Security Models Security Reference Architecture
Security Reference Architecture Pdf The key in creating a good model to solve a specific information security problem is to model the problem, not the complete system with all elements. this because modelling the world completely is ineffective, time consuming and it does not give a direct answer to solve a problem situation. You learn about the microsoft cybersecurity reference architecture (mcra) and microsoft cloud security benchmark (mcsb) and how you can use them to design more secure solutions.
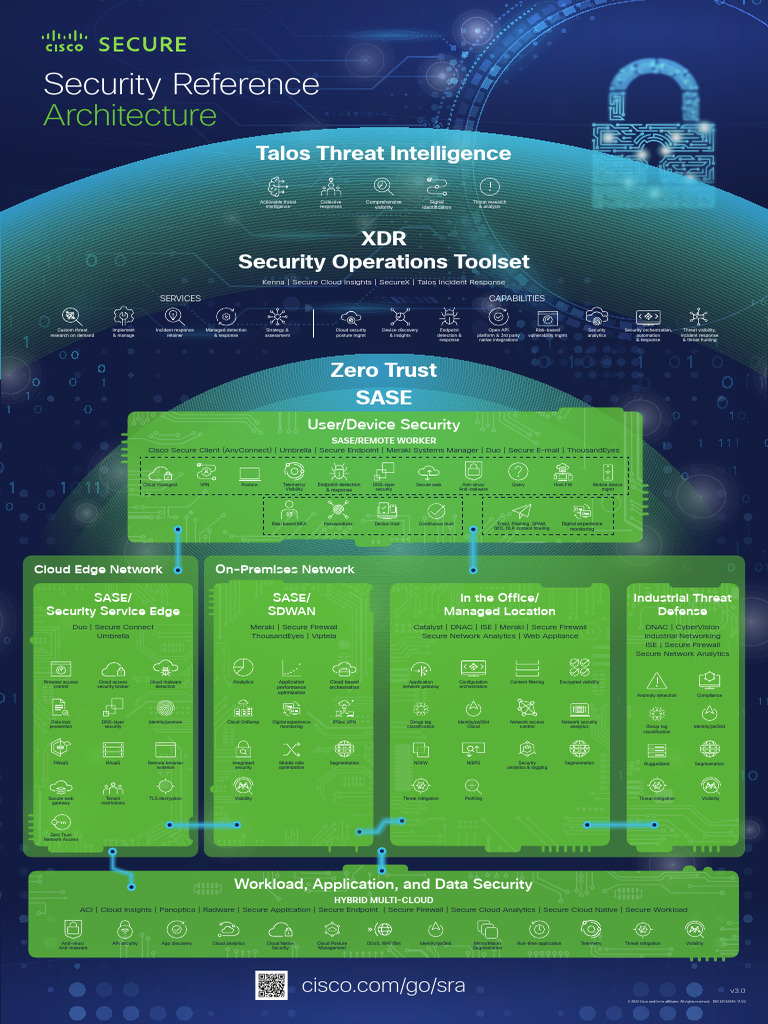
Security Reference Architecture Poster Vs 3 0 Pdf A security reference architecture is a codified blueprint that prescribes how security controls are placed, configured, and measured across cloud native platforms to protect assets while enabling reliable operations. The cisco security reference architecture (sra) provides an overview of the cisco security portfolio, commonly deployed use cases, and the recommended capabilities within an integrated architecture. This architectural diagram brings together all the aws security related services. it is built around a simple, three tier web architecture that can fit on a single page. The security reference model (srm) is a framework used to define and organize the security requirements for an information system. it is part of the overall enterprise architecture and is used to guide the development and implementation of security controls.
A Security Reference Architecture For Blockchains Pdf This architectural diagram brings together all the aws security related services. it is built around a simple, three tier web architecture that can fit on a single page. The security reference model (srm) is a framework used to define and organize the security requirements for an information system. it is part of the overall enterprise architecture and is used to guide the development and implementation of security controls. The security reference architecture models both security related processes and security technologies across digital enterprises’ multi cloud and edge system it environments. A well designed reference architecture acts as a bridge between the high level intent of a policy and its practical implementation. it is not just a document–it is a visual map, a shared language, and a guiding framework for turning policy into action. When designing security architecture, organizations leverage security reference models to create systems that effectively protect data. these models outline the necessary components required to secure an environment, including access controls, encryption methods, and monitoring tools. Two fundamental concepts in computer and information security are the security model, which outlines how security is to be implemented—in other words, providing a “blueprint”—and the architecture of a computer system, which fulfills this blueprint.
The Security Reference Architecture For Blockchains Toward A The security reference architecture models both security related processes and security technologies across digital enterprises’ multi cloud and edge system it environments. A well designed reference architecture acts as a bridge between the high level intent of a policy and its practical implementation. it is not just a document–it is a visual map, a shared language, and a guiding framework for turning policy into action. When designing security architecture, organizations leverage security reference models to create systems that effectively protect data. these models outline the necessary components required to secure an environment, including access controls, encryption methods, and monitoring tools. Two fundamental concepts in computer and information security are the security model, which outlines how security is to be implemented—in other words, providing a “blueprint”—and the architecture of a computer system, which fulfills this blueprint.
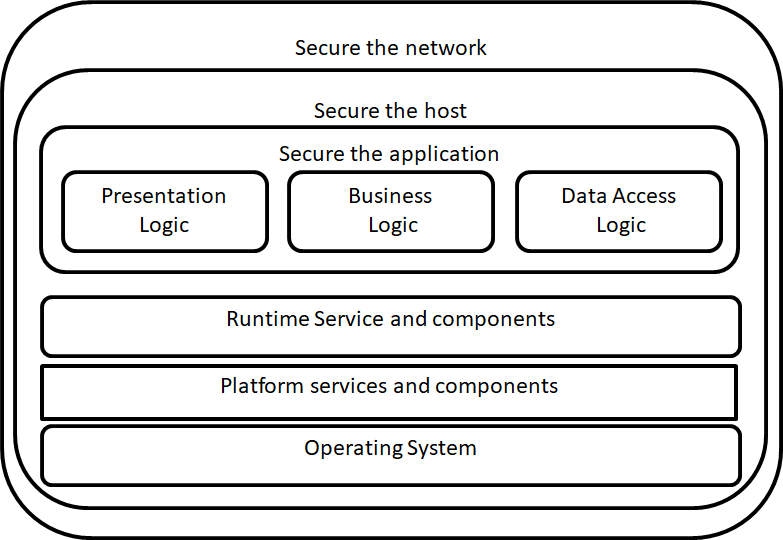
Security Models Security Reference Architecture When designing security architecture, organizations leverage security reference models to create systems that effectively protect data. these models outline the necessary components required to secure an environment, including access controls, encryption methods, and monitoring tools. Two fundamental concepts in computer and information security are the security model, which outlines how security is to be implemented—in other words, providing a “blueprint”—and the architecture of a computer system, which fulfills this blueprint.
Comments are closed.