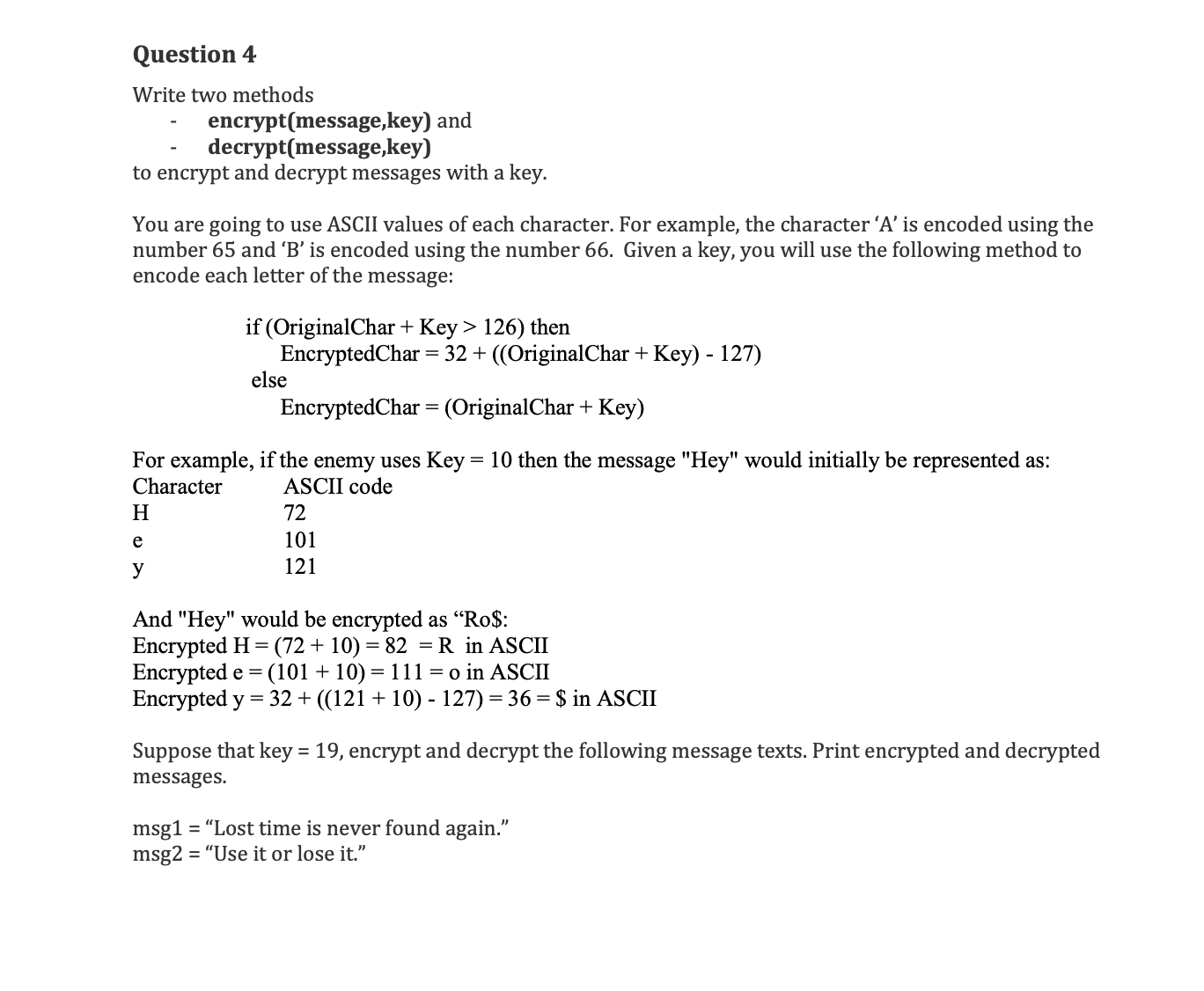
Solved Question 4 Write Two Methods Encrypt Message Key Chegg Question: question 4 write two methods encrypt (message,key) and decrypt (message,key) to encrypt and decrypt messages with a key. you are going to use ascii values of each character. Solution for write two methods encrypt (message,key) and decrypt (message,key) to encrypt and decrypt messages with a key.
