Secure Boot In Embedded Linux Best Practices Guide

Secure Boot In Embedded Linux Best Practices Guide Learn key secure boot best practices for embedded linux, including signing, verification, and device protection to ensure trusted, tamper proof systems. Learn how secure boot protects embedded linux devices from firmware threats and ensures compliance with eu cyber resilience act (cra).

Secure Boot Witekio Secure boot is a critical security mechanism designed to protect embedded systems against various threats. discover how to implement it in your system. Discover how secure boot, dm verity, and hash trees create a verified chain of trust in embedded linux, protecting devices from unauthorized code. You’ll learn how to build a successful, secure, and user friendly solution by exploring the critical hardware and software components that form the foundation of a secure appliance. Presenting one of available solutions based on: nxp i.mx8 ahab secure boot u boot verified boot dm init dm verity.
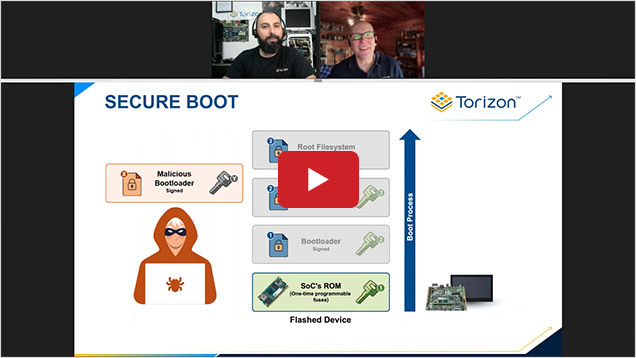
Safeguard Your Embedded Linux Devices With Secure Boot You’ll learn how to build a successful, secure, and user friendly solution by exploring the critical hardware and software components that form the foundation of a secure appliance. Presenting one of available solutions based on: nxp i.mx8 ahab secure boot u boot verified boot dm init dm verity. In the linux ecosystem, secure boot provides an additional layer of security by ensuring that only trusted software components are loaded during the boot process. this blog post will delve into the fundamental concepts of secure boot in linux, its usage methods, common practices, and best practices. Discover how secure boot and firmware hardening protect uefi, windows, linux, and embedded systems against bootkits and advanced attacks. Learn about secure boot mechanisms, their importance in embedded systems, and how to implement them effectively to prevent malware and ensure device security. The national security agency (nsa) of the united states released its “uefi secure boot customization” guidelines for configuring platform firmware to take advantage of the security promise provided by secure boot.
Comments are closed.