Security Assessment Sample Report Content Lead

Security Assessment Report Pdf Security Computer Security This is a sample assessment report for the types of security insights wiz provides you with. in this report, you will learn about the wiz inventory, which provides you with visibility into every technology u000brunning in your environment. Security assessments are a “point in time” analysis and as such, it is possible that elements in the environment have changed since the tests reflected in this report were run.
Free 5 Security Assessment Report Templates In Google Docs Ms Word This is a sample assessment report for the types of security insights wiz provides you with. Sample security assessment report from wolfe defense labs – executive summary, findings, and roadmap for an attack surface and cloud focused engagement. The template includes sections for an executive summary, background, assessment scope, summary of findings, summary of recommendations, introduction, assessment methodology, detailed findings, risk methodology, and documentation lists. The scope of the cybersecurity risk assessment included data integrity protection and security, network security, physical security, and logical security (such as it policies, it security awareness, and maintenance) of the company’s it assets.
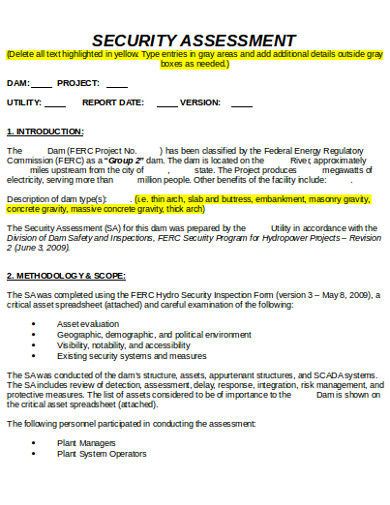
Free 5 Security Assessment Report Templates In Google Docs Ms Word The template includes sections for an executive summary, background, assessment scope, summary of findings, summary of recommendations, introduction, assessment methodology, detailed findings, risk methodology, and documentation lists. The scope of the cybersecurity risk assessment included data integrity protection and security, network security, physical security, and logical security (such as it policies, it security awareness, and maintenance) of the company’s it assets. To guide and document security assessments, organizations perform security assessments that involve generating a security assessment report (sar). these reports provide a summarization of assessment findings and corrective recommendations. Majority of the candidates are falling in “collaborative security” box indicating team’s strong focus on collaboration, resilience, discipline, and adherence to compliance and process, fostering a secure and supportive cybersecurity environment. Perform a comprehensive security assessment and penetration test of the information systems infrastructure of acme corporation (sample report) which included the following:. The essential sections every security assessment report needs. from scope definition to finding details, learn what makes reports professional and actionable.

Security Assessment Report Template A Pdf Vulnerability Computing To guide and document security assessments, organizations perform security assessments that involve generating a security assessment report (sar). these reports provide a summarization of assessment findings and corrective recommendations. Majority of the candidates are falling in “collaborative security” box indicating team’s strong focus on collaboration, resilience, discipline, and adherence to compliance and process, fostering a secure and supportive cybersecurity environment. Perform a comprehensive security assessment and penetration test of the information systems infrastructure of acme corporation (sample report) which included the following:. The essential sections every security assessment report needs. from scope definition to finding details, learn what makes reports professional and actionable.
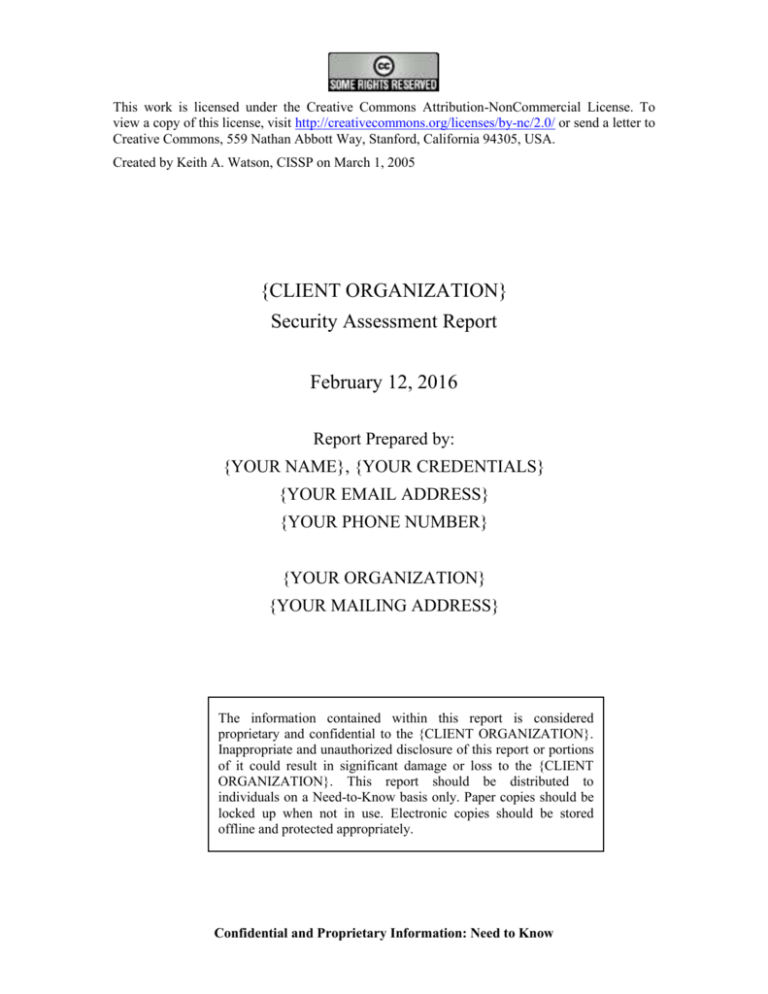
Security Assessment Report Template Prntbl Concejomunicipaldechinu Gov Co Perform a comprehensive security assessment and penetration test of the information systems infrastructure of acme corporation (sample report) which included the following:. The essential sections every security assessment report needs. from scope definition to finding details, learn what makes reports professional and actionable.

Security Assessment Sample Report Content Lead
Comments are closed.