Secure Multi Party Computation Secure Circuit Evaluation Explained

Secure Multi Party Computation Pdf The foundation for secure multi party computation started in the late 1970s with the work on mental poker, cryptographic work that simulates game playing computational tasks over distances without requiring a trusted third party. We cover garbled circuit evaluation (gce) and linear secret sharing (lss) which are commonly used for secure two party and multi party computation, respectively. the coverage includes both standard adversarial models: semi honest and malicious.

Secure Multi Party Computation Smpc Latentview Analytics Designing and implementing circuits for five compelling secure multi party computation tasks. these tasks represent five key mpc problems that cover most of the applications suggested in literature, namely, auction, voting, set inter section, stable matching, and nearest neighbor search. With the use of the cryptographic approach known as "secure multiparty computation, "n parties can securely compute a function together without disclosing each other's unique inputs. this preserves data privacy while enabling computations and analysis. This chapter provides an overview of secure multiparty computation, beginning with its definition. it then introduces several protocols used in secure multiparty computation. the chapter offers a thorough understanding of various techniques in this field. Secure multi party computation (mpc) is one of the most influential achievements of modern cryptography: it allows evaluation of an arbitrary function on privat.
Secure Multi Party Computation This chapter provides an overview of secure multiparty computation, beginning with its definition. it then introduces several protocols used in secure multiparty computation. the chapter offers a thorough understanding of various techniques in this field. Secure multi party computation (mpc) is one of the most influential achievements of modern cryptography: it allows evaluation of an arbitrary function on privat. Secure multi party computation (mpc) is a set of cryptographic protocols that let multiple parties jointly compute a function over their private inputs without revealing those inputs to each other. This task can be achieved using a multi party computation (mpc scheme). mpc enables multiple parties to jointly compute a function over their inputs while keeping those inputs private. For every pair (i,j), i≠j, party i picks random aij and lets party j securely compute bij s.t. aij bij = [u]i[v]j using the naive protocol (a single 1 out of 2 ot). Before presenting the garbled circuit protocol, this paper introduces secure multi party computation, explaining the canonical millionaire problem. we then examine oblivious transfer, a necessary tool in yao’s protocol.
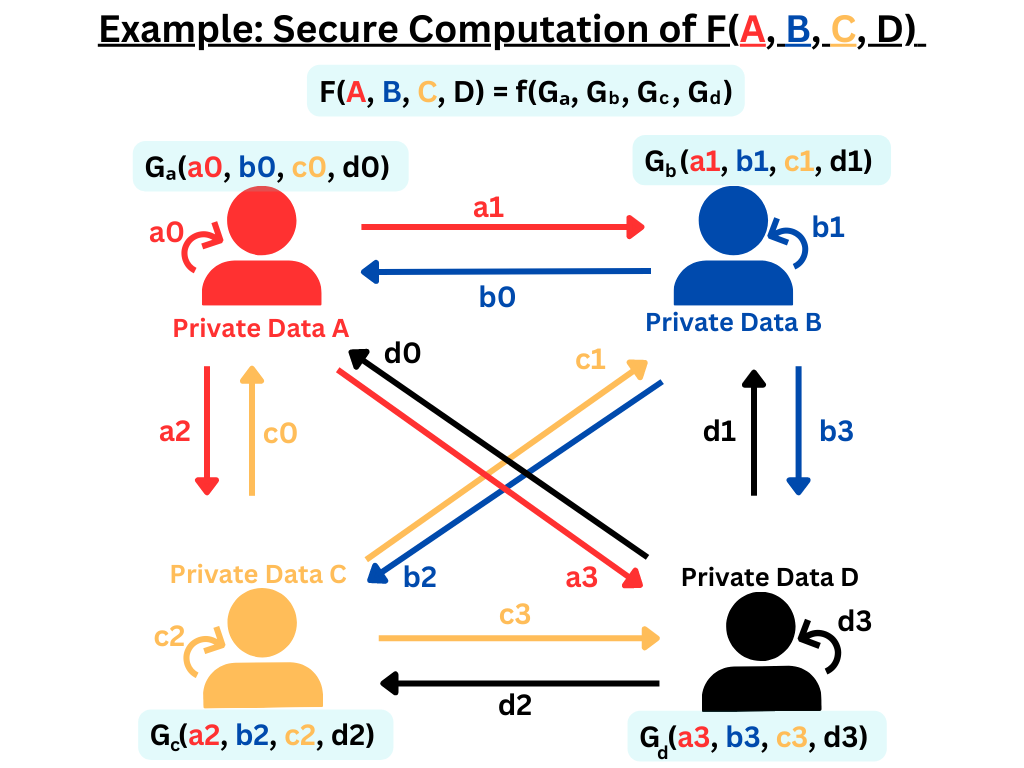
Secure Multi Party Computation Solutions Iudx Secure multi party computation (mpc) is a set of cryptographic protocols that let multiple parties jointly compute a function over their private inputs without revealing those inputs to each other. This task can be achieved using a multi party computation (mpc scheme). mpc enables multiple parties to jointly compute a function over their inputs while keeping those inputs private. For every pair (i,j), i≠j, party i picks random aij and lets party j securely compute bij s.t. aij bij = [u]i[v]j using the naive protocol (a single 1 out of 2 ot). Before presenting the garbled circuit protocol, this paper introduces secure multi party computation, explaining the canonical millionaire problem. we then examine oblivious transfer, a necessary tool in yao’s protocol.
About Secure Multi Party Computation For every pair (i,j), i≠j, party i picks random aij and lets party j securely compute bij s.t. aij bij = [u]i[v]j using the naive protocol (a single 1 out of 2 ot). Before presenting the garbled circuit protocol, this paper introduces secure multi party computation, explaining the canonical millionaire problem. we then examine oblivious transfer, a necessary tool in yao’s protocol.
Comments are closed.