Securing Digital Identities Best Practices For Cisos

2023 Trends In Securing Digital Identities Identity Defined Security This article explores the best practices for securing digital identities, focusing on strategic mindset shifts, proactive technical measures, and the importance of cross functional collaboration to future proof identity security. Integrating security and identity is not just a technical necessity; it’s a critical endeavor for organizations that want to protect sensitive information in today’s complex digital landscape.

2021 Trends In Securing Digital Identities Identity Defined Security Discover how cisos can lead secure digital transformation with a 2025 cloud identity management strategy grounded in best practices and zero trust principles. Effective identity protection is critical to safeguarding sensitive data and ensuring organizational resilience against cyber attacks. here are the five steps every ciso must undertake to secure their organization’s identities:. The attack surface will evolve, but the principle remains constant: identity is everything. for every ciso, making identity security the cornerstone of your cybersecurity strategy is essential. and it’s the difference between reacting to threats and staying one step ahead of them. Master essential cloud security best practices for cisos. learn about iam, data protection, monitoring, and incident response to secure your cloud environment.

5 Ways Cisos Can Prepare For Sec Cybersecurity Compliance The attack surface will evolve, but the principle remains constant: identity is everything. for every ciso, making identity security the cornerstone of your cybersecurity strategy is essential. and it’s the difference between reacting to threats and staying one step ahead of them. Master essential cloud security best practices for cisos. learn about iam, data protection, monitoring, and incident response to secure your cloud environment. As businesses embrace cloud computing, remote work, and interconnected ecosystems, digital identities representing users, devices, and applications have become prime targets for cybercriminals. In the digital age, the security of digital identities has become a defining challenge for organizations worldwide. Discover how cisos use risk based identity governance to enhance security, manage risk, and drive agility across the enterprise. To help security leaders proactively tackle today’s shifting concerns, here are what we see as our top 5 ciso priorities for this year. identities are the central piece of digital evidence.
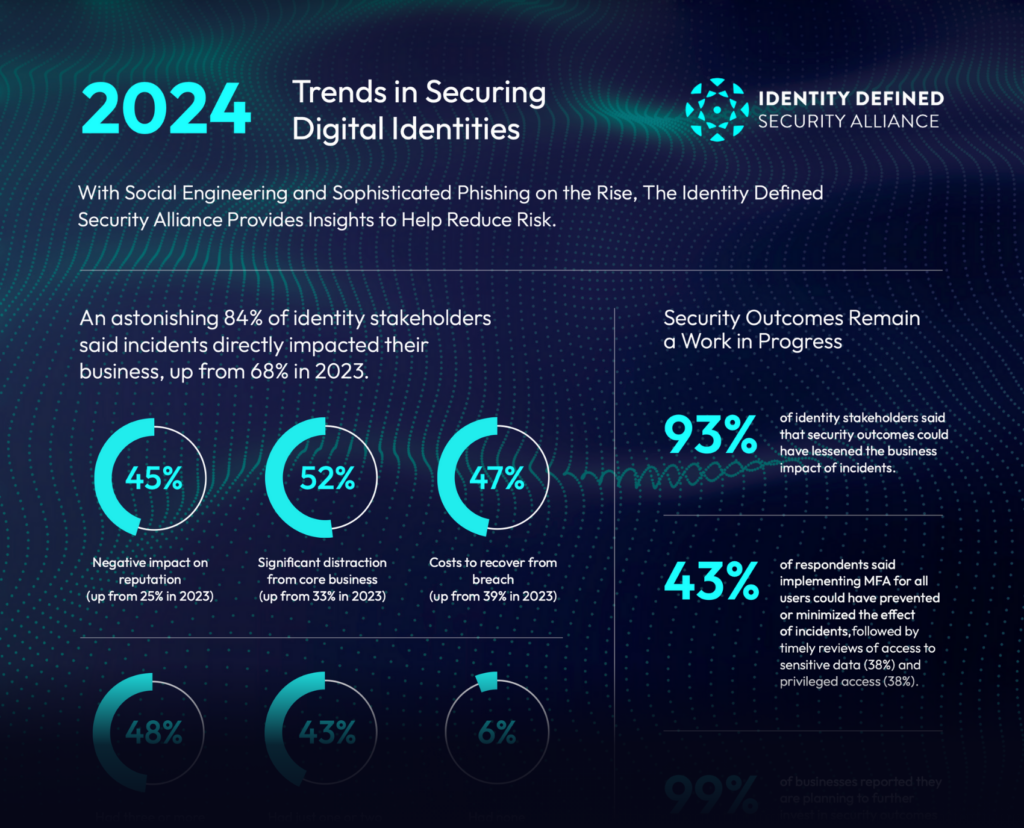
2024 Trends In Securing Digital Identities Identity Defined Security As businesses embrace cloud computing, remote work, and interconnected ecosystems, digital identities representing users, devices, and applications have become prime targets for cybercriminals. In the digital age, the security of digital identities has become a defining challenge for organizations worldwide. Discover how cisos use risk based identity governance to enhance security, manage risk, and drive agility across the enterprise. To help security leaders proactively tackle today’s shifting concerns, here are what we see as our top 5 ciso priorities for this year. identities are the central piece of digital evidence.
Comments are closed.