Sankey Tech Talks Post Quantum Cryptographic Protocol

Hybrid Cryptographic Solutions Secure Quantum By Applied Quantum Discover how to safeguard your privacy from future supercomputers! watch our sankians pallavi shewale & ankita thakkar sharing about a new protocol that will. Our team worked with academic and industry partners on four candidates for cryptography systems that we believed could both withstand quantum computer capabilities, while still working with existing protocols.

Tech Making Messaging Safer With Post Quantum Cryptographic It is the first messaging protocol which reached level 3 security, which means it is built to defend against most sophisticated quantum attacks. There are algorithms secure enough to be out of reach for both classical and future quantum machines, called post quantum cryptography, but transitioning to these is a work in progress. This follow up dives into how forward thinking enterprises are already operationalizing pqc in their day to day security efforts—and how your team can take practical steps to do the same before quantum risk becomes quantum reality. Iot systems face unique challenges in implementing post quantum cryptography (pqc) and crypto agility to ensure long term security and resilience in the quantum era.
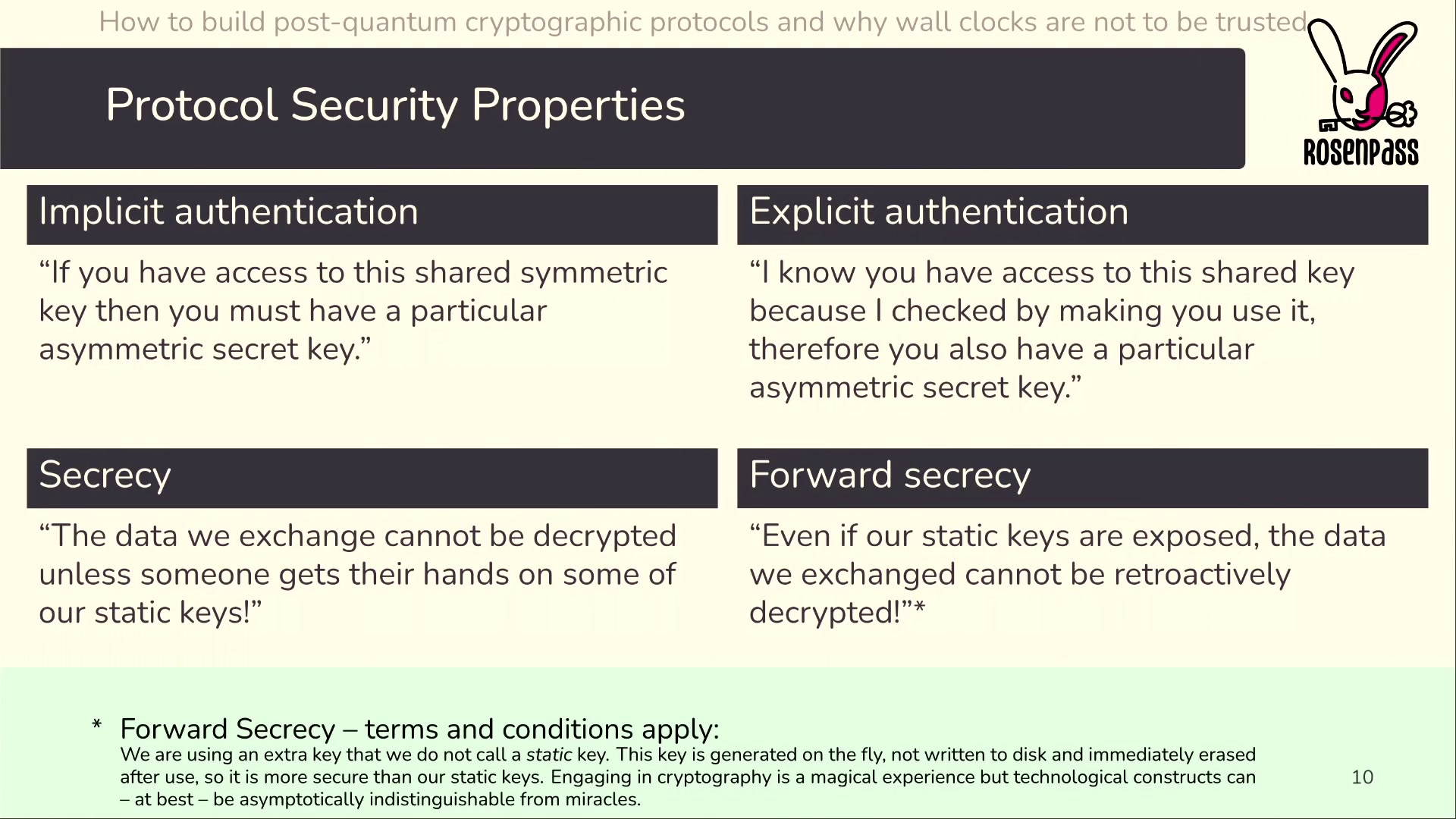
How To Build Post Quantum Cryptographic Protocols And Why Wall Clocks This follow up dives into how forward thinking enterprises are already operationalizing pqc in their day to day security efforts—and how your team can take practical steps to do the same before quantum risk becomes quantum reality. Iot systems face unique challenges in implementing post quantum cryptography (pqc) and crypto agility to ensure long term security and resilience in the quantum era. The study being done in the field of post quantum cryptography includes a wide range of tasks, such as creating new algorithms and protocols, putting them into practice, and teaching others about them. Nist’s post quantum cryptography (pqc) project leads the national and global effort to secure electronic information against the future threat of quantum computers—machines that may be years or decades away but could eventually break many of today’s widely used cryptographic systems. Post quantum cryptography (pqc) has become the primary defense against the vulnerabilities that large scale quantum computing introduces to traditional cryptographic systems. As we transition to sixth generation (6g) networks, ensuring robust, quantum resistant security through post quantum cryptography (pqc) and quantum communication is not just essential—it is foundational to the trustworthiness and longevity of future communication systems.

Post Quantum Cryptography Securing Data In The Quantum Era The study being done in the field of post quantum cryptography includes a wide range of tasks, such as creating new algorithms and protocols, putting them into practice, and teaching others about them. Nist’s post quantum cryptography (pqc) project leads the national and global effort to secure electronic information against the future threat of quantum computers—machines that may be years or decades away but could eventually break many of today’s widely used cryptographic systems. Post quantum cryptography (pqc) has become the primary defense against the vulnerabilities that large scale quantum computing introduces to traditional cryptographic systems. As we transition to sixth generation (6g) networks, ensuring robust, quantum resistant security through post quantum cryptography (pqc) and quantum communication is not just essential—it is foundational to the trustworthiness and longevity of future communication systems.
Comments are closed.