S 190 Secure Computation

Secure Computation Pdf Questions should be sent to the iacr conference chat room. Explore the fundamentals and advanced concepts of secure computation in this comprehensive lecture. delve into resource restricted cryptography, efficient constructions, and succinct non interactive secure computation.
Secure Computation Nec This course will discuss about how using various cryptographic primitives, one can do computation on distributed and sensitive data, also known as secure multi party computation (mpc), which is one of the most fundamental problems in cryptography as well as distributed computing. Lecture 11: secure multiparty computation instructor: akshayaram srinivasan scribe: vedic sharma. The theoretical projects will involve answering deep and exiciting theoretical questions in the secure computation literature. on the other hand, the practical projects will involve implementing and improving challenging practical secure computation tasks. Secure multi party computation enables a group of parties to compute a function while jointly keeping their private inputs secret. the term “secure” indicates the latter property where the.
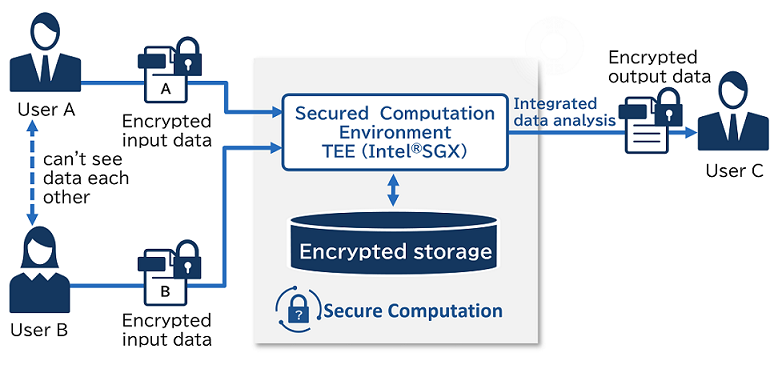
Secure Computation Nec The theoretical projects will involve answering deep and exiciting theoretical questions in the secure computation literature. on the other hand, the practical projects will involve implementing and improving challenging practical secure computation tasks. Secure multi party computation enables a group of parties to compute a function while jointly keeping their private inputs secret. the term “secure” indicates the latter property where the. Ntt's secure multi party computation is built on a secret sharing scheme that complies with iso international standards, combined with advanced cryptographic protocols for privacy preserving data processing. It is also referred to as secure function evaluation (sfe), and is concerned with the question: 'can two party computation be achieved more efficiently and under weaker security assumptions than general mpc?. Generic constructions for secure computation, including secure protocols for both semi honest and malicious models, and state of the art construction techniques, are discussed in section 3. To recover f(x, y), we therefore somehow need a method to do fhe decryption within key equation, but without actually revealing any information about the fhe secret key, as that would compromise bob’s security.
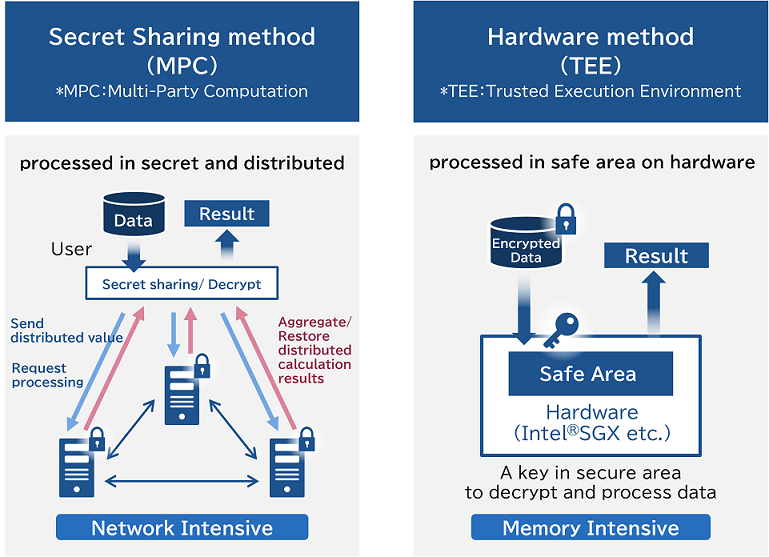
Secure Computation Nec Ntt's secure multi party computation is built on a secret sharing scheme that complies with iso international standards, combined with advanced cryptographic protocols for privacy preserving data processing. It is also referred to as secure function evaluation (sfe), and is concerned with the question: 'can two party computation be achieved more efficiently and under weaker security assumptions than general mpc?. Generic constructions for secure computation, including secure protocols for both semi honest and malicious models, and state of the art construction techniques, are discussed in section 3. To recover f(x, y), we therefore somehow need a method to do fhe decryption within key equation, but without actually revealing any information about the fhe secret key, as that would compromise bob’s security.
Comments are closed.