Security Groups And Network Access Control Lists Acl

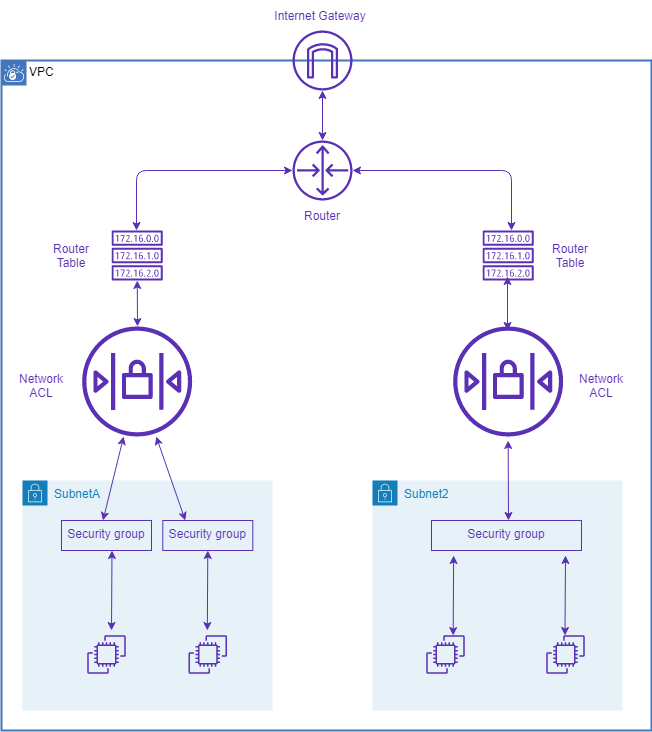
Acl Access Control Lists R3 Int F0 0 R3 Ip Access Group 10 Out Pdf In aws, securing your network involves two primary layers of defense: security groups (sgs) and network access control lists (nacls). while they both act as firewalls, they operate at different layers of the vpc and have fundamentally different behaviors. You can use the default network acl for your vpc, or you can create a custom network acl for your vpc with rules that are similar to the rules for your security groups in order to add an additional layer of security to your vpc.
Enhancing Network Security A Guide To Access Control Lists Acl Learn what a network access control list (acl) is, its benefits, and the different types. this enables administrators to ensure that, unless the proper credentials are presented by the device, it cannot gain access. This document describes various types of ip access control lists (acls) and how they can filter network traffic. Access control lists control user permissions on a network. learn how they work and the different types of acl. Nacls and security groups can be applied in layers together, meaning that we could have nacl rules and security group rules, and they will all have to be evaluated before a request can make it through.

Network Access Control Lists Nacls And Security Groups Sgs Sy0 Access control lists control user permissions on a network. learn how they work and the different types of acl. Nacls and security groups can be applied in layers together, meaning that we could have nacl rules and security group rules, and they will all have to be evaluated before a request can make it through. Awesome cloud — security groups and network acls tl;dr: security group is the firewall of ec2 instances. network acl is the firewall of the vpc subnets. Access control lists (acls) are a way to manage permissions in a structured manner for systems, files, resources, and applications. access to network resources and actions associated with that access is specified by acl. At the heart of many robust security architectures lies a fundamental, yet powerful tool: the access control list (acl). whether you're a network administrator or an it enthusiast, understanding acls is crucial for implementing effective security policies. Now let's zoom in and see how access control lists (acls) work. let's examine the simplest and most straightforward scenario: using access control lists to filter traffic.

Access Control List Acl Pdf Awesome cloud — security groups and network acls tl;dr: security group is the firewall of ec2 instances. network acl is the firewall of the vpc subnets. Access control lists (acls) are a way to manage permissions in a structured manner for systems, files, resources, and applications. access to network resources and actions associated with that access is specified by acl. At the heart of many robust security architectures lies a fundamental, yet powerful tool: the access control list (acl). whether you're a network administrator or an it enthusiast, understanding acls is crucial for implementing effective security policies. Now let's zoom in and see how access control lists (acls) work. let's examine the simplest and most straightforward scenario: using access control lists to filter traffic.

Acl Your Firewall S Bouncer For Network Access At the heart of many robust security architectures lies a fundamental, yet powerful tool: the access control list (acl). whether you're a network administrator or an it enthusiast, understanding acls is crucial for implementing effective security policies. Now let's zoom in and see how access control lists (acls) work. let's examine the simplest and most straightforward scenario: using access control lists to filter traffic.
Security Groups Vs Network Access Control Lists Learn With Aniket
Comments are closed.