Security Reference Architecture Process
Security Reference Architecture Pdf Security reference architecture is a practical, codified blueprint that converts security intent into repeatable design, telemetry, and operational practices. it bridges architects, sres, and security teams to reduce risk while preserving developer velocity. These reference architectures accelerate planning and execution of security modernization using open standards, microsoft’s cybersecurity capabilities and technologies, and third party security technology.
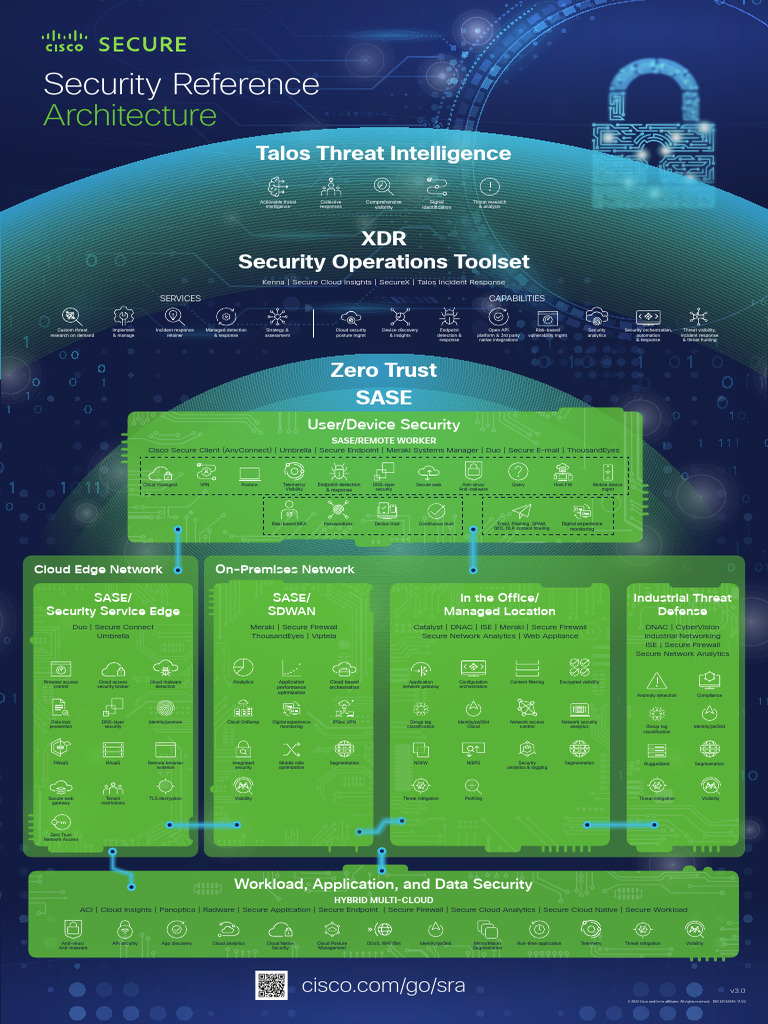
Security Reference Architecture Poster Vs 3 0 Pdf Guidance on how you can build your own security architecture in six iterative phases, based on the reference provided by aws sra. The reference architecture maps to domains that align closely with industry security frameworks such as nist, cisa, and disa. the five main components of the reference architecture are listed below. This report provides a security reference architecture and guidance for secure digital enterprises. it contains business and technical views that security teams can customize to fit their specific needs. A reference architecture doesn’t just tell you what to do—it shows you how to do it, often through visual diagrams, workflows, and detailed mappings of policies to specific systems or processes.
A Security Reference Architecture For Blockchains Pdf This report provides a security reference architecture and guidance for secure digital enterprises. it contains business and technical views that security teams can customize to fit their specific needs. A reference architecture doesn’t just tell you what to do—it shows you how to do it, often through visual diagrams, workflows, and detailed mappings of policies to specific systems or processes. The cybersecurity reference architecture (csra) version 5 will deliver on this imperative for the dod by aligning to the dms and integrating zt principles to define data protection for cloud,. These views map security related technologies and processes into those required for security management and control systems, security monitoring, incident response, vulnerability and configuration management, network security, identity and access management, and information protection. Overview: describe the security policies and considerations required of the architecture that external users will need to interface and get access to the data information. Learn how to create effective cybersecurity reference architectures, including definitions, benefits, implementation strategies, governance, and common challenges.
The Security Reference Architecture For Blockchains Toward A The cybersecurity reference architecture (csra) version 5 will deliver on this imperative for the dod by aligning to the dms and integrating zt principles to define data protection for cloud,. These views map security related technologies and processes into those required for security management and control systems, security monitoring, incident response, vulnerability and configuration management, network security, identity and access management, and information protection. Overview: describe the security policies and considerations required of the architecture that external users will need to interface and get access to the data information. Learn how to create effective cybersecurity reference architectures, including definitions, benefits, implementation strategies, governance, and common challenges.
Security Reference Architecture Process Overview: describe the security policies and considerations required of the architecture that external users will need to interface and get access to the data information. Learn how to create effective cybersecurity reference architectures, including definitions, benefits, implementation strategies, governance, and common challenges.
Comments are closed.