Scripting Ghidra Memory Map
Github Alex Bellon Ghidra Label From Memory Map Canon firmware loads some binary parts from rom into a various memory locations. those needs to be properly defined loaded into a project before reverse engineering starts. the goal of this article is to combine those two together into a memory map in ghidra. The expand down< i> action is enabled when exactly one memory block is selected. use the expand block down< i> dialog to cause a memory block to grow by adding additional bytes after the memory block.
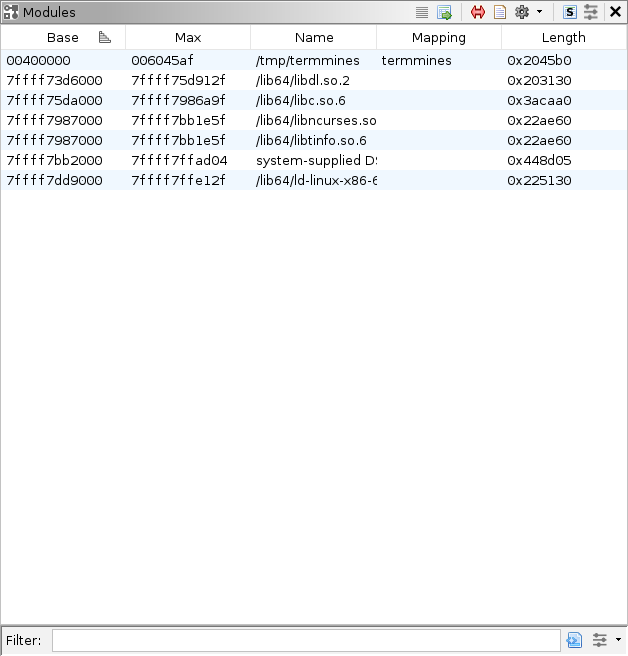
Ghidra Debugger Ghidra is an awesome re tool that quickly took off after its initial launch in 2019. it can display not only the disassembly of our binary but also have a decompiler that allows us to see a bit. The memory map window displays a list of memory blocks that make up the memory structure of the current program. the component provides actions for adding, renaming, moving, splitting, extending, joining, and deleting memory blocks. For example, here is memory layout created by python script: i want a) split ram in two blocks: .text (code) and .data (data), and b) add 2 new blocks: .bss and stack. (both as overlay) i set the start address to 0x80004000, and imported binary. All memory block manipulations require excusive access (see domainobject.hasexclusiveaccess ()) and all memory changes should generally be completed prior to analysis. in particular, adding additional overlay blocks to an existing overlay space that has already been analyzed should be avoided.
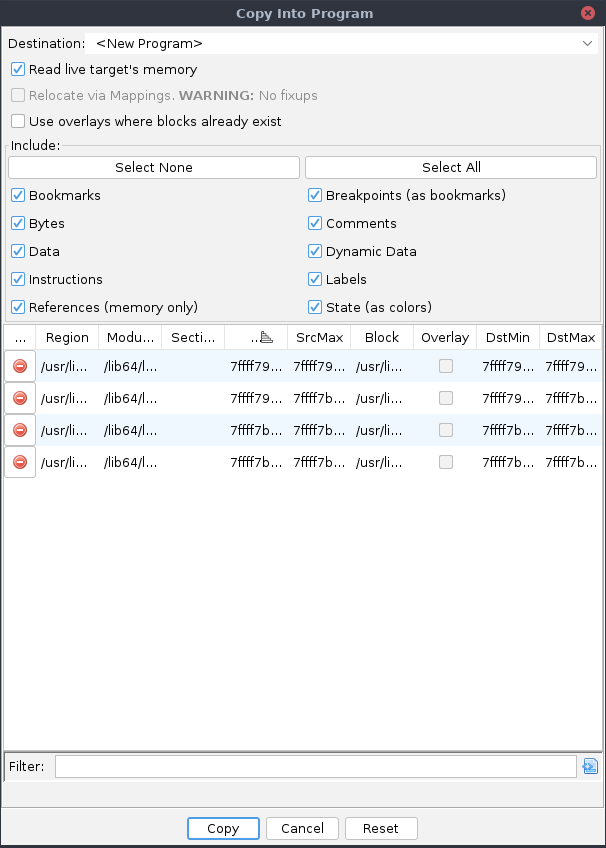
Ghidra Debugger For example, here is memory layout created by python script: i want a) split ram in two blocks: .text (code) and .data (data), and b) add 2 new blocks: .bss and stack. (both as overlay) i set the start address to 0x80004000, and imported binary. All memory block manipulations require excusive access (see domainobject.hasexclusiveaccess ()) and all memory changes should generally be completed prior to analysis. in particular, adding additional overlay blocks to an existing overlay space that has already been analyzed should be avoided. In this post, we’ll be building on the concepts we learned in part 0 and introduce some new topics including converting applying data types, function call trees graphs, the script manager and memory map. The nearest analog from the codebrowser is the memory map window. unlike the memory map window, the regions window includes all regions mapped to external modules, as well as regions allocated for stacks, heaps, or other system objects. Community dedicated to discussion about the national security agency's reverse engineering framework, ghidra. Create a byte mapped memory block and add it to this memory. each byte address within the resulting memory block will correspond to a byte within the mapped region specified by mappedaddress.

Reverse Engineering Ghidra Memory Map Dokuwiki In this post, we’ll be building on the concepts we learned in part 0 and introduce some new topics including converting applying data types, function call trees graphs, the script manager and memory map. The nearest analog from the codebrowser is the memory map window. unlike the memory map window, the regions window includes all regions mapped to external modules, as well as regions allocated for stacks, heaps, or other system objects. Community dedicated to discussion about the national security agency's reverse engineering framework, ghidra. Create a byte mapped memory block and add it to this memory. each byte address within the resulting memory block will correspond to a byte within the mapped region specified by mappedaddress.
301 Moved Permanently Community dedicated to discussion about the national security agency's reverse engineering framework, ghidra. Create a byte mapped memory block and add it to this memory. each byte address within the resulting memory block will correspond to a byte within the mapped region specified by mappedaddress.

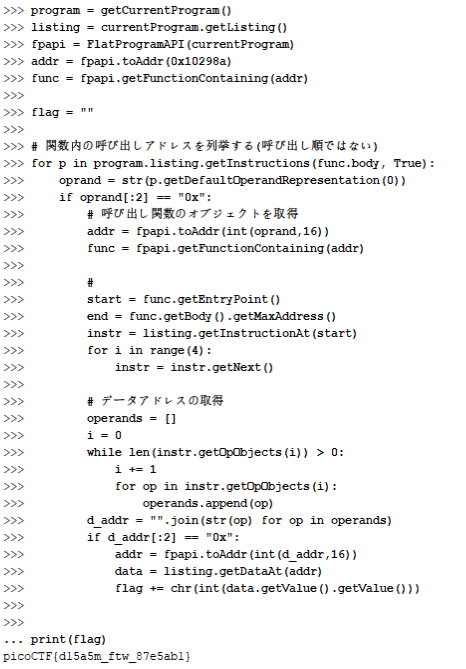
Github Syscall7 Ghidra Scripts Ghidra Scripts
Comments are closed.