Secure Provisioning Configuration

Secure Configuration Standard Pdf Computer Security Security Whether you are new to secure boot and encryption workflows or looking to integrate secure provisioning into your production process, this guide will help you get started quickly. Secure provisioning is the process of configuring embedded devices with trusted firmware, device specific cryptographic credentials, and configuration parameters in a way that guarantees authenticity and confidentiality.
Provisioning Versus Configuration Devops Secure provisioning allows you to claim a device as your own and provision the device remotely. it allows you to define a device’s provisioning configuration, define rules that apply to multiple devices, control who within your team can provision the device, and block or unclaim the device. Whether you are new to secure boot and encryption workflows or looking to integrate secure provisioning into your production process, this guide will help you get started quickly. New users should find it easier to prepare, flash, and secure images, while experienced users rediscover features from the existing toolset (sdphost, blhost, nxpimage, and so on) under a friendlier gui. experienced users can further customize secure provisioning flows by modifying scripts generated by the tool. figure 1. Earlier in this series we covered cryptographic functions. so, with this newly gained knowledge let us examine, in detail, how these are used in the typical workflow of secure provisioning.
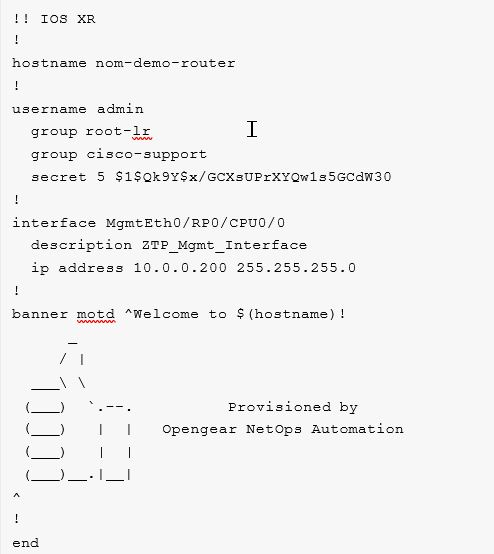
Secure Provisioning Configuration New users should find it easier to prepare, flash, and secure images, while experienced users rediscover features from the existing toolset (sdphost, blhost, nxpimage, and so on) under a friendlier gui. experienced users can further customize secure provisioning flows by modifying scripts generated by the tool. figure 1. Earlier in this series we covered cryptographic functions. so, with this newly gained knowledge let us examine, in detail, how these are used in the typical workflow of secure provisioning. This includes serial numbers, mac addresses, provisioning timestamps, and security configuration. this data supports inventory tracking, warranty management, and customer support operations. This chapter describes client provisioning functions in cisco ise that allows you to download client provisioning resources and configure agent