Rsa Algorithm Step By Step Example Youtube
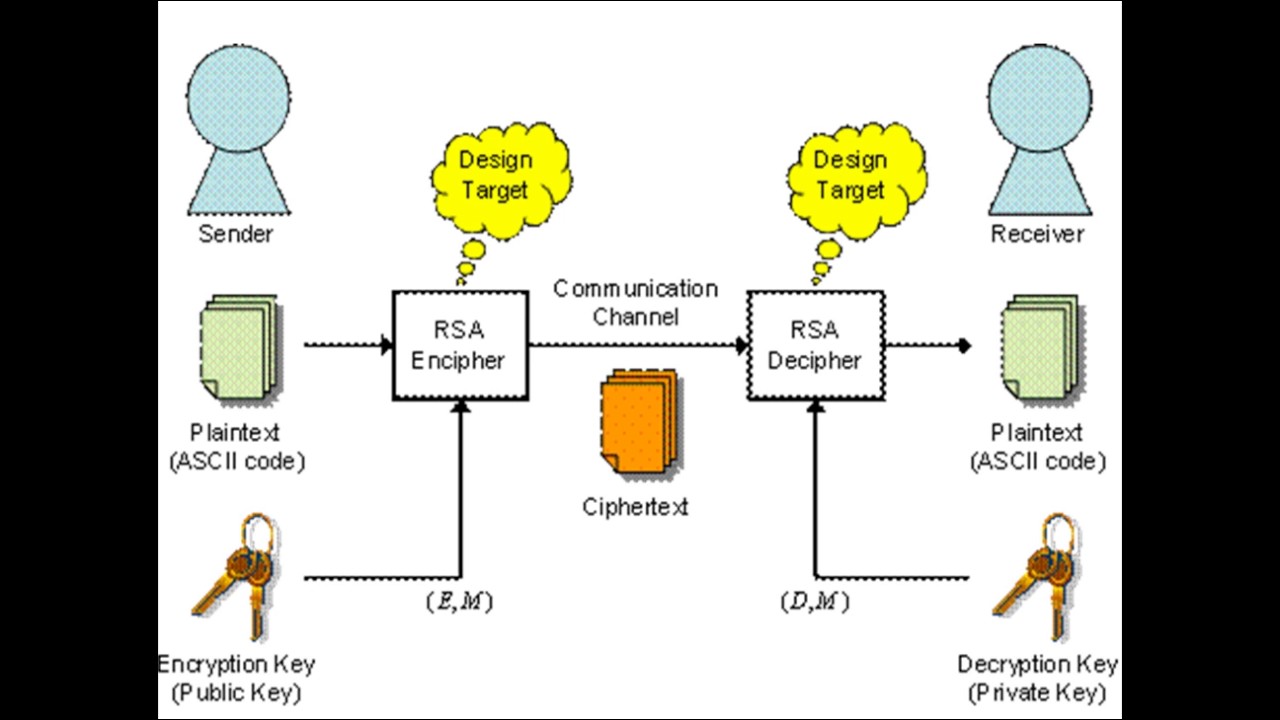
Rsa Algorithm Youtube By the end of this video, you’ll have a solid understanding of how rsa works, from key generation to encryption and decryption, with a practical example of how alice can send a secure message. Learn about the rsa algorithm, a fundamental public key encryption method, in this 23 minute video tutorial. explore the step by step process of generating public and private keys, including selecting prime numbers, calculating necessary values, and applying the keys for encryption and decryption.

Rsa Algorithm Youtube Using intuitive explanations and helpful visuals, i'll simplify the complexities, allowing you to fully comprehend how this robust encryption method operates. 💻 getting hands on: theory meets. Rsa encryption is used in many public and private key encryption systems. this video will show public and private key examples and then the mechanics of using the rsa algorithm. In this video, we provide a step by step explanation of how rsa encryption works, making this essential cryptographic technique easy to understand for everyone. In this video, you will learn the rsa algorithm in a simple and structured way with a step by step numerical example.
