Session Management Flino Dev

Session Management Flino Dev Learn about session management and the different attacks that can be performed against insecure implementations. The open source modsecurity waf, plus the owasp core rule set, provide capabilities to detect and apply security cookie attributes, countermeasures against session fixation attacks, and session tracking features to enforce sticky sessions.

Protocols And Servers 2 Flino Dev Therefore, in order to introduce the concept of a session, it is required to implement session management capabilities that link both the authentication and access control (or authorization) modules commonly available in web applications:. In these scenarios, or to complement the web application defenses, and with the goal of keeping the web application as secure as possible, it is recommended to use external protections such as web application firewalls (wafs) that can mitigate the session management threats already described. In this article, we’ll explore how web developers can effectively create and manage user sessions on the client and server side, as well as in typical monolithic and microservices environments, without compromising user experience, security, performance, and scalability of the system. By understanding the core mechanisms, storage options, and security best practices outlined in this guide, you'll be well equipped to implement effective session management in your node.js projects, or indeed in any other web development stack.

Francisco Lino Software Developer Flino Dev In this article, we’ll explore how web developers can effectively create and manage user sessions on the client and server side, as well as in typical monolithic and microservices environments, without compromising user experience, security, performance, and scalability of the system. By understanding the core mechanisms, storage options, and security best practices outlined in this guide, you'll be well equipped to implement effective session management in your node.js projects, or indeed in any other web development stack. In this article, we will explore some common best practices for session management and see how you can implement each using node or python. a user session refers to the period of time during which a user interacts with your app. User session management is an important security function of web applications. it keeps user identities and sensitive data secure during an interaction while orchestrating a seamless navigation experience as the user submits requests and visits different web pages or applications. The overall objective while attacking session management is to find a way to forge new session tokens to gain unauthorized access to an account or data. following these steps will allow many impactful flaws to be revealed that are often overlooked. 3 session management ¶ browse by section: 3.1 fundamental session management requirements 3.2 session binding requirements 3.3 session logout and timeout requirements 3.4 cookie based session management 3.5 token based session management 3.6 re authentication from a federation or assertion 3.7 defenses against session management exploits.
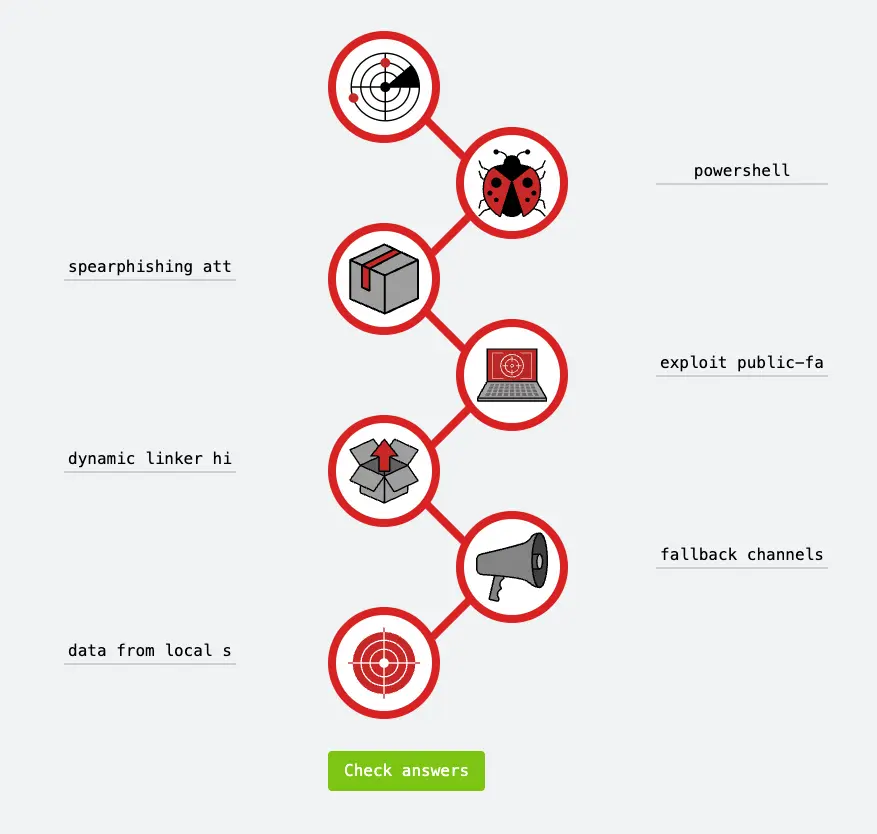
Cyber Kill Chain Room Flino Dev In this article, we will explore some common best practices for session management and see how you can implement each using node or python. a user session refers to the period of time during which a user interacts with your app. User session management is an important security function of web applications. it keeps user identities and sensitive data secure during an interaction while orchestrating a seamless navigation experience as the user submits requests and visits different web pages or applications. The overall objective while attacking session management is to find a way to forge new session tokens to gain unauthorized access to an account or data. following these steps will allow many impactful flaws to be revealed that are often overlooked. 3 session management ¶ browse by section: 3.1 fundamental session management requirements 3.2 session binding requirements 3.3 session logout and timeout requirements 3.4 cookie based session management 3.5 token based session management 3.6 re authentication from a federation or assertion 3.7 defenses against session management exploits.

Unified Kill Chain Room Flino Dev The overall objective while attacking session management is to find a way to forge new session tokens to gain unauthorized access to an account or data. following these steps will allow many impactful flaws to be revealed that are often overlooked. 3 session management ¶ browse by section: 3.1 fundamental session management requirements 3.2 session binding requirements 3.3 session logout and timeout requirements 3.4 cookie based session management 3.5 token based session management 3.6 re authentication from a federation or assertion 3.7 defenses against session management exploits.

Session Management Fundamentals
Comments are closed.