Sdas Secure Remote Access In Action
Sda S Secure Remote Access In Action Sda Stay up to date. subscribe for our latest news. Do you want to know what secure remote access in a software defined automation console looks like? meet amir, who will explain how secure remote access and c.

Remote Access Security Best Practices Upd Ev Pdf Secure remote access offers a lightweight implementation—a small software install, no hardware required—and setup is easy and fast. our gateway, included at no extra cost, uses standard network ports and provides best practice encryption in transit. Introducing sd access automates user and device policy for any application across the wireless and wired network via a single network fabric. In this post, we demonstrate how to set up quick, constrained, and time bound authentication and authorization to remote data sources in azure data lake storage (adls) using a shared access signature (sas) when running apache spark jobs via emr notebooks attached to an emr cluster. Substations, once designed as locally operated and heavily hardwired installations, are now required to function as intelligent, remotely supervised nodes within a highly interconnected grid. this shift has given rise to the widespread adoption of substation automation systems (sas).

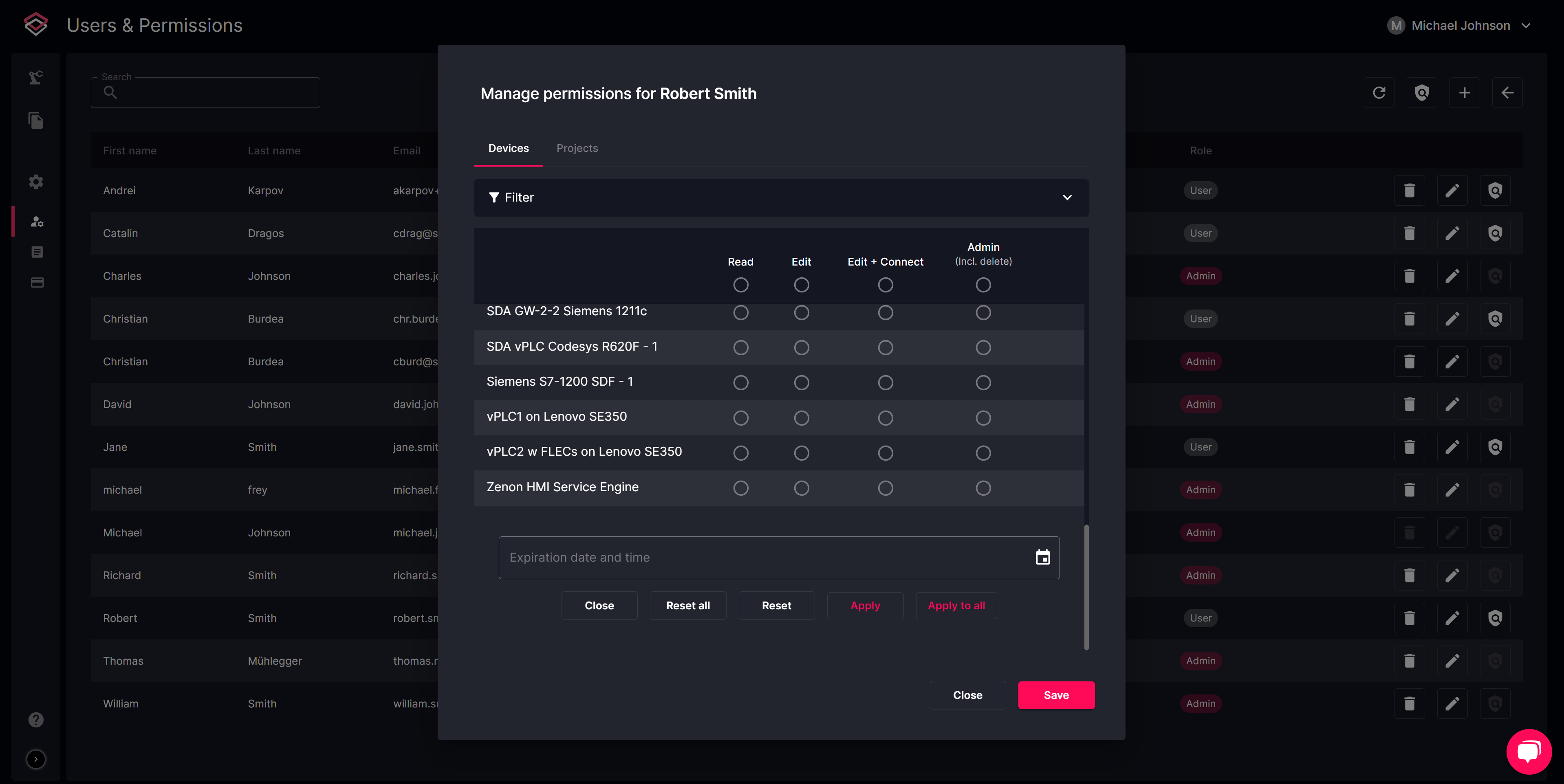
Sdas Remote Access Unit In this post, we demonstrate how to set up quick, constrained, and time bound authentication and authorization to remote data sources in azure data lake storage (adls) using a shared access signature (sas) when running apache spark jobs via emr notebooks attached to an emr cluster. Substations, once designed as locally operated and heavily hardwired installations, are now required to function as intelligent, remotely supervised nodes within a highly interconnected grid. this shift has given rise to the widespread adoption of substation automation systems (sas). Learn about using shared access signatures (sas) to delegate access to azure storage resources, including blobs, queues, tables, and files. This article gives an overview of the cisco sda. the cisco sd access architecture and its physical layer are also explained. While there are beneficial features and legitimate uses of remote access software, malicious actors often exploit these products to evade detection and establish network connections through cloud hosted infrastructure. Instead of securing the perimeter around the network, sda isolates the user and, in turn, limits the scope of a potential breach. sda can be delivered via in line software, as a cloud service or, in some cases, on prem.
Comments are closed.