Rsa Examples Pdf Encryption Applied Mathematics

Rsa Examples Pdf Cryptography Applied Mathematics Rsa examples free download as pdf file (.pdf), text file (.txt) or read online for free. the document provides an example of encrypting a message using rsa with a modulus of 2537 and an encryption exponent of 13. Hu abstract. in the field of cryptography, which aims to ensure secure message communica tion, the rsa public key cryptosystem is the oldest widely applied secure data transmi. sion method. in this expository paper, we provide a historical and technical overview of the rsa .

The Mathematics Of Rsa Encryption Pptx We first go through the steps for producing the necessary numbers for encryption and decryption in rsa. we will then go through a simple example to understand how the processes of encryption and decryption are implemented. One of the ideas behind the rsa cryptography is that it is very hard to factor large integers, even if you use a computer. you have learnt how to factor small numbers, but how would you find the prime factorization of an integer n with 200 digits?. Our research on the rsa algorithm brings a significant amount of mathematics to bear. for instance, we have needed to understand how best to use the algorithm to establish keys and sign messages. This chapter explores the mathematics behind the rsa cryptosystem including the encryp tion, decryption and signature schemes of rsa. we give a survey of the main methods used in attacks against the rsa cryptosystem.
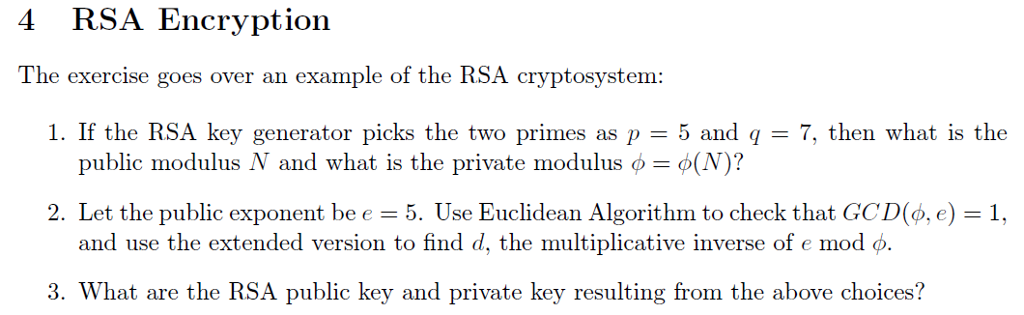
Solved 4 Rsa Encryption The Exercise Goes Over An Example Of Chegg Our research on the rsa algorithm brings a significant amount of mathematics to bear. for instance, we have needed to understand how best to use the algorithm to establish keys and sign messages. This chapter explores the mathematics behind the rsa cryptosystem including the encryp tion, decryption and signature schemes of rsa. we give a survey of the main methods used in attacks against the rsa cryptosystem. Despite the fact that you are not likely to use rsa for content encryption, it’s nonetheless educational to reflect on how it could be used for that purpose in the form of a block cipher. But with quantum technology quickly evolving, many of our classic mathematical techniques in cryptography are under threat. in the following discussion we will inspect the mathematics behind the most common encryption mechanism: rsa. Imagine that a person x wants to send a carefully encrypted message to another person y , say. x will look in a directory which publishes the public key of various people including y . They posted one of the first public key encryption messages using a 129 digit number which later became known as rsa 129. they offered a $100 prize and remarked that using technology and factoring techniques available at that time, it would take 40 quadrillion years to crack.
Application Of Discrete Mathematics Rsa Algorithm Report My Computer Despite the fact that you are not likely to use rsa for content encryption, it’s nonetheless educational to reflect on how it could be used for that purpose in the form of a block cipher. But with quantum technology quickly evolving, many of our classic mathematical techniques in cryptography are under threat. in the following discussion we will inspect the mathematics behind the most common encryption mechanism: rsa. Imagine that a person x wants to send a carefully encrypted message to another person y , say. x will look in a directory which publishes the public key of various people including y . They posted one of the first public key encryption messages using a 129 digit number which later became known as rsa 129. they offered a $100 prize and remarked that using technology and factoring techniques available at that time, it would take 40 quadrillion years to crack.

Rsa Pdf Teaching Methods Materials Science Mathematics Imagine that a person x wants to send a carefully encrypted message to another person y , say. x will look in a directory which publishes the public key of various people including y . They posted one of the first public key encryption messages using a 129 digit number which later became known as rsa 129. they offered a $100 prize and remarked that using technology and factoring techniques available at that time, it would take 40 quadrillion years to crack.
Solved 1 Implement Rsa Encryption Decryption Algorithm Chegg
Comments are closed.