Secure Shell Ssh Unlocking Secure Remote Access Pdf Secure Shell

Ssh Shell Secure Milolab This chapter provides guidelines for configuring ssh (secure shell) securely for system administrators running ssh on unix systems. the focus is on establishing a secure system, even at the expense of flexibility. Implementations of secure shell offer the following capabilities: a secure command shell, secure file transfer, and remote access to a variety of tcp ip applications via a secure tunnel.

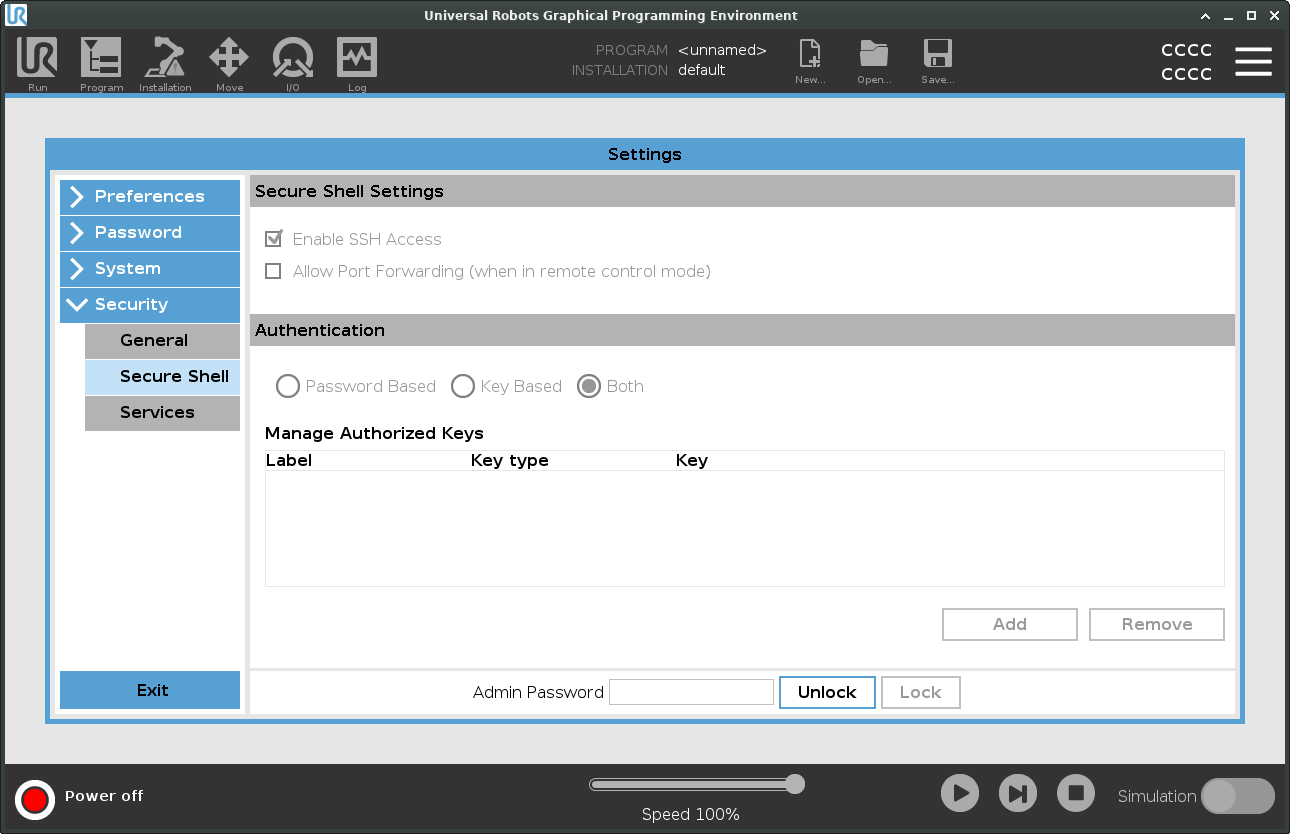
How Do Secure Shell Ssh Keys Work Encryption Consulting Secure shell ssh unlocking secure remote access free download as pdf file (.pdf), text file (.txt) or read online for free. secure shell (ssh) is a protocol that provides encrypted communication for secure remote access, allowing users to log in to remote systems, run commands, and transfer files safely. Since ssh is a powerful tool which often grants a lot of access to anyone using it to login into a server, it’s critical to make your ssh model as secure as possible. this tech paper proposes three approaches to achieving that, covering each in a chapter:. Encrypting protocols which are not normally encrypted (e.g. vnc). no setup – already done! the screen display shows up on your computer, and any keystrokes and mouse movements are sent back, all encrypted. The purpose of this document is to assist organizations in understanding the basics of secure shell (ssh) and ssh access management in an enterprise, focusing on the management of ssh user keys.

