Solved Blockchain Technology Assignment 2 Code A Hash Chegg
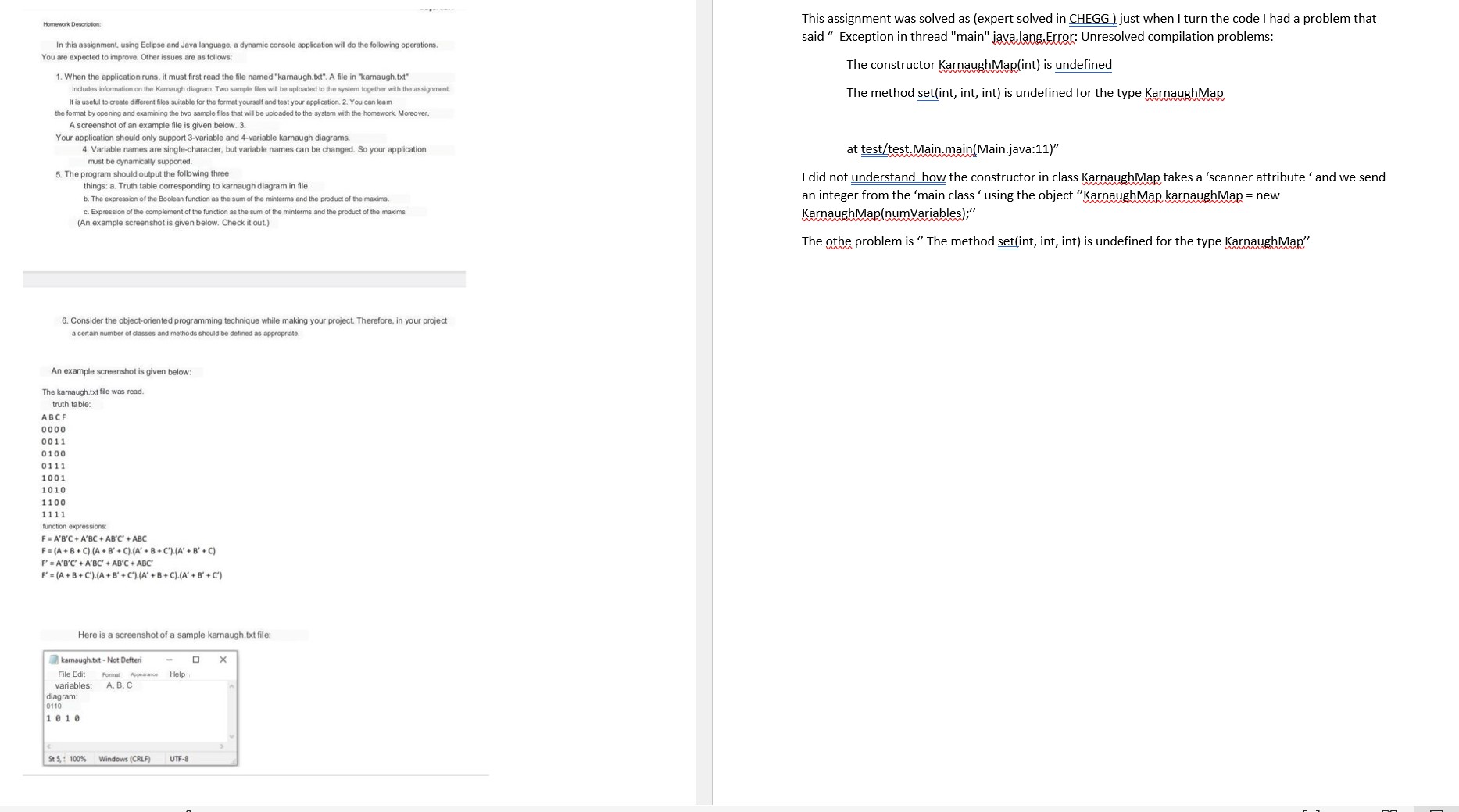
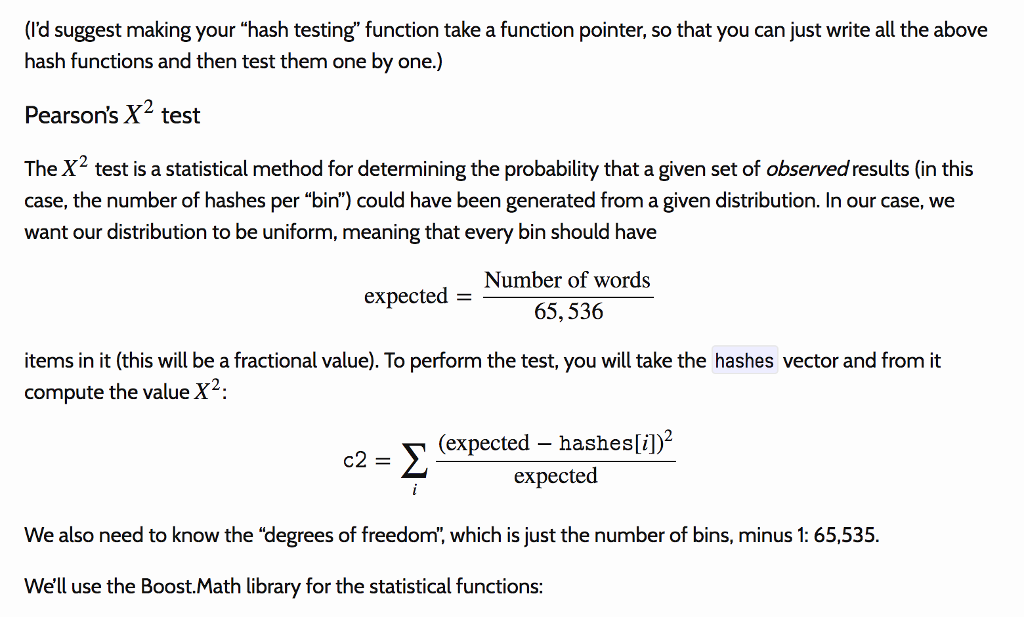
Solved Question Chegg There are 2 steps to solve this one. blockchain technology assignment # 2 code a hash function in any language and match result with four standards. The document outlines a comprehensive assignment on blockchain technology, covering various topics such as the avalanche effect, types of blockchain, consensus mechanisms, and the double spending problem.
Solved Blockchain Technology Assignment 2 Code A Hash Chegg Discover the byzantine generals problem and its impact on blockchain consensus mechanisms, including bitcoin mining and transaction processes. I recognize the time people spend on building intuition, understanding new concepts, solving quizzes and assignments in this course. the solutions uploaded here are only for reference purpose. Bct assignment 2 free download as pdf file (.pdf), text file (.txt) or read online for free. the document is an assignment for the department of cse at east west institute of technology, focusing on blockchain technology. Blockchain is an encrypted and publicly available database in which new blocks must be recognized by existing nodes in the chain before entering the blockchain system. this "consensus mechanism" increases data storage and distribution’s security while eliminating the role of intermediator.

