Side Channel Attacks On Everyday Applications

Side Channel Attacks Explained All You Need To Know Rambus Continuing the trend of using cache side channels to violate users’ privacy, our work further confirms that cache side channel attacks can do worse than just break ing cryptography software. Uncover the hidden world of side channel attacks: learn how hackers exploit system vulnerabilities, real world examples, and cutting edge defense strategies.
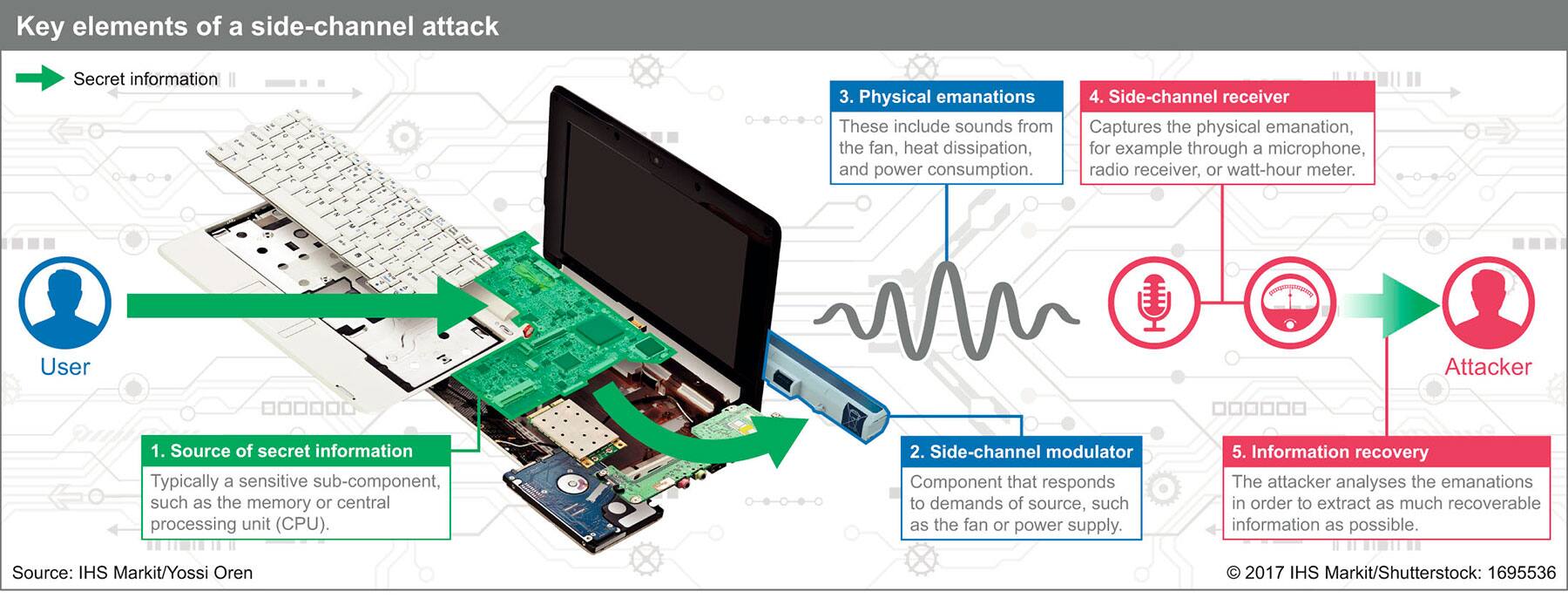
Side Channel Attacks Pose Growing Threat To Security In computer security, a side channel attack is a type of security exploit that uses information inadvertently leaked by a system—such as timing, power consumption, or electromagnetic or acoustic emissions—to gain unauthorized access to sensitive information. In this paper, we provide a comprehensive survey of power side channel attacks and their countermeasures in different application domains. specifically, this survey aims to classify recent power side channel attacks and provide a comprehensive comparison based on application specific considerations. We describe how input distinguishing attacks can be discovered automatically (with human assistance) and we present three concrete attacks. our first attack is against the links command line web browser. What exactly is a side channel attack? to understand side channel attacks, we need to shift our perspective. a mathematical algorithm like aes or rsa exists in theory as clean, precise.

Side Channel Attacks Explained Types Examples Dpa Protection We describe how input distinguishing attacks can be discovered automatically (with human assistance) and we present three concrete attacks. our first attack is against the links command line web browser. What exactly is a side channel attack? to understand side channel attacks, we need to shift our perspective. a mathematical algorithm like aes or rsa exists in theory as clean, precise. Continuing the trend of using cache side channels to violate users’ privacy, our work further confirms that cache side channel attacks can do worse than just breaking cryptography software. Side channel attacks are simply another tool in the attacker’s arsenal. if an attacker can’t find a practical way to break the algorithm itself, then they can collect information from its implementation and see if this gets them any closer to breaking the system. We propose a new method based on attention mechanisms and multi scale convolutional neural networks (amcnnet), which is designed to effectively attack encryption implementations under the countermeasures of masking and clock jitter. the following is a summary of the main contributions of this paper. Such source of information beyond the output speci ed by an abstraction is called a side channel. in this lecture, we will explore the history, examples, and countermeasures of side channel attacks.

