Session On Deep Learning Based Side Channel Attacks
Scadl A New Side Channel Attack Tool Using Deep Learning Ledger This tutorial is designed to be accessible to researchers, students, and practitioners seeking to learn practical dlsca techniques and improve the security of cryptographic systems. Scaaml intro : a hacker guide to deep learning based side channel attacks. code, dataset and models used in our step by step tutorial on how to use deep learning to perform aes side channel attacks in practice.

Side Channel Attacks Explained Types Examples Dpa Protection Successfully classified side channel attack patterns with over 90% accuracy using deep learning techniques. despite its relatively simple structure, mlp achieved the best classification performance (99.4%). mlp was also confirmed to be the most efficient in terms of training time and memory usage. Explore cutting edge research on deep learning based side channel attacks in this comprehensive session from ches 2022. delve into the latest advancements and techniques in the field of cryptographic hardware and embedded systems security. Encryption algorithms and encryption devices both play a key role in ensuring the safety of data that has been encrypted. various types of attacks, such as ener. We introduce how deep learning can be applied to side channel attacks and preprocess side channel attack datasets for denoising, making it easier for attackers to infer sensitive information.

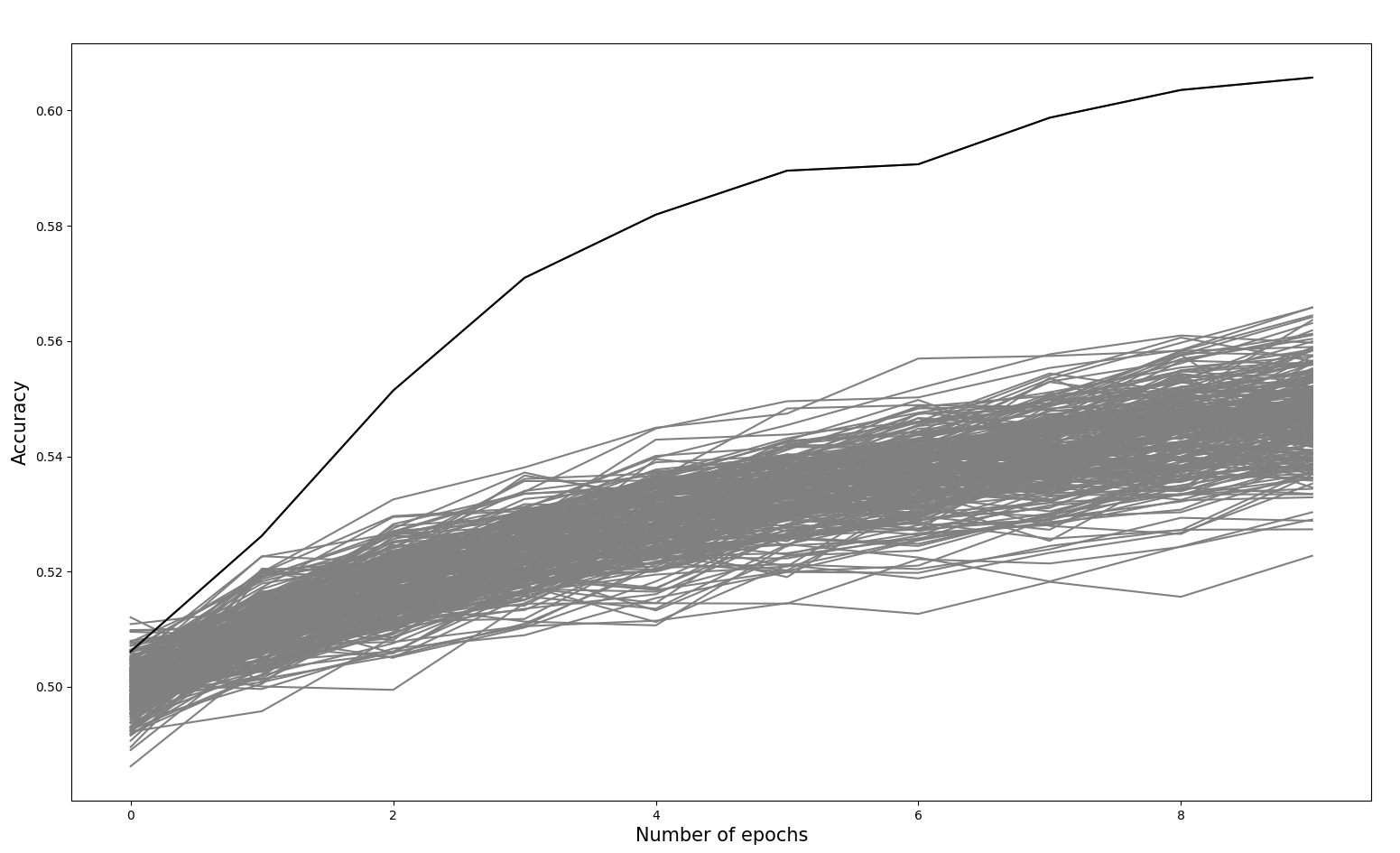
Black Hat Talk A Hacker S Guide To Reducing Side Channel Attack Encryption algorithms and encryption devices both play a key role in ensuring the safety of data that has been encrypted. various types of attacks, such as ener. We introduce how deep learning can be applied to side channel attacks and preprocess side channel attack datasets for denoising, making it easier for attackers to infer sensitive information. In this study, we conduct a detailed examination of the extent to which environmental noise and interference can affect the attack efficiency of rf wscas. we first proposed a 20 input cnn architecture that achieved similar attack results to the sota model. Following that, it introduces the concepts of deep learning and explains the role that deep learning plays in enabling side channel attacks. in addition, it covers various leakage models and commonly utilized evaluation metrics for scas. By exploiting advances in deep learning (dl), several dl based profiled side channel analyses (scas) have been performed. In this study, we propose and investigate the use of deep learning (dl) techniques to enhance the effectiveness of non profiled scas through an optimized deep learning power analysis (dlpa) algorithm.
