Side Channel Attack
New Collide Power Side Channel Attack Leaks Data From Most Modern Cpus In computer security, a side channel attack is a type of security exploit that uses information inadvertently leaked by a system—such as timing, power consumption, or electromagnetic or acoustic emissions—to gain unauthorized access to sensitive information. A side channel attack is a cybersecurity exploit that aims to gather information from or influence a system's program execution. it does this by measuring or exploiting indirect effects of the system or its hardware rather than directly targeting the program or its code.

Side Channel Attack By Wentz Wu Issap Issep Issmp Cissp Ccsp Csslp A side channel attack is a security exploit that targets the implementation of a computer system rather than theoretical vulnerabilities in the algorithms. these attacks analyze information gained from the physical operation of a system. A side channel attack is defined as a method of stealing information indirectly by exploiting unintended information leakage, such as side channel signals generated during computation. Side channel attacks don't target cryptographic systems, but their implementations instead. find out how they can compromise secure algorithms. Learn what a side channel attack is, how it exploits physical characteristics of a cryptosystem, and what are the potential risks and examples of this security exploit. find out how to protect against side channel attacks with various strategies and techniques.
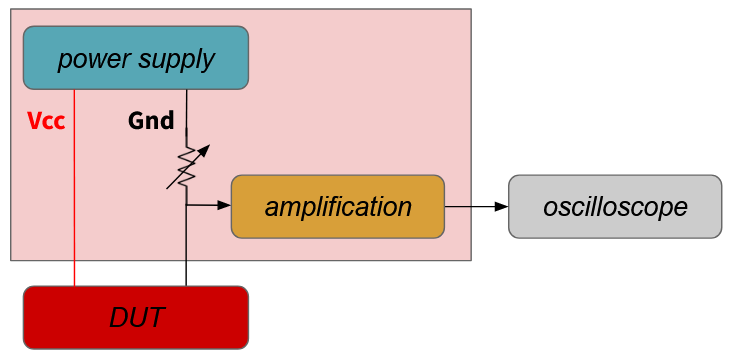
Side Channel Attack Measurement Platform By Stephan Electronics Side channel attacks don't target cryptographic systems, but their implementations instead. find out how they can compromise secure algorithms. Learn what a side channel attack is, how it exploits physical characteristics of a cryptosystem, and what are the potential risks and examples of this security exploit. find out how to protect against side channel attacks with various strategies and techniques. Learn how to exploit and defend against side channel attacks on embedded devices using power and em leakage. this presentation covers the basics of side channel analysis, attack strategies, countermeasures, and examples. Side channel attacks are a current class of attacks that remains very powerful in practice. via measuring side channel data, the attacker has the ability to capture very sensitive data. Discover 7 emerging side channel attacks threatening trusted execution environments (tees) and learn how to secure enterprise generative ai deployments. Learn about the history, examples, and countermeasures of side channel attacks, which exploit information beyond the output speci ed by an abstraction. side channel attacks can use timing, power consumption, network traffic, electromagnetic radiation, sound, or error messages to break isolation and access secrets.

11 Side Channel Attack Download Scientific Diagram Learn how to exploit and defend against side channel attacks on embedded devices using power and em leakage. this presentation covers the basics of side channel analysis, attack strategies, countermeasures, and examples. Side channel attacks are a current class of attacks that remains very powerful in practice. via measuring side channel data, the attacker has the ability to capture very sensitive data. Discover 7 emerging side channel attacks threatening trusted execution environments (tees) and learn how to secure enterprise generative ai deployments. Learn about the history, examples, and countermeasures of side channel attacks, which exploit information beyond the output speci ed by an abstraction. side channel attacks can use timing, power consumption, network traffic, electromagnetic radiation, sound, or error messages to break isolation and access secrets.
Mitigating A Token Length Side Channel Attack In Our Ai Products Discover 7 emerging side channel attacks threatening trusted execution environments (tees) and learn how to secure enterprise generative ai deployments. Learn about the history, examples, and countermeasures of side channel attacks, which exploit information beyond the output speci ed by an abstraction. side channel attacks can use timing, power consumption, network traffic, electromagnetic radiation, sound, or error messages to break isolation and access secrets.
Comments are closed.