Secure Application Management Getting Started

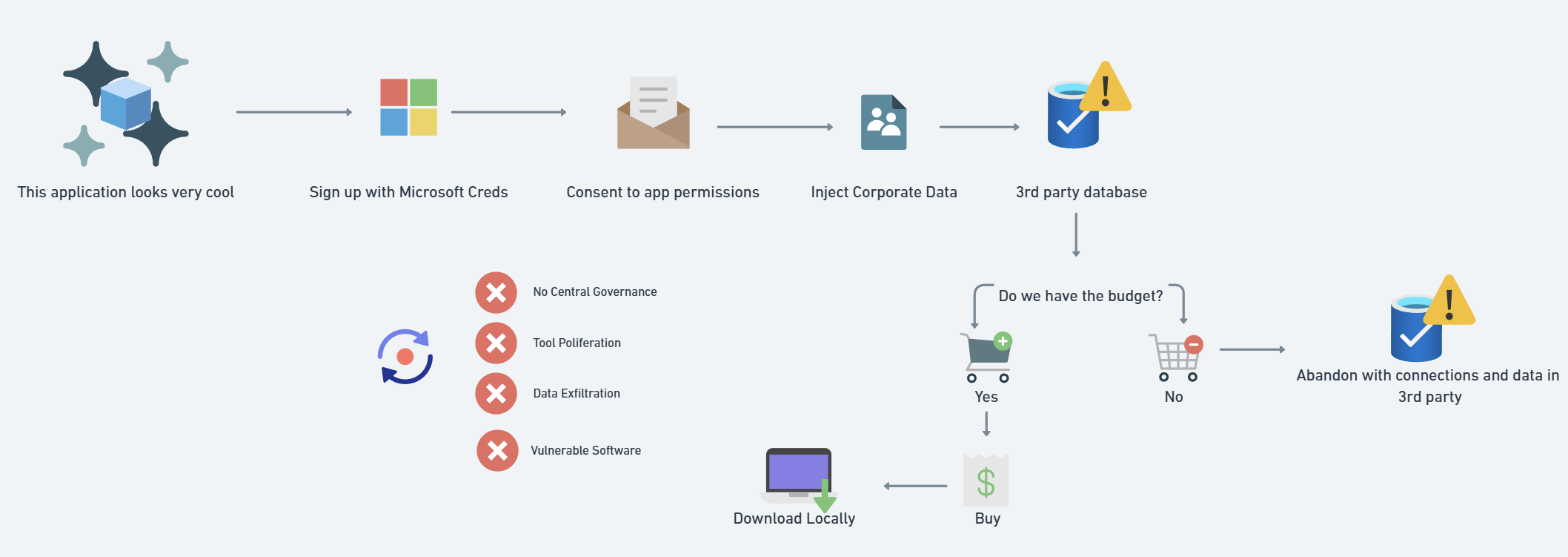
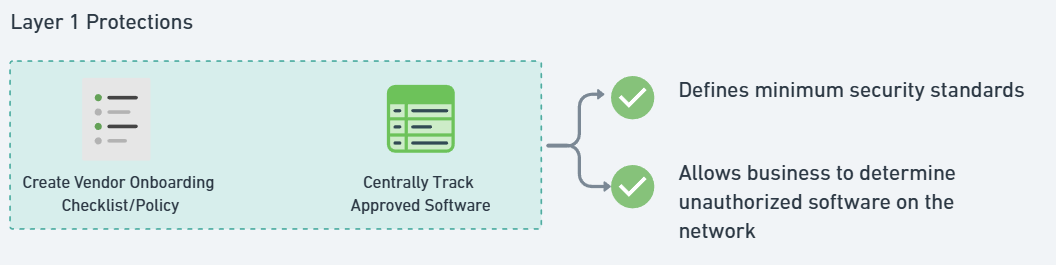
Secure Application Management Getting Started In this video, i dive into how to take control of your business’s software inventory using microsoft 365 security tools. with the rise of shadow it, unauthorized app registrations, and saas tool. In this blog series, we’re going to break down software inventory management and security, mapping it directly to cis control 2 (inventory & control of software assets). we’ll also dive into microsoft 365’s security tools, showing you how to protect your organization against these risks.

Secure Application Management Getting Started Secure application management involves integrating security practices into every stage of software application development, deployment, and maintenance to protect against sophisticated threats. Find the guides to help you get started, install keycloak, and configure it and your applications to match your needs. Step 1: ensure that all requirements are met, and that the licensed version of supported apm agent is installed. check the required version of the controller and apm agent. step 2: obtain the secure application license. note: you cannot proceed to the next step until a license is provisioned. The secure application manager option provides secure, application level remote access to enterprise servers from client applications. you may deploy two versions of the secure application manager:.
Secure Application Management Getting Started Step 1: ensure that all requirements are met, and that the licensed version of supported apm agent is installed. check the required version of the controller and apm agent. step 2: obtain the secure application license. note: you cannot proceed to the next step until a license is provisioned. The secure application manager option provides secure, application level remote access to enterprise servers from client applications. you may deploy two versions of the secure application manager:. Application security managertm (asm) is a web application firewall that secures web applications and protects them from vulnerabilities. asm also helps to ensure compliance with key regulatory mandates, such as hipaa and pci dss. Application management in microsoft entra id is the process of creating, configuring, managing, and monitoring applications in the cloud. when an application is registered in a microsoft entra tenant, users who are already assigned to it can securely access it. Whether you are just getting started and you need to learn how to integrate your firewall into the network, or you are setting up advanced features to prevent credential theft and thwart an attacker’s ability to use stolen credentials to move laterally through your network, you'll find the help you need in the pan os documentation. Secure applications are essential to strong cybersecurity. learn why vulnerabilities in software pose serious risks, and how application security skills are in high demand—plus how isc2’s new express course helps professionals get started in this critical domain.
Secure Application Management Getting Started Application security managertm (asm) is a web application firewall that secures web applications and protects them from vulnerabilities. asm also helps to ensure compliance with key regulatory mandates, such as hipaa and pci dss. Application management in microsoft entra id is the process of creating, configuring, managing, and monitoring applications in the cloud. when an application is registered in a microsoft entra tenant, users who are already assigned to it can securely access it. Whether you are just getting started and you need to learn how to integrate your firewall into the network, or you are setting up advanced features to prevent credential theft and thwart an attacker’s ability to use stolen credentials to move laterally through your network, you'll find the help you need in the pan os documentation. Secure applications are essential to strong cybersecurity. learn why vulnerabilities in software pose serious risks, and how application security skills are in high demand—plus how isc2’s new express course helps professionals get started in this critical domain.
Comments are closed.