Mitigating A Token Length Side Channel Attack In Our Ai Products In this study, we conduct a detailed examination of the extent to which environmental noise and interference can affect the attack efficiency of rf wscas. we first proposed a 20 input cnn architecture that achieved similar attack results to the sota model. Following that, it introduces the concepts of deep learning and explains the role that deep learning plays in enabling side channel attacks. in addition, it covers various leakage models and commonly utilized evaluation metrics for scas. By exploiting advances in deep learning (dl), several dl based profiled side channel analyses (scas) have been performed. In this study, we propose and investigate the use of deep learning (dl) techniques to enhance the effectiveness of non profiled scas through an optimized deep learning power analysis (dlpa) algorithm.
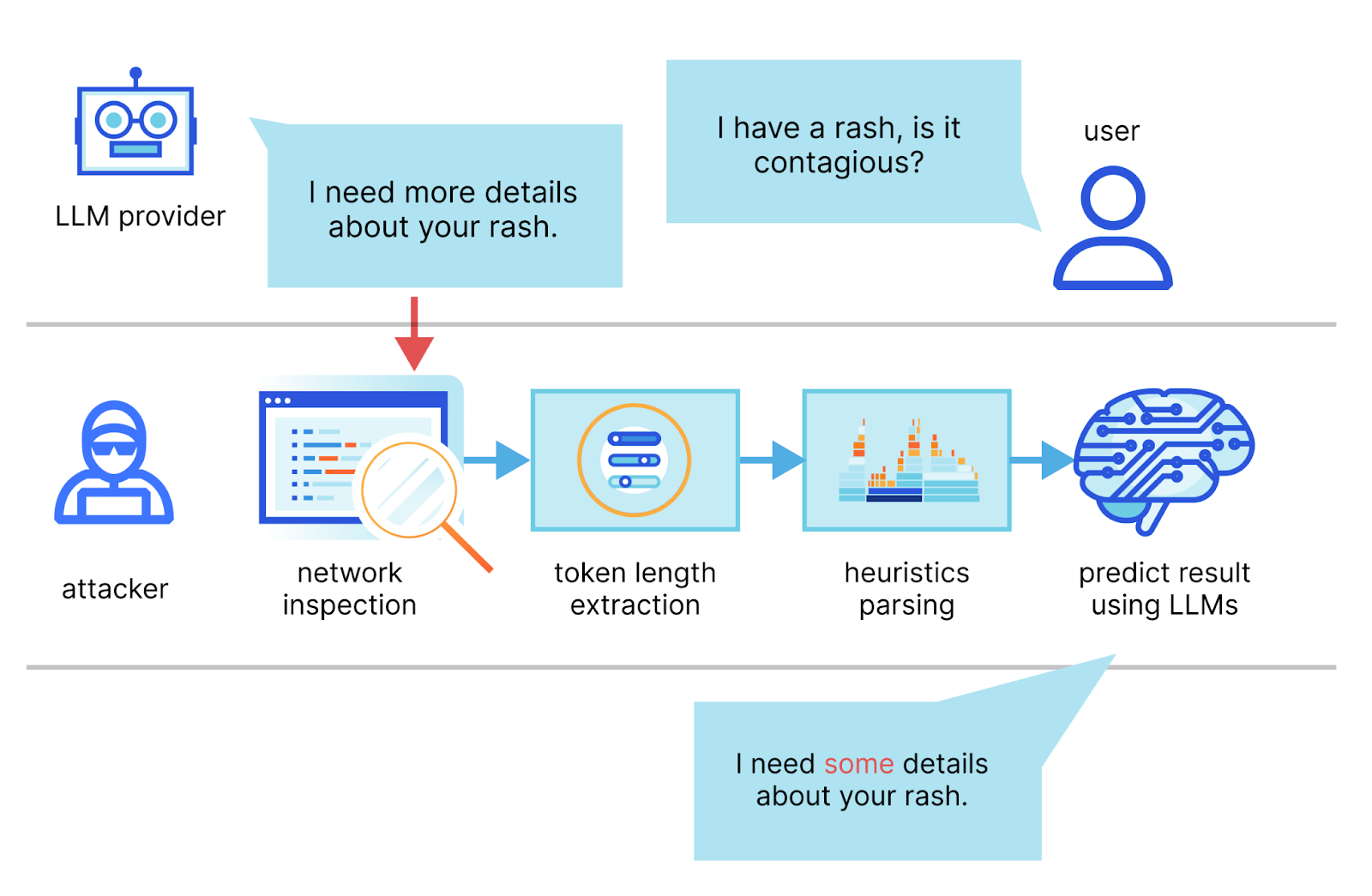
Mitigating A Token Length Side Channel Attack In Our Ai Products By exploiting advances in deep learning (dl), several dl based profiled side channel analyses (scas) have been performed. In this study, we propose and investigate the use of deep learning (dl) techniques to enhance the effectiveness of non profiled scas through an optimized deep learning power analysis (dlpa) algorithm.
Comments are closed.