How Do Secure Shell Ssh Keys Work Encryption Consulting

How Do Secure Shell Ssh Keys Work Encryption Consulting Secure shell (ssh) is the network protocol that provides a secure way for two devices like computers to connect remotely. ssh employs encryption to ensure that attackers cannot interpret the connection or traffic between two connected devices. Ssh uses this technique to authenticate users and securely exchange keys without exposing sensitive information. public key is shared openly, while the private key remains secret.

Ssh Secure Shell Pdf Using a number of encryption technologies, ssh provides a mechanism for establishing a cryptographically secured connection between two parties, authenticating each side to the other, and passing commands and output back and forth. A session key in ssh is an encryption key used for encrypting the bulk of the data in a connection. the session key is negotiated during the connection and then used with a symmetric encryption algorithm and a message authentication code algorithm to protect the data. The purpose of this article was to make the user aware of how ssh establishes secure communication between two systems. hopefully, i've offered some insight into that process. Understand the purpose and importance of ssh keys for secure remote access. learn how ssh keys work and how to effectively use them.
What Is Secure Shell Ssh How Does Secure Shell Work The purpose of this article was to make the user aware of how ssh establishes secure communication between two systems. hopefully, i've offered some insight into that process. Understand the purpose and importance of ssh keys for secure remote access. learn how ssh keys work and how to effectively use them. Ssh (secure shell) keys are a pair of cryptographic keys used to authenticate a client to a server without transmitting a password over the network. the pair consists of a private key (kept secret on your machine) and a public key (placed on the server you want to access). Ssh is a secure shell protocol, so every communication inside ssh must be secure. that’s why here we need a key exchange process to make sure ssh communication is encrypted securely. All enterprises rely on secure shell (ssh) keys to authenticate privileged users and establish trusted access to critical systems, including application servers, routers, firewalls, virtual machines, cloud instances, and many other devices and systems. Secure shell (ssh) keys are a pair of cryptographic keys that are used to authenticate a client to an ssh server without the use of passwords. this technology was developed to increase the strength and complexity of authentication, thus significantly enhancing cybersecurity.
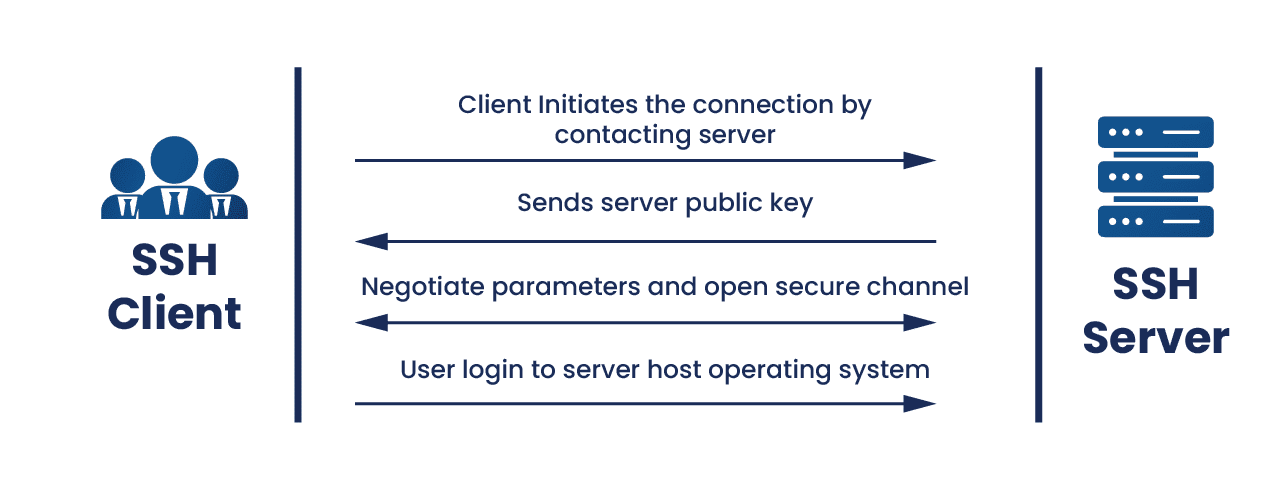
What Is Secure Shell Ssh How Does Secure Shell Work Ssh (secure shell) keys are a pair of cryptographic keys used to authenticate a client to a server without transmitting a password over the network. the pair consists of a private key (kept secret on your machine) and a public key (placed on the server you want to access). Ssh is a secure shell protocol, so every communication inside ssh must be secure. that’s why here we need a key exchange process to make sure ssh communication is encrypted securely. All enterprises rely on secure shell (ssh) keys to authenticate privileged users and establish trusted access to critical systems, including application servers, routers, firewalls, virtual machines, cloud instances, and many other devices and systems. Secure shell (ssh) keys are a pair of cryptographic keys that are used to authenticate a client to an ssh server without the use of passwords. this technology was developed to increase the strength and complexity of authentication, thus significantly enhancing cybersecurity.
Comments are closed.