Security Audits Step
Security Audits Step It security audit guide: types, methods, security standards, frequency, and tips. we also review the best automated it security audit tools. This guide covers everything you need to understand about security audits: what they are, how they work, what you actually receive when one is complete, and how to prepare so the process delivers maximum value. key takeaways.

Cloud Security Audits A Step By Step Guide Checklist Uncover the fundamentals of security audit checklists, from their importance and common gaps to best practices and key steps for success. understand audit types and examples and see how you can improve your organization's auditing outcomes. A well executed security audit helps organizations prevent breaches, comply with regulations, and enhance overall security posture. below is a step by step guide on conducting a comprehensive security audit. This article will provide details on what exactly security audits are, the various types under them, steps involved, and a security audit checklist. Run smarter security audits with evidence ready controls, clean scoping, faster fieldwork, and remediation that actually sticks.
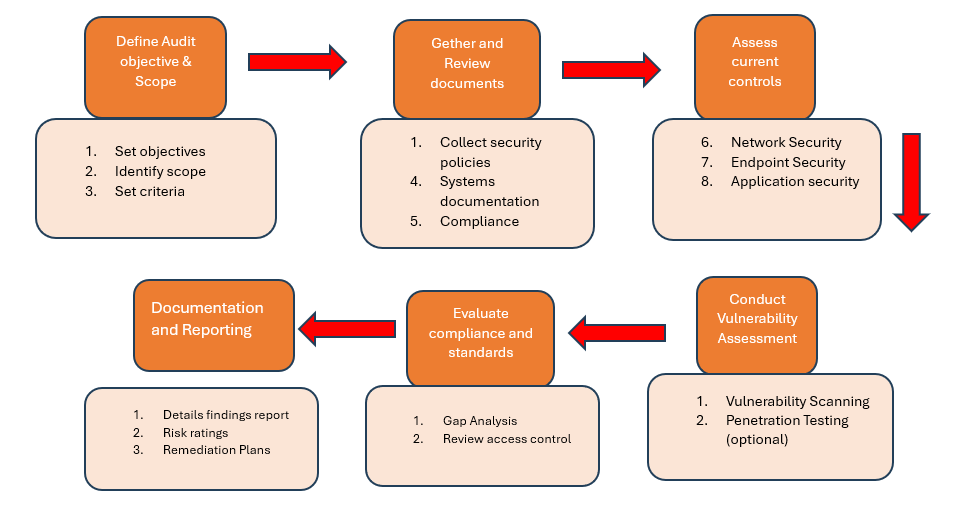
Security Audits Assessments This article will provide details on what exactly security audits are, the various types under them, steps involved, and a security audit checklist. Run smarter security audits with evidence ready controls, clean scoping, faster fieldwork, and remediation that actually sticks. Explore the 2025 security audit checklist for enterprises. learn steps, tools, and best practices to ensure compliance, mitigate risk, and enhance cybersecurity. However, conducting a security audit requires a comprehensive approach to ensure that all possible security gaps are identified and addressed. we’ve developed a 7 step list that will ensure your next security audit is conducted appropriately and achieves its objectives. Security audit processes are essential for any organization handling digital assets. this comprehensive guide walks you through every critical phase of conducting a thorough assessment that identifies vulnerabilities and strengthens your cyber defenses. In this guide, you’ll learn about security audits, their types, how often to perform one, and a practical step by step approach to help you get it done right. what are security audits?.
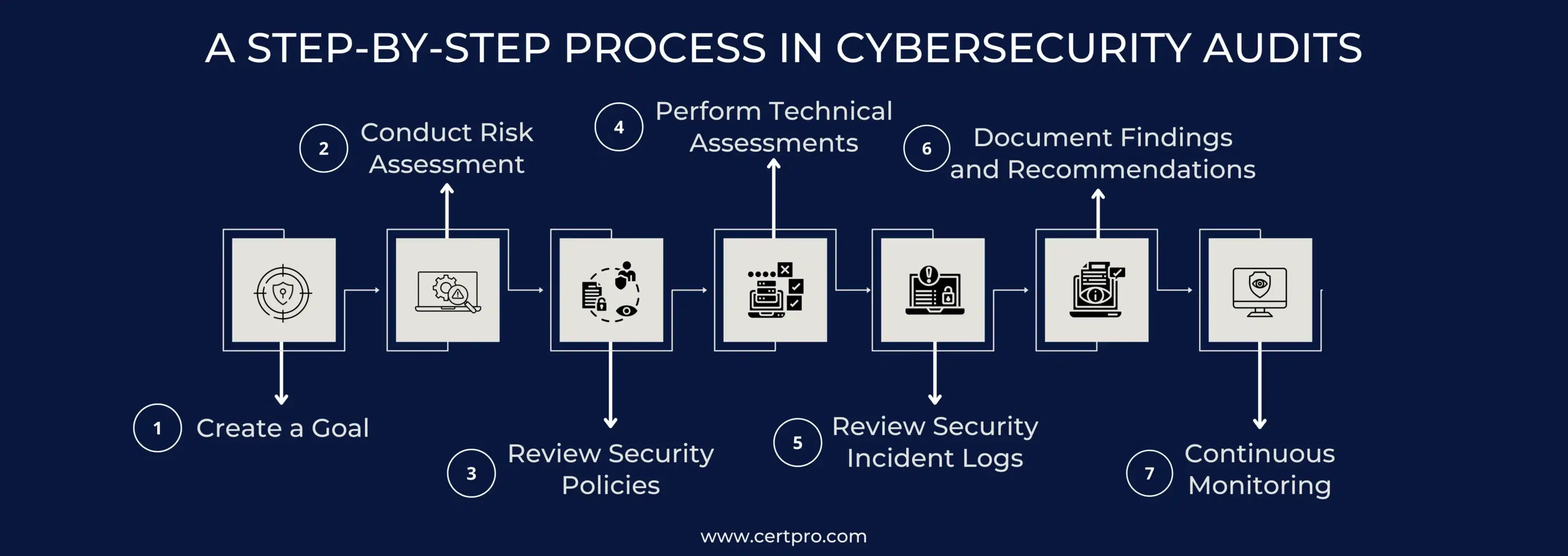
Cybersecurity Audit Protect Your Business With Best Practices Explore the 2025 security audit checklist for enterprises. learn steps, tools, and best practices to ensure compliance, mitigate risk, and enhance cybersecurity. However, conducting a security audit requires a comprehensive approach to ensure that all possible security gaps are identified and addressed. we’ve developed a 7 step list that will ensure your next security audit is conducted appropriately and achieves its objectives. Security audit processes are essential for any organization handling digital assets. this comprehensive guide walks you through every critical phase of conducting a thorough assessment that identifies vulnerabilities and strengthens your cyber defenses. In this guide, you’ll learn about security audits, their types, how often to perform one, and a practical step by step approach to help you get it done right. what are security audits?.

How To Conduct Effective Security Audits A Step By Step Guide Security audit processes are essential for any organization handling digital assets. this comprehensive guide walks you through every critical phase of conducting a thorough assessment that identifies vulnerabilities and strengthens your cyber defenses. In this guide, you’ll learn about security audits, their types, how often to perform one, and a practical step by step approach to help you get it done right. what are security audits?.

Security Audits
Comments are closed.