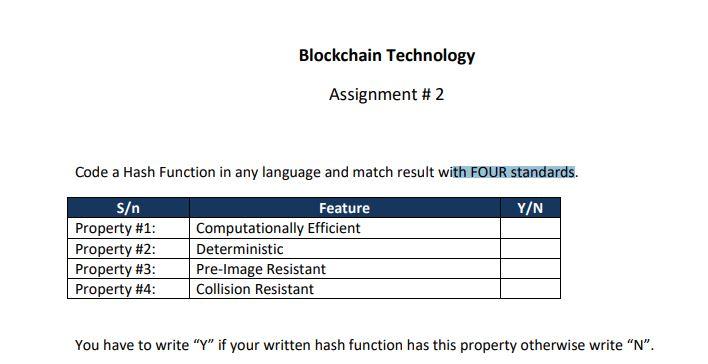
Assignment Hash Functions Finding Collisions And Chegg Bct assignment 2 free download as pdf file (.pdf), text file (.txt) or read online for free. the document is an assignment for the department of cse at east west institute of technology, focusing on blockchain technology. Blockchain is an encrypted and publicly available database in which new blocks must be recognized by existing nodes in the chain before entering the blockchain system. this "consensus mechanism" increases data storage and distribution’s security while eliminating the role of intermediator. Sha 256 is the most famous of all cryptographic hash functions because it’s used extensively in blockchain technology. the sha 256 hashing algorithm was developed by the national security agency (nsa) in 2001. The document discusses blockchain technology, focusing on its mining process and cryptographic principles. it highlights the role of hashing algorithms, particularly sha 256, in securing transactions and ensuring data integrity. This lab assignment explores various cryptographic techniques, including caesar and vigenère ciphers, des brute force attacks, password hashing, hmac signatures, blockchain implementation, and the vernam cipher. each section includes problem statements, solution codes, and terminal outputs, demonstrating practical applications of cryptography in python. This document contains a laboratory assignment on block chain technologies from lakshami narain college of technology excellence in bhopal, india. it includes two questions about bitcoin mining and the differences between bitcoin and ethereum blockchains.
Solved Data Structures In C Hash Functions Hello Chegg Chegg Sha 256 is the most famous of all cryptographic hash functions because it’s used extensively in blockchain technology. the sha 256 hashing algorithm was developed by the national security agency (nsa) in 2001. The document discusses blockchain technology, focusing on its mining process and cryptographic principles. it highlights the role of hashing algorithms, particularly sha 256, in securing transactions and ensuring data integrity. This lab assignment explores various cryptographic techniques, including caesar and vigenère ciphers, des brute force attacks, password hashing, hmac signatures, blockchain implementation, and the vernam cipher. each section includes problem statements, solution codes, and terminal outputs, demonstrating practical applications of cryptography in python. This document contains a laboratory assignment on block chain technologies from lakshami narain college of technology excellence in bhopal, india. it includes two questions about bitcoin mining and the differences between bitcoin and ethereum blockchains.
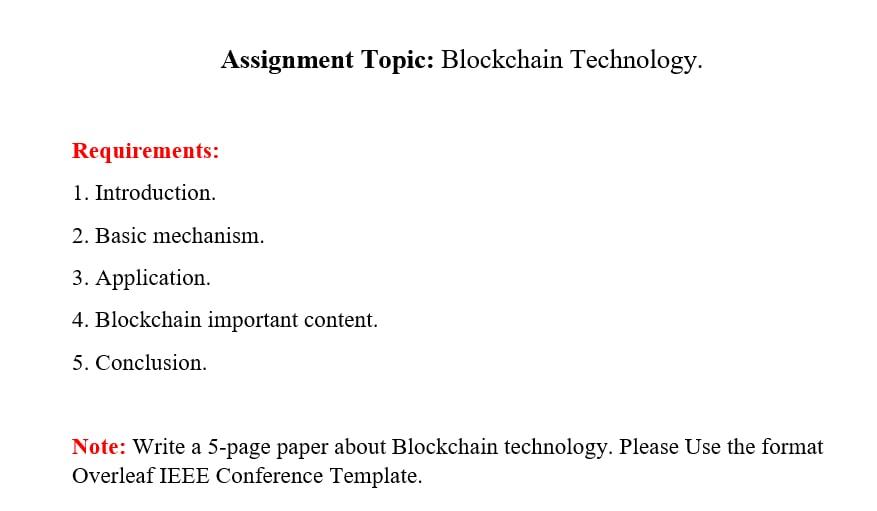
Solved Assignment Topic Blockchain Technology Chegg This lab assignment explores various cryptographic techniques, including caesar and vigenère ciphers, des brute force attacks, password hashing, hmac signatures, blockchain implementation, and the vernam cipher. each section includes problem statements, solution codes, and terminal outputs, demonstrating practical applications of cryptography in python. This document contains a laboratory assignment on block chain technologies from lakshami narain college of technology excellence in bhopal, india. it includes two questions about bitcoin mining and the differences between bitcoin and ethereum blockchains.
Comments are closed.