Lab Setup For Analyzing Malicious Files And Executables

Malware Analysis Lab Setup Pdf The first and the most important thing to do before setting up a lab is to figure out the needs and the requirements for setting up a lab. it is very important to have some dedicated systems with tools to control, analyze, and safeguard your environment. This project aims to provide a detailed and structured setup guide for building a safe and functional malware analysis lab. by using vmware, kali linux, and windows, you can perform both static and dynamic malware analysis, all within a secure environment.

Lab Setup For Analyzing Malicious Files And Executables Mossé Cyber In this video, we will discuss how you can perform malware analysis at home in your very own lab. “step by step malware analysis lab setup” by ammar hakim haris walks you through the entire process of building a safe and isolated analysis lab — even if it’s your first time setting one up. By following this step by step guide, you have successfully built a malware analysis lab using vmware workstation, enabling both static and dynamic analysis of malware samples. This gold standard guide provides everything you need to build a professional grade, fully isolated malware analysis lab on your own computer using virtualbox. devel….
Github Acibojbp Malware Analysis Lab Setup By following this step by step guide, you have successfully built a malware analysis lab using vmware workstation, enabling both static and dynamic analysis of malware samples. This gold standard guide provides everything you need to build a professional grade, fully isolated malware analysis lab on your own computer using virtualbox. devel…. Malware labs must be separated from other networks to prevent infections from spilling outside of the lab. at a minimum, the analysis labs themselves should only be accessible one way via a specific interface. Copy malicious files to the virtual machine, run them and observe the behavior with the help of malware analysis tools once the analysis is completed, revert the virtual machine to a clean state to clear the machine of malware. Now that we understand the basics of malware analysis, let’s begin setting up our lab. before we jump into the installation steps, i’ll first walk you through flare vm and remnux vm — what they are, why they’re used, and how they help in malware analysis. Building the right malware analysis lab is the first step for every researcher. use this guide and download our free custom tools to aid your research.

27 2 15 Lab Investigating A Malware Exploit Pdf Security Malware labs must be separated from other networks to prevent infections from spilling outside of the lab. at a minimum, the analysis labs themselves should only be accessible one way via a specific interface. Copy malicious files to the virtual machine, run them and observe the behavior with the help of malware analysis tools once the analysis is completed, revert the virtual machine to a clean state to clear the machine of malware. Now that we understand the basics of malware analysis, let’s begin setting up our lab. before we jump into the installation steps, i’ll first walk you through flare vm and remnux vm — what they are, why they’re used, and how they help in malware analysis. Building the right malware analysis lab is the first step for every researcher. use this guide and download our free custom tools to aid your research.
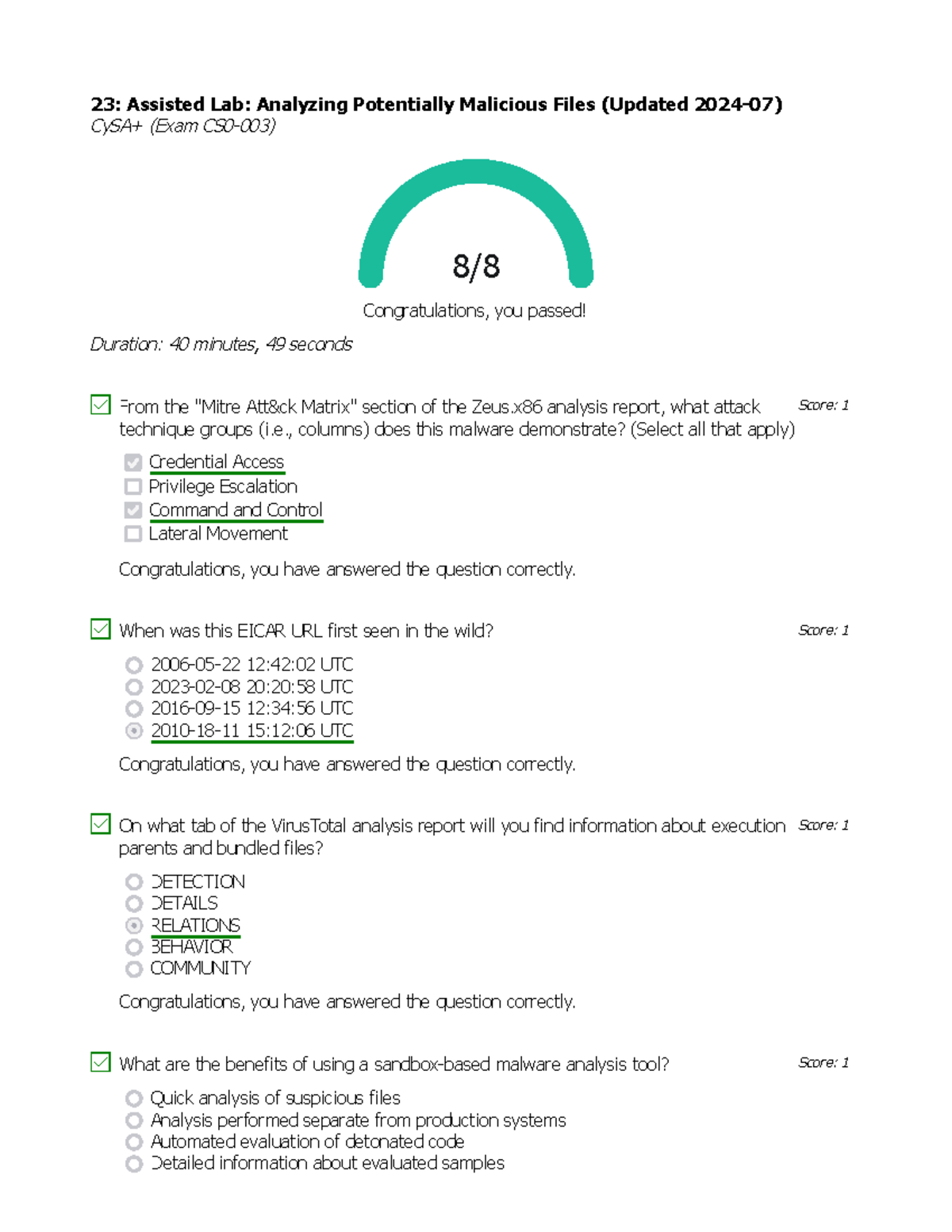
23 Analyzing Potentially Malicious Files Columns Does This Malware Now that we understand the basics of malware analysis, let’s begin setting up our lab. before we jump into the installation steps, i’ll first walk you through flare vm and remnux vm — what they are, why they’re used, and how they help in malware analysis. Building the right malware analysis lab is the first step for every researcher. use this guide and download our free custom tools to aid your research.
Comments are closed.