Setting Up Lab For Malware Analysis Pdf

Malware Analysis Lab Setup Pdf Before starting an analysis, you need to make a choice between these two variants. The document outlines the steps for setting up a malware analysis lab using windows 10 and remnux in virtualbox. it includes instructions for installing flarevm, configuring network settings, and ensuring both virtual machines can communicate with each other while isolated from external networks.

27 2 15 Lab Investigating A Malware Exploit Pdf Security In this chapter, you learned how to set up a malware analysis lab, where one can run all kinds of malware without fear of infecting the host device and other hosts on the network. This step by step will provides a detailed guide for setting up a malware analysis lab. it covers the installation and configuration of various tools and virtual environments essential for analyzing malware in a controlled and isolated environment. In conclusion, the study confirms the efficiency of the lab environment in performing malware analysis. the lab environment not only supports advanced malware analysis tasks, but also acts as a replicable model for education in the sphere of cybersecurity. If you’re planning to dive into malware analysis, this pdf guide is an excellent starting point. “step by step malware analysis lab setup” by ammar hakim haris walks you through the entire process of building a safe and isolated analysis lab — even if it’s your first time setting one up.
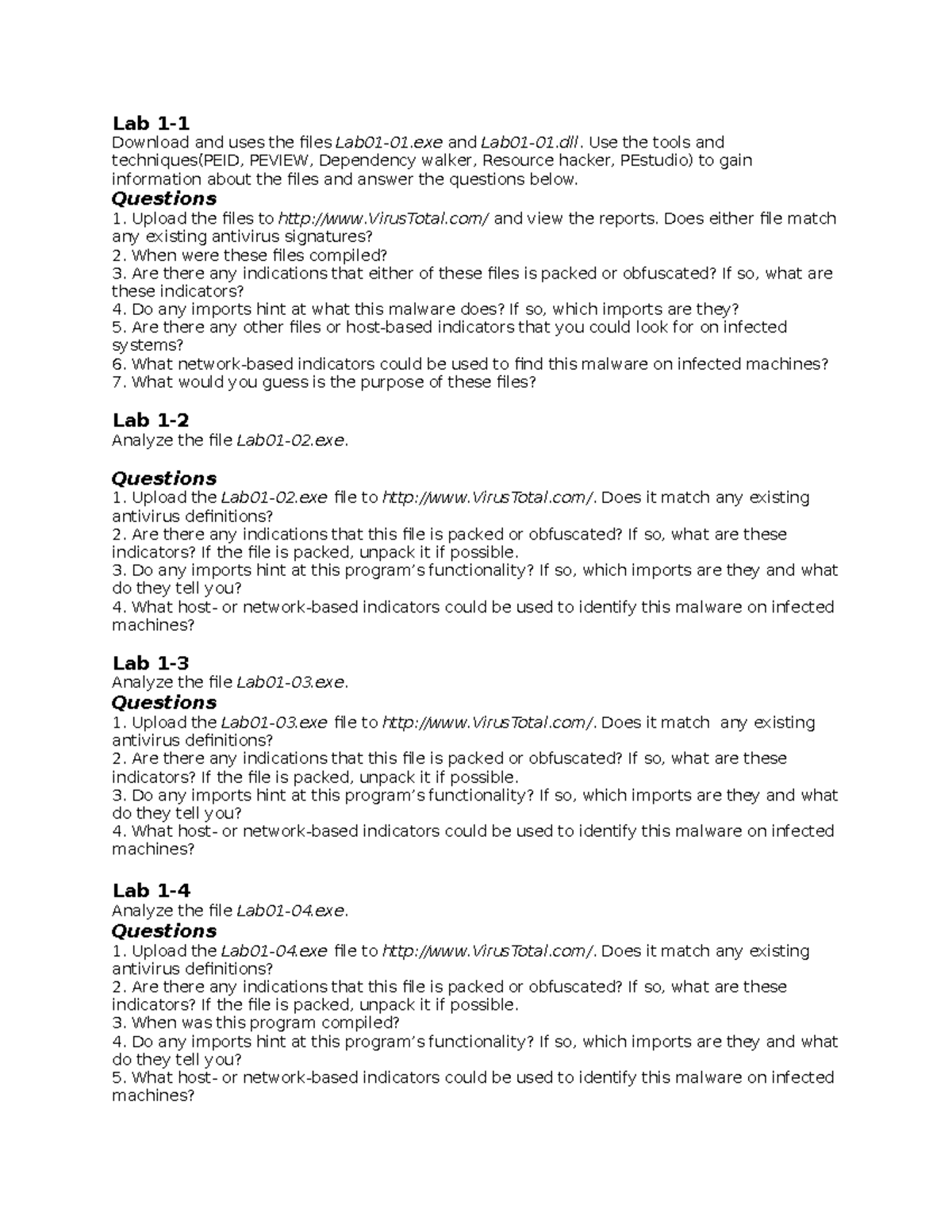
Lab 2 Malware Analysis Lab Lab 1 Download And Uses The Files Lab01 In conclusion, the study confirms the efficiency of the lab environment in performing malware analysis. the lab environment not only supports advanced malware analysis tasks, but also acts as a replicable model for education in the sphere of cybersecurity. If you’re planning to dive into malware analysis, this pdf guide is an excellent starting point. “step by step malware analysis lab setup” by ammar hakim haris walks you through the entire process of building a safe and isolated analysis lab — even if it’s your first time setting one up. Re analysis, and setting up a manual malw. lysis lab. malware is malicious software that ca. ses harm. the average malware wi. l have 125 lines of code. generally, malware consi. ts of 3 components: a concealer, a. replicator, and a bomb. m. lware is classified based on its nature and functionality. into two categor. “a great introduction to malware analysis. all chapters contain detailed technical explanations and hands on lab exercises to get you immediate exposure to real malware.” —sebastian porst, googlesoftwareengineer. “brings reverse engineering to readers of all skill levels. Then click create to duplicate another adapter for this setting. so, both vm will only communicate with each other to prevent your host get infected with malware once detonated. Step by step malware analysis lab set up name the snapshot accordingly. this will allow you to return to this base phase if there is error prompted during next configuration.
Pdf Malware Analysis Re analysis, and setting up a manual malw. lysis lab. malware is malicious software that ca. ses harm. the average malware wi. l have 125 lines of code. generally, malware consi. ts of 3 components: a concealer, a. replicator, and a bomb. m. lware is classified based on its nature and functionality. into two categor. “a great introduction to malware analysis. all chapters contain detailed technical explanations and hands on lab exercises to get you immediate exposure to real malware.” —sebastian porst, googlesoftwareengineer. “brings reverse engineering to readers of all skill levels. Then click create to duplicate another adapter for this setting. so, both vm will only communicate with each other to prevent your host get infected with malware once detonated. Step by step malware analysis lab set up name the snapshot accordingly. this will allow you to return to this base phase if there is error prompted during next configuration.
Comments are closed.