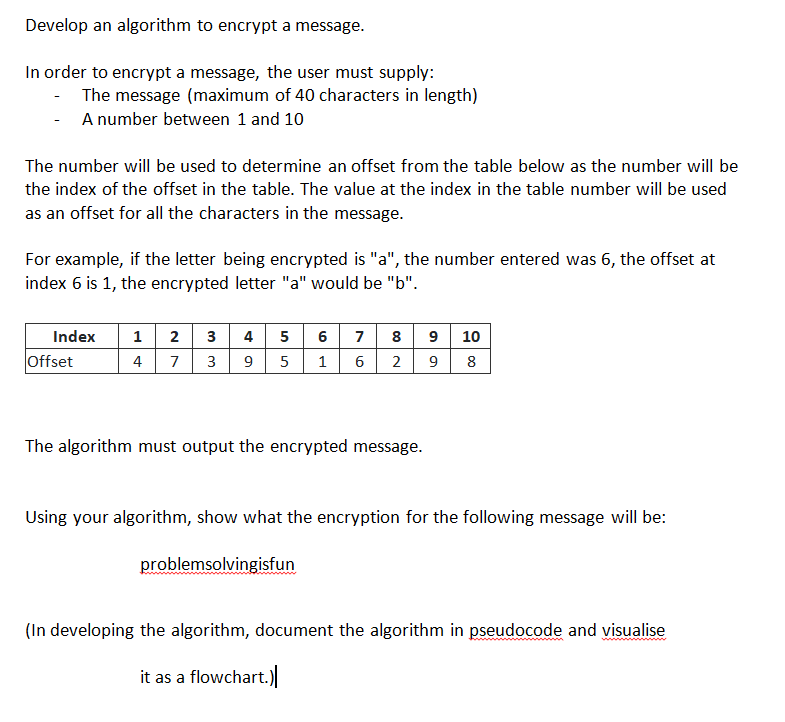
Solved Develop An Algorithm To Encrypt A Message In Order Chegg Write two methods encrypt (message, key) and decrypt (message, key) to encrypt and decrypt messages with a key. you are going to use ascii values of each character. Write two methods encrypt (message,key) and decrypt (message,key) to encrypt and decrypt messages with a key. Question: a question 4 write two methods encrypt (message.key) and decrypt (message,key) to encrypt and decrypt messages with a key. you are going to use ascii values of each character. for example, the character 'a' is encoded using the number 65 and 'b' is encoded using the number 66. Write two methods encrypt (message,key) and decrypt (message,key) to encrypt and decrypt messages with a key. you are going to use ascii values of each character. for example, the character 'a' is encoded using the number 65 and 'b' is encoded using the number 66.
