Secure Coding Practices A Q A On Embedded Software Security

Secure Coding Practices Pdf Password Http Cookie In this q&a, rolland offers a straight from the trenches look at secure coding, from the easy to miss mistakes that cause the biggest headaches, to the right way to layer security tools, to what “memory safety” really means in practice. Trustinsoft spoke with senior software engineer at runsafe security mitch souders to hear his perspective on the state of embedded software security and the most prevalent issues likely to affect the future of software security.

Secure Coding Practices A Q A On Embedded Software Security Secure coding practices for embedded systems ensure the safety and integrity of these devices. our comprehensive guide provides essential techniques for protecting embedded systems from vulnerabilities. Writing secure code is essential to mitigate risks such as unauthorized access, data breaches, and tampering. in this technical blog, we’ll explore best practices for secure embedded c. This article provides a detailed guide to secure embedded systems programming, focusing on buffer overflow prevention and mitigation, secure coding practices, and memory management. This guide provides coding practices that can be translated into coding requirements without the need for the developer to have an in depth understanding of security vulnerabilities and exploits.

Nurturing Software Security A Guide To Secure Coding Practices This article provides a detailed guide to secure embedded systems programming, focusing on buffer overflow prevention and mitigation, secure coding practices, and memory management. This guide provides coding practices that can be translated into coding requirements without the need for the developer to have an in depth understanding of security vulnerabilities and exploits. Learn how to securely code embedded systems in this online course. gain skills to architect secure systems, implement cryptography and iam, sanitize inputs outputs, harden systems, and release secure updates. Developers should follow secure coding practices and apply early risk assessment to address vulnerabilities before they are embedded in the firmware. a formalized sdlc should include security testing stages at every phase of software development. It defines specific security practices and requirements for each phase of development, emphasizing training, threat modeling, secure coding standards, security testing, and incident response. We discuss the challenges and best practices for securing embedded systems from various types of malicious events, and also explore security concepts and standards that make it easier to implement.

Unlocking Sustainable Security Practices With Secure Coding Education Learn how to securely code embedded systems in this online course. gain skills to architect secure systems, implement cryptography and iam, sanitize inputs outputs, harden systems, and release secure updates. Developers should follow secure coding practices and apply early risk assessment to address vulnerabilities before they are embedded in the firmware. a formalized sdlc should include security testing stages at every phase of software development. It defines specific security practices and requirements for each phase of development, emphasizing training, threat modeling, secure coding standards, security testing, and incident response. We discuss the challenges and best practices for securing embedded systems from various types of malicious events, and also explore security concepts and standards that make it easier to implement.
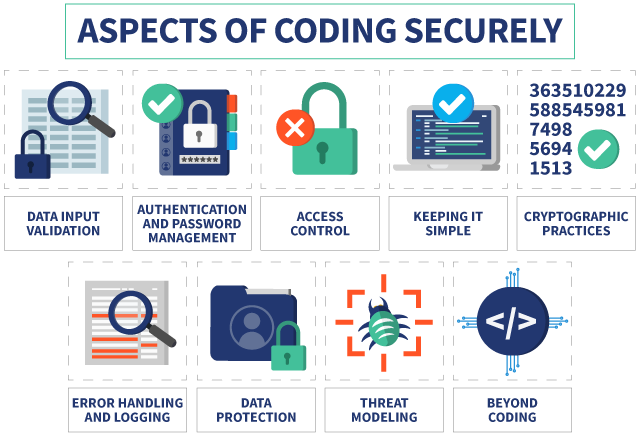
Enhancing Software Security Through Secure Coding Practices It defines specific security practices and requirements for each phase of development, emphasizing training, threat modeling, secure coding standards, security testing, and incident response. We discuss the challenges and best practices for securing embedded systems from various types of malicious events, and also explore security concepts and standards that make it easier to implement.
Comments are closed.