Secure Your Private Api Endpoints
Secure Your Private Api Endpoints Learn how to secure api endpoints with proven authentication, authorization, and monitoring strategies. complete guide to api endpoint security best practices for 2025. Secure your api endpoints with proper authentication, authorization, encryption, and input validation. complete guide with implementation examples.

How To Secure Api Endpoints From Unauthorized Access Wansafe Discover the 7 best practices for api endpoint security to protect sensitive data and prevent breaches. learn about authentication, tls ssl encryption, rate limiting, input validation, and more to safeguard your api infrastructure. This proactive approach prevents data breaches, unauthorized access, and service disruptions that can cost organizations millions in damages and reputation loss. the strategies below will help you build comprehensive api protection that scales with your cloud environment. Restrict access to your private api to specific vpcs or vpc endpoints. add aws:sourcevpc or aws:sourcevpce conditions to your api's resource policy to restrict access. In this article, we shall consider the 7 best practices that combine detailed explanations with concise bullet points to sustain robust api shielding against shifting dangers, hence protecting internet assets and improving trust by users. what is api security and why does it matters?.
Api Security Protecting Your Endpoints Bizdev Restrict access to your private api to specific vpcs or vpc endpoints. add aws:sourcevpc or aws:sourcevpce conditions to your api's resource policy to restrict access. In this article, we shall consider the 7 best practices that combine detailed explanations with concise bullet points to sustain robust api shielding against shifting dangers, hence protecting internet assets and improving trust by users. what is api security and why does it matters?. You can configure an inbound private endpoint for your api management instance to allow clients in your private network to securely access the instance over azure private link. Insecure api endpoints can be exploited by attackers, leading to data breaches, unauthorized access, and other severe consequences. in this blog, we'll explore best practices for securing api endpoints to ensure that your data and services are protected. Securing api endpoints is crucial in today’s digital landscape, and knowing how to secure api endpoints with tls and ssl encryption is your best defense against the ever growing threat landscape. By combining function apps, apim, openapi registration, outbound policies, and private endpoints, you create a secure, consistent, and maintainable api platform.

The Ultimate Guide To Api Security Protecting Your Data And Users You can configure an inbound private endpoint for your api management instance to allow clients in your private network to securely access the instance over azure private link. Insecure api endpoints can be exploited by attackers, leading to data breaches, unauthorized access, and other severe consequences. in this blog, we'll explore best practices for securing api endpoints to ensure that your data and services are protected. Securing api endpoints is crucial in today’s digital landscape, and knowing how to secure api endpoints with tls and ssl encryption is your best defense against the ever growing threat landscape. By combining function apps, apim, openapi registration, outbound policies, and private endpoints, you create a secure, consistent, and maintainable api platform.
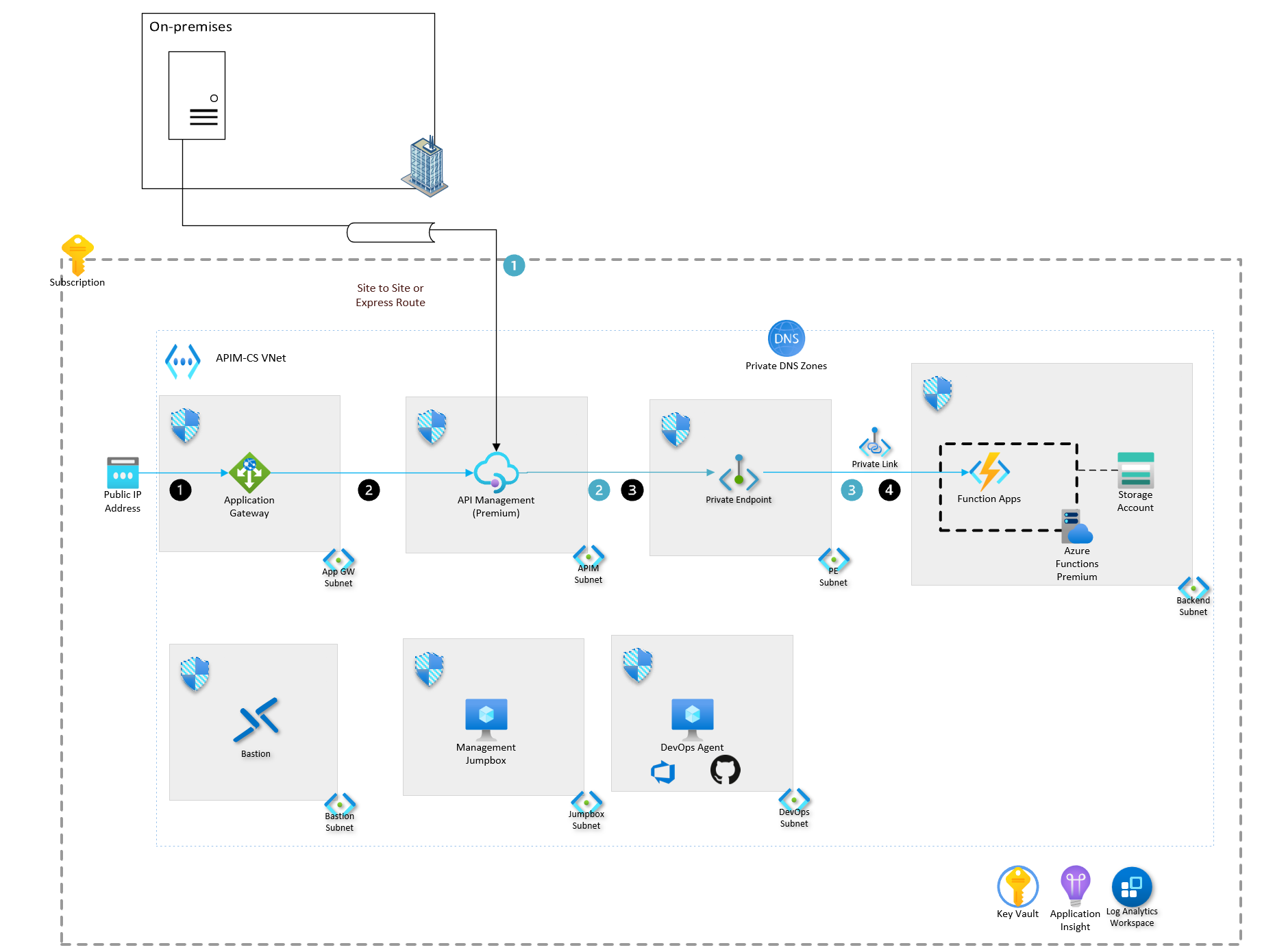
Secure Endpoints Rest Api At Rosie Mireles Blog Securing api endpoints is crucial in today’s digital landscape, and knowing how to secure api endpoints with tls and ssl encryption is your best defense against the ever growing threat landscape. By combining function apps, apim, openapi registration, outbound policies, and private endpoints, you create a secure, consistent, and maintainable api platform.
Comments are closed.