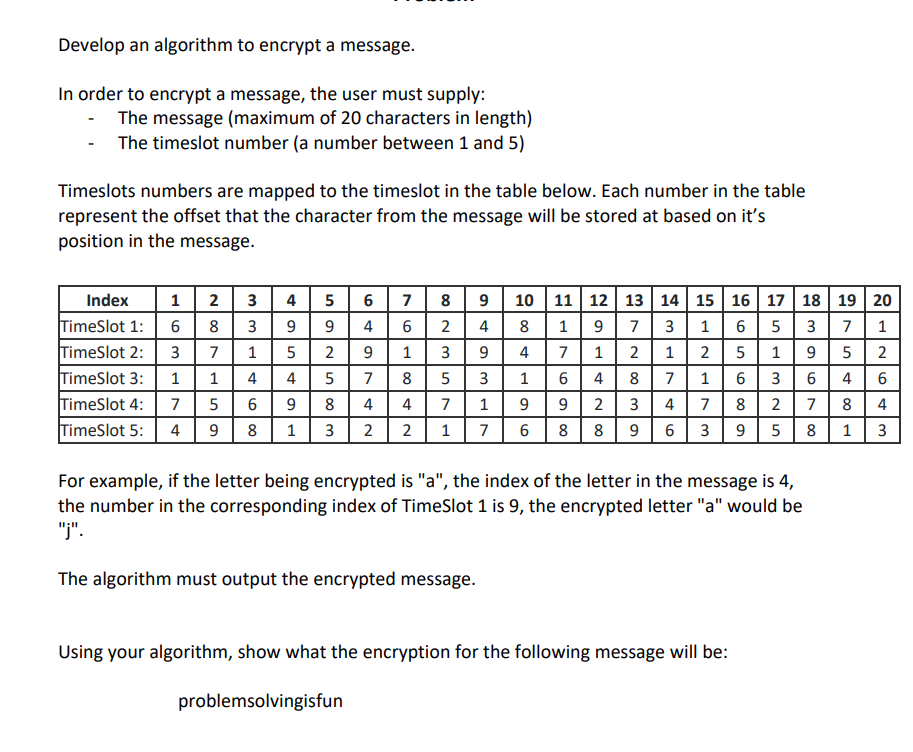
Solved Develop An Algorithm To Encrypt A Message In Order Chegg Question: a question 4 write two methods encrypt (message.key) and decrypt (message,key) to encrypt and decrypt messages with a key. you are going to use ascii values of each character. for example, the character 'a' is encoded using the number 65 and 'b' is encoded using the number 66. Write two methods encrypt (message,key) and decrypt (message,key) to encrypt and decrypt messages with a key. you are going to use ascii values of each character. for example, the character 'a' is encoded using the number 65 and 'b' is encoded using the number 66. Question: write two methods encrypt (message,key) and decrypt (message,key) to encrypt and decrypt messages with a key. you are going to use ascii values of each character. for example, the character ‘a’ is encoded using the number 65 and ‘b’ is encoded using the number 66. In this exercise we shall encrypt and decrypt a text message using a symmetric cipher aes cbc 256, combined with scrypt password to key derivation and hmac message authentication code. Solved: write two methods to encrypt or decrypt a file by shifting each of its bytes by a certain value (the key). We will explore how to encrypt a message so that only the intended recipient can decrypt and read it. there are two primary methods for achieving this: ⚖️ symmetric cryptography: in this method, the same key is used for both encryption and decryption. this approach has been used since roman times.
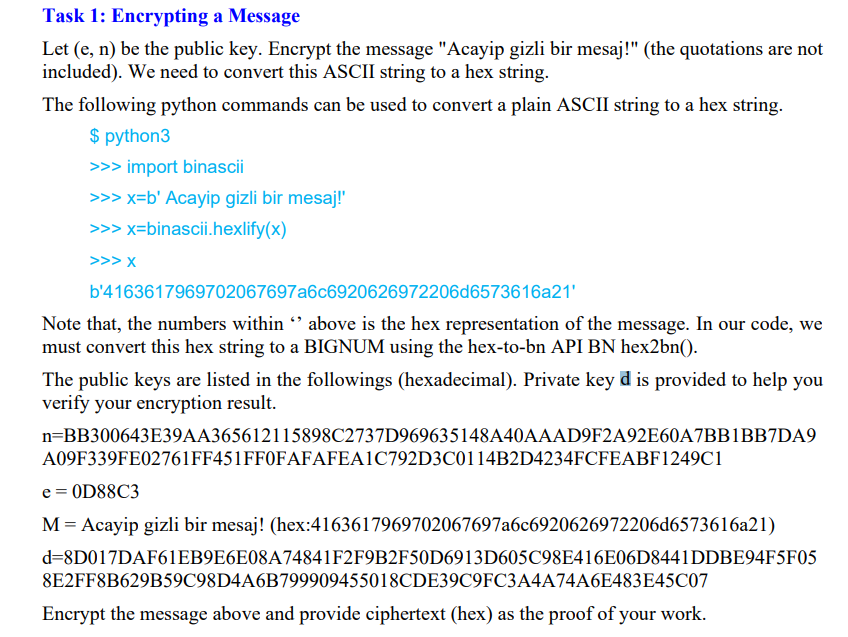
Solved Task 1 Encrypting A Message Let E N Be The Public Chegg Question: write two methods encrypt (message,key) and decrypt (message,key) to encrypt and decrypt messages with a key. you are going to use ascii values of each character. for example, the character ‘a’ is encoded using the number 65 and ‘b’ is encoded using the number 66. In this exercise we shall encrypt and decrypt a text message using a symmetric cipher aes cbc 256, combined with scrypt password to key derivation and hmac message authentication code. Solved: write two methods to encrypt or decrypt a file by shifting each of its bytes by a certain value (the key). We will explore how to encrypt a message so that only the intended recipient can decrypt and read it. there are two primary methods for achieving this: ⚖️ symmetric cryptography: in this method, the same key is used for both encryption and decryption. this approach has been used since roman times.
