Security Testing Overview Documentation

Security Testing Documentation Pdf Software Testing Software This guide covers the complete spectrum of security test documentation, from owasp based testing checklists to penetration test reports, vulnerability assessments, and remediation tracking. Get a comprehensive overview of security testing in pynt. understand how pynt's advanced tools help identify vulnerabilities, assess risks, and secure your apis effectively.

4 Security Testing Pdf Security Computer Security The web security testing guide (wstg) project produces the premier cybersecurity testing resource for web application developers and security professionals. The guide provides practical recommendations for designing, implementing, and maintaining technical information security test and examination processes and procedures. As with the introduction of any new concepts, there can be flaws and vulnerabilities that necessitate testing. otherwise, poorly secured apis may provide an unrestricted direct path to sensitive data. this chapter attempts to guide the security researcher in the concepts necessary for testing apis. In summary, security testing should be integrated throughout the software development lifecycle, from development through to system integration and user acceptance testing.

Introduction To Security Testing Pdf As with the introduction of any new concepts, there can be flaws and vulnerabilities that necessitate testing. otherwise, poorly secured apis may provide an unrestricted direct path to sensitive data. this chapter attempts to guide the security researcher in the concepts necessary for testing apis. In summary, security testing should be integrated throughout the software development lifecycle, from development through to system integration and user acceptance testing. The rest of this guide is organized as follows: this introduction covers the pre requisites of testing web applications and the scope of testing. it also covers the principles of successful testing and testing techniques, best practices for reporting, and business cases for security testing. With cyberattacks becoming more easily happens, it’s important to perform thorough security tests throughout the development process. this helps find vulnerabilities early on, preventing them from being exploited later. Security testing is performed to reveal security flaws in the system in order to protect data and maintain functionality.this tutorial explains the core concepts of security testing and related topics with simple and useful examples. The wog security testing guidelines establishes clear guidelines for all parties involved in security testing engagements with the intent of ensuring proper end to end delivery of high quality security testing of wog systems.

Security Testing Overview Documentation The rest of this guide is organized as follows: this introduction covers the pre requisites of testing web applications and the scope of testing. it also covers the principles of successful testing and testing techniques, best practices for reporting, and business cases for security testing. With cyberattacks becoming more easily happens, it’s important to perform thorough security tests throughout the development process. this helps find vulnerabilities early on, preventing them from being exploited later. Security testing is performed to reveal security flaws in the system in order to protect data and maintain functionality.this tutorial explains the core concepts of security testing and related topics with simple and useful examples. The wog security testing guidelines establishes clear guidelines for all parties involved in security testing engagements with the intent of ensuring proper end to end delivery of high quality security testing of wog systems.
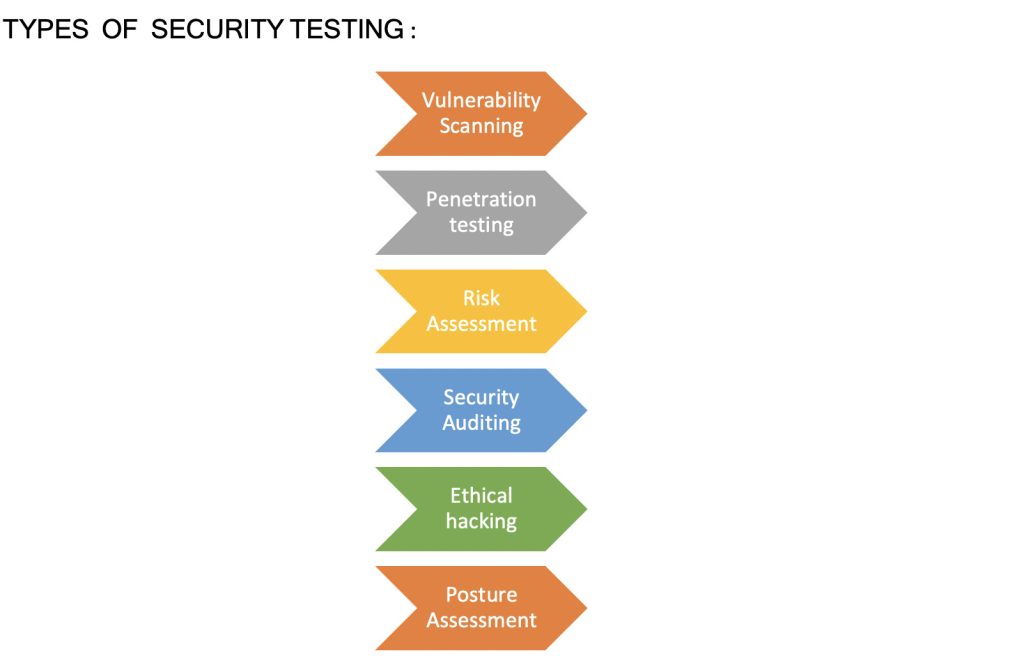
Security Testing Audvik Labs Security testing is performed to reveal security flaws in the system in order to protect data and maintain functionality.this tutorial explains the core concepts of security testing and related topics with simple and useful examples. The wog security testing guidelines establishes clear guidelines for all parties involved in security testing engagements with the intent of ensuring proper end to end delivery of high quality security testing of wog systems.

Automating Security Testing Strategies For Comprehensive Coverage
Comments are closed.