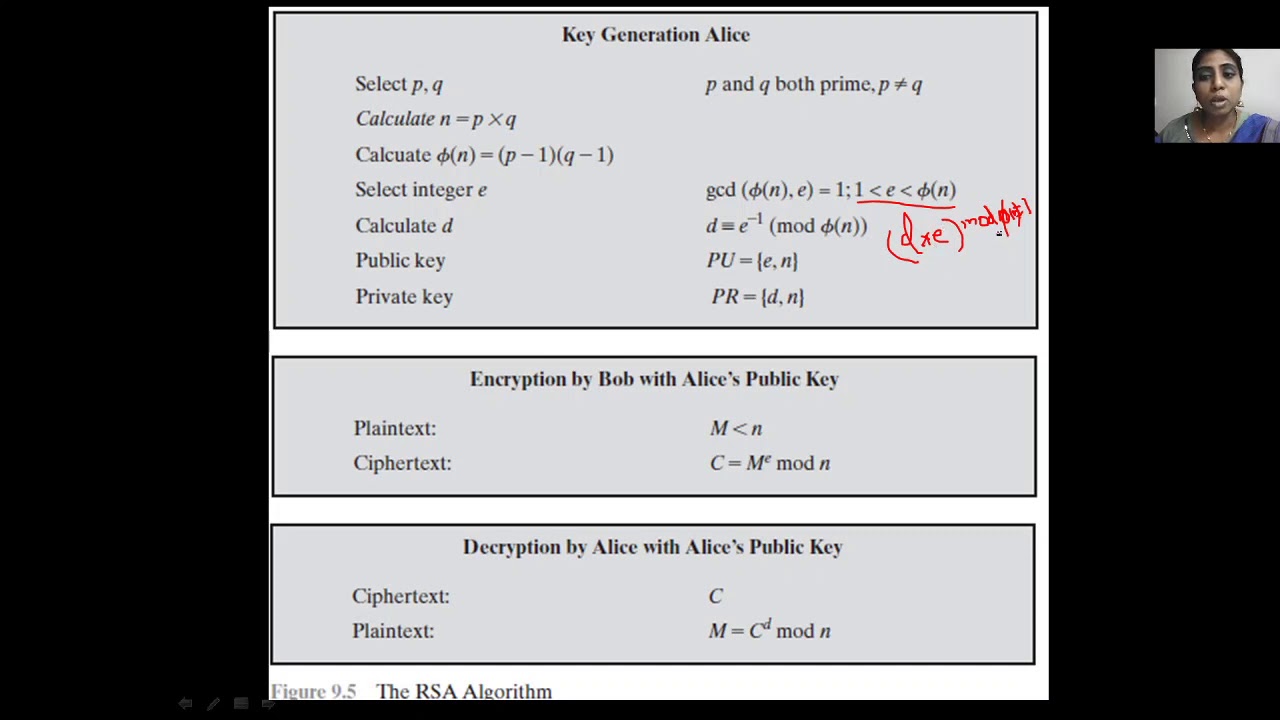
Rsa Algorithm Youtube In this video, we provide a step by step explanation of how rsa encryption works, making this essential cryptographic technique easy to understand for everyone. In this video, you will learn the rsa algorithm in a simple and structured way with a step by step numerical example. In this video, we explain public–private key cryptography (asymmetric cryptography) in a simple and beginner friendly way, along with the rsa algorithm expla. We'll take you step by step through the inner workings of rsa, providing practical examples along the way to ensure a clear understanding. Ever wondered how your data stays safe online? in this video, we break down the rsa algorithm in simple terms. learn the math behind public and private keys,. Here you can see how to encrypt and decrypt using the rsa procedure step by step. the security of rsa is based on the fact that it is easy to calculate the product n n of two large prime numbers p p and q q. however, it is very difficult to determine the two primes only from the product n n.
Comments are closed.