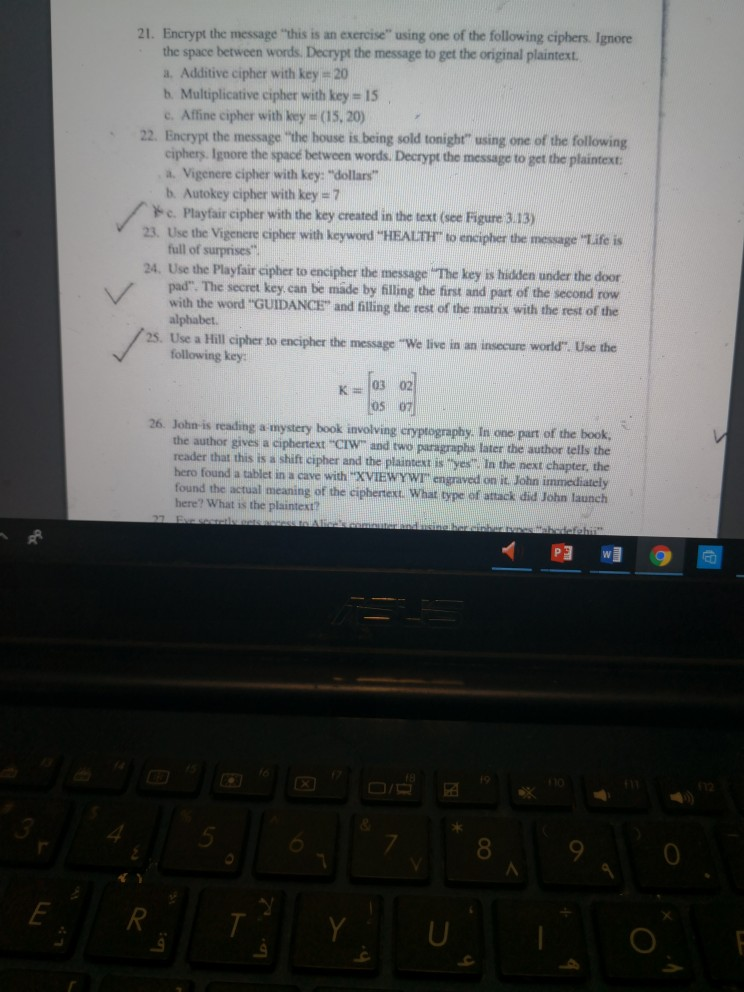
Solved 21 Encrypt The Message This Is An Exercise Using Chegg Solved: write two methods to encrypt or decrypt a file by shifting each of its bytes by a certain value (the key). We will explore how to encrypt a message so that only the intended recipient can decrypt and read it. there are two primary methods for achieving this: ⚖️ symmetric cryptography: in this method, the same key is used for both encryption and decryption. this approach has been used since roman times.

Answered Write Two Methods Encrypt Message Key And Decrypt Message
Comments are closed.