Secure Shell Encrypting protocols which are not normally encrypted (e.g. vnc). no setup – already done! the screen display shows up on your computer, and any keystrokes and mouse movements are sent back, all encrypted. The purpose of this document is to assist organizations in understanding the basics of secure shell (ssh) and ssh access management in an enterprise, focusing on the management of ssh user keys. What is ssh? it is a set of standards and associated protocols to establish a secure channel between two computers. it provides mutual authentication, data confidentiality, and data integrity. originally, it was designed as a replacement of insecure applications like r commands (i.e., berkeley remote commands, e.g., rlogin, rsh, rcp). One possible application of an ssh private key without a password would be to allow automated scripts to log into remote machines and perform actions. we'll cover this kind of functionality more in the scripting course, but for now we'll focus on using ssh keys for authentication. Openssh secures communications between networked systems. this document includes content that was tested against oracle linux 8, oracle linux 9, and oracle linux 10, but generally applies to most oracle linux releases, and might also apply to other distributions. Features of ssh encrypted login and shell connection easy, drop in replacement for rlogin, rsh, rcp multiple means of authentication.

Secure Shell What is ssh? it is a set of standards and associated protocols to establish a secure channel between two computers. it provides mutual authentication, data confidentiality, and data integrity. originally, it was designed as a replacement of insecure applications like r commands (i.e., berkeley remote commands, e.g., rlogin, rsh, rcp). One possible application of an ssh private key without a password would be to allow automated scripts to log into remote machines and perform actions. we'll cover this kind of functionality more in the scripting course, but for now we'll focus on using ssh keys for authentication. Openssh secures communications between networked systems. this document includes content that was tested against oracle linux 8, oracle linux 9, and oracle linux 10, but generally applies to most oracle linux releases, and might also apply to other distributions. Features of ssh encrypted login and shell connection easy, drop in replacement for rlogin, rsh, rcp multiple means of authentication.
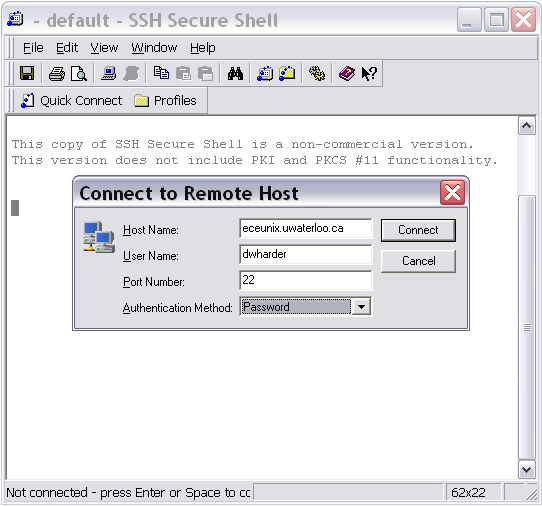
Ssh Secure Shell Client Mte 241 University Of Waterloo Openssh secures communications between networked systems. this document includes content that was tested against oracle linux 8, oracle linux 9, and oracle linux 10, but generally applies to most oracle linux releases, and might also apply to other distributions. Features of ssh encrypted login and shell connection easy, drop in replacement for rlogin, rsh, rcp multiple means of authentication.
Secure Shell
Comments are closed.