profiles for windows and mac os x clients, and native supplicant profiles for your own personal devices. It does not generate, test or validate device configuration. instead, it is focused on provisioning remote managed devices with user supplied configuration and device os images – automatically, remotely and securely, no matter where those devices are and no matter what the state of the network is. The unified provisioning support in the esp idf provides an extensible mechanism to the developers to configure the device with the wi fi credentials and or other custom configuration using various transports and different security schemes.

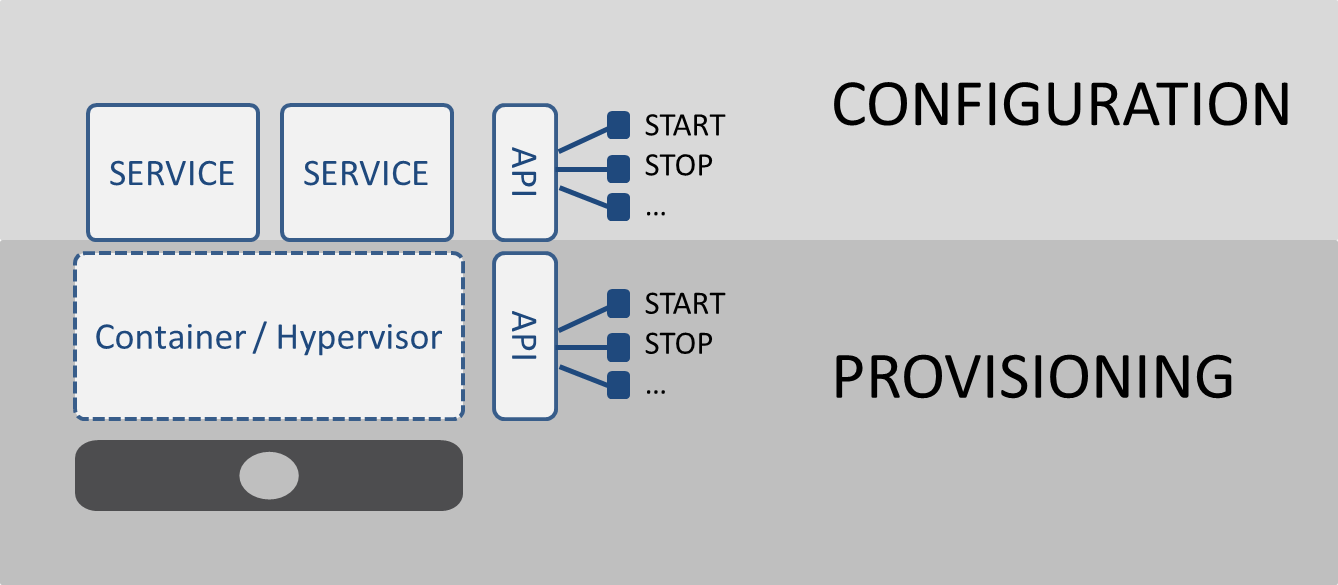
Configuration And Provisioning Download Scientific Diagram This includes serial numbers, mac addresses, provisioning timestamps, and security configuration. this data supports inventory tracking, warranty management, and customer support operations. This chapter describes client provisioning functions in cisco ise that allows you to download client provisioning resources and configure agent profiles for windows and mac os x clients, and native supplicant profiles for your own personal devices. It does not generate, test or validate device configuration. instead, it is focused on provisioning remote managed devices with user supplied configuration and device os images – automatically, remotely and securely, no matter where those devices are and no matter what the state of the network is. The unified provisioning support in the esp idf provides an extensible mechanism to the developers to configure the device with the wi fi credentials and or other custom configuration using various transports and different security schemes.
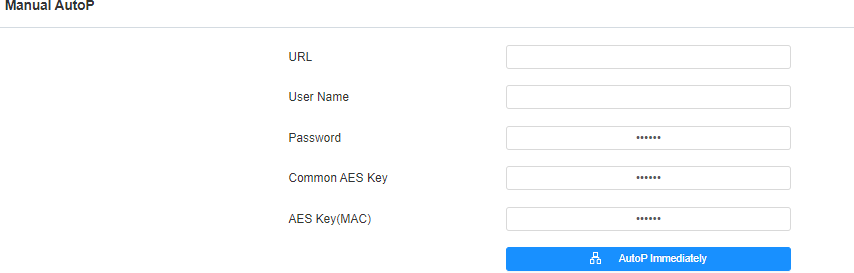
Auto Provisioning Via Configuration File It does not generate, test or validate device configuration. instead, it is focused on provisioning remote managed devices with user supplied configuration and device os images – automatically, remotely and securely, no matter where those devices are and no matter what the state of the network is. The unified provisioning support in the esp idf provides an extensible mechanism to the developers to configure the device with the wi fi credentials and or other custom configuration using various transports and different security schemes.
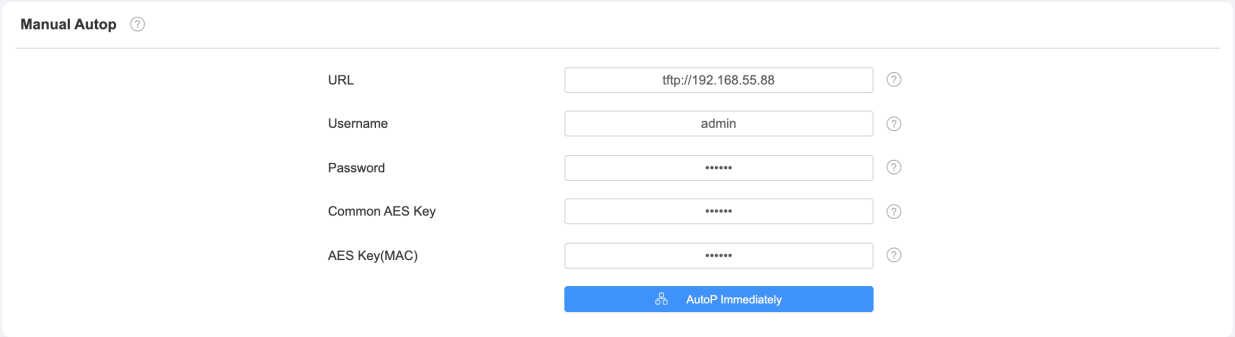
Auto Provisioning Via Configuration File
Comments are closed.