Software Composition Analysis Sca Securing Open Source

Software Composition Analysis Sca Securing Open Source Sca (software composition analysis) is the process of identifying and managing the open source and third party components used in software development. the goal of sca is to identify potential security vulnerabilities, licensing issues, or outdated components in the software being developed or used. Software composition analysis (sca) is a cybersecurity process that identifies and manages open source components within software applications. by scanning for project dependencies in the code, sca tools detect vulnerabilities, license compliance issues, and outdated libraries.
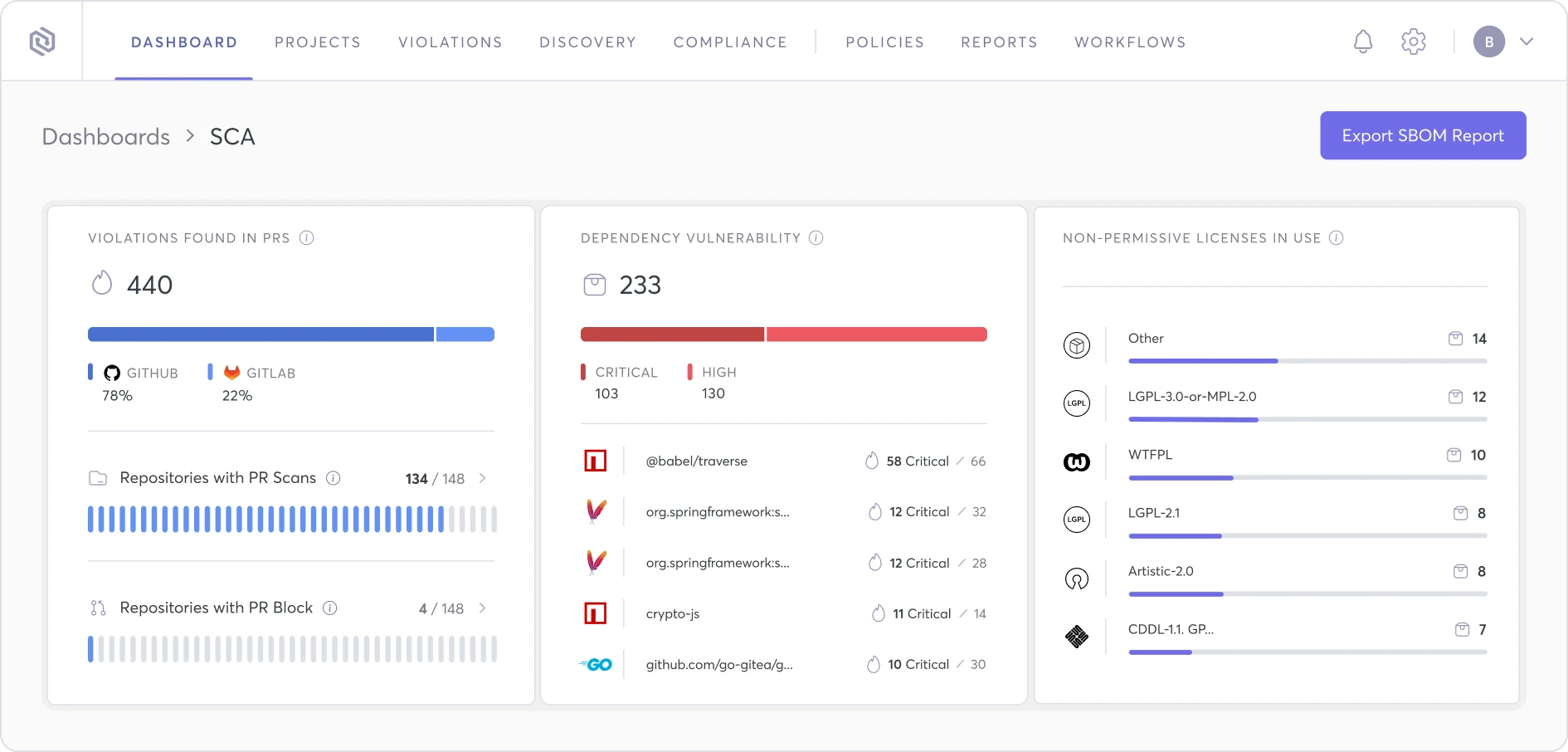
Software Composition Analysis Sca Securing Open Source Software composition analysis (sca) is the process of identifying, managing, and securing open source components and third party libraries within a software project. Comprehensive guide to implementing sca in devsecops pipelines including vulnerability detection, license compliance, and dependency management strategies. Explore the top sca tools of 2025 to find, fix, and prevent vulnerabilities in open source code, ensuring secure, compliant software in modern pipelines. Software composition analysis (sca) is an automated process in software development that identifies, analyzes, & manages open source components within applications to mitigate security risks and ensure compliance.

Dependency Check Open Source Software Composition Analysis Sca Tool Explore the top sca tools of 2025 to find, fix, and prevent vulnerabilities in open source code, ensuring secure, compliant software in modern pipelines. Software composition analysis (sca) is an automated process in software development that identifies, analyzes, & manages open source components within applications to mitigate security risks and ensure compliance. Secure your open source use with automated vulnerability detection, license compliance, and risk prevention. seamlessly integrate into your workflows, gain full visibility of risks, and protect your software supply chain with ease. Learn what software composition analysis (sca) is, how it differs from sast, why open source dependencies are risky, and how to scan for vulnerable packages. What is software composition analysis, and why does it matter for cloudsec, appsec, and secops teams? software composition analysis (sca) identifies the open source components and third party dependencies an application uses and evaluates the associated security, licensing, and compliance risks. Software composition analysis (sca) is the process of analyzing software—most commonly software built from open source components—to ensure that the components are up to date, secure and in license compliance.

04 Software Composition Analysis Sca Secure your open source use with automated vulnerability detection, license compliance, and risk prevention. seamlessly integrate into your workflows, gain full visibility of risks, and protect your software supply chain with ease. Learn what software composition analysis (sca) is, how it differs from sast, why open source dependencies are risky, and how to scan for vulnerable packages. What is software composition analysis, and why does it matter for cloudsec, appsec, and secops teams? software composition analysis (sca) identifies the open source components and third party dependencies an application uses and evaluates the associated security, licensing, and compliance risks. Software composition analysis (sca) is the process of analyzing software—most commonly software built from open source components—to ensure that the components are up to date, secure and in license compliance.
Software Composition Analysis Sca Checklist Itreports Tech What is software composition analysis, and why does it matter for cloudsec, appsec, and secops teams? software composition analysis (sca) identifies the open source components and third party dependencies an application uses and evaluates the associated security, licensing, and compliance risks. Software composition analysis (sca) is the process of analyzing software—most commonly software built from open source components—to ensure that the components are up to date, secure and in license compliance.
Comments are closed.