Side Channel Attacks Explained Types Examples Dpa Protection Continuing the trend of using cache side channels to violate users’ privacy, our work further confirms that cache side channel attacks can do worse than just breaking cryptography software. Side channel attacks are simply another tool in the attacker’s arsenal. if an attacker can’t find a practical way to break the algorithm itself, then they can collect information from its implementation and see if this gets them any closer to breaking the system. We propose a new method based on attention mechanisms and multi scale convolutional neural networks (amcnnet), which is designed to effectively attack encryption implementations under the countermeasures of masking and clock jitter. the following is a summary of the main contributions of this paper. Such source of information beyond the output speci ed by an abstraction is called a side channel. in this lecture, we will explore the history, examples, and countermeasures of side channel attacks.
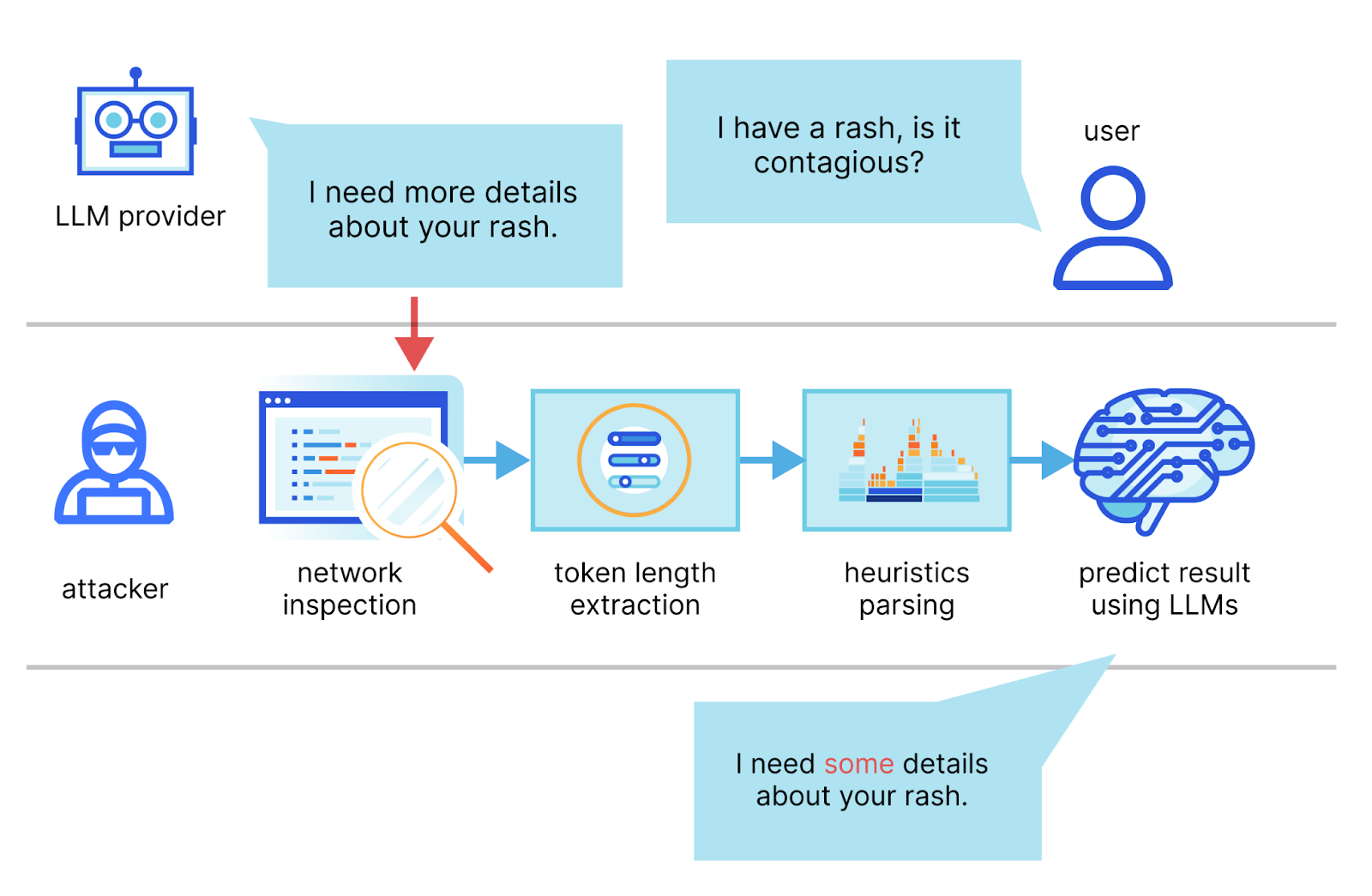
Mitigating A Token Length Side Channel Attack In Our Ai Products We propose a new method based on attention mechanisms and multi scale convolutional neural networks (amcnnet), which is designed to effectively attack encryption implementations under the countermeasures of masking and clock jitter. the following is a summary of the main contributions of this paper. Such source of information beyond the output speci ed by an abstraction is called a side channel. in this lecture, we will explore the history, examples, and countermeasures of side channel attacks